Compare commits
1 Commits
dev
...
5e02fb99cf
| Author | SHA1 | Date | |
|---|---|---|---|
|
5e02fb99cf
|
55
.sops.yaml
Normal file
@@ -0,0 +1,55 @@
|
||||
keys:
|
||||
- &users
|
||||
- &tux age14vktfes95f33vuefwnmuvryas7az04u76dsgyhfvsx73czkvmp2q7njkl4
|
||||
|
||||
- &hosts
|
||||
- &sirius age1f860dfewlx5jtt9ejr47gywx70p3dmyc8mat29gpr75psljwjv8q5xyxkq
|
||||
- &canopus age1udt3cssu7ahdrhsvckt8450rswrr6mknn36xpq74dkfp9lpajvnq84kdzj
|
||||
- &homelab age1jg642q775gmnmxeu29gcf3lph8vem4xr8t84cxe809dpd0myrussh49h60
|
||||
- &arcturus age1zsl5d4vj6gl3h96y5p53sq5y4vr4vtlwp727h7rp9a4xfkxm53lqrh6r50
|
||||
- &alpha age1zujp5gxy7suv8ysnygv43cmzuvv36nxfg0ch7r3xg2emc6fz3vmqqujheq
|
||||
- &vega age1ydkclhk9kwqdq74utesqdfupt43lz64d5k65gz2z9uyljcqq9fcq3hv28l
|
||||
- &capella age1y4luzn2jls7rvgphej23srvdlx563lxq29tvf66vhwwzaf7c3f3qzvresh
|
||||
|
||||
creation_rules:
|
||||
- path_regex: hosts/common/secrets.yaml$
|
||||
key_groups:
|
||||
- age:
|
||||
- *tux
|
||||
- *sirius
|
||||
- *canopus
|
||||
- *homelab
|
||||
- *arcturus
|
||||
- *alpha
|
||||
- *vega
|
||||
- *capella
|
||||
- path_regex: hosts/sirius/secrets.yaml$
|
||||
key_groups:
|
||||
- age:
|
||||
- *tux
|
||||
- *sirius
|
||||
- path_regex: hosts/canopus/secrets.yaml$
|
||||
key_groups:
|
||||
- age:
|
||||
- *tux
|
||||
- *canopus
|
||||
- path_regex: hosts/arcturus/secrets.yaml$
|
||||
key_groups:
|
||||
- age:
|
||||
- *tux
|
||||
- *arcturus
|
||||
- path_regex: hosts/alpha/secrets.yaml$
|
||||
key_groups:
|
||||
- age:
|
||||
- *tux
|
||||
- *alpha
|
||||
- path_regex: hosts/capella/secrets.yaml$
|
||||
key_groups:
|
||||
- age:
|
||||
- *tux
|
||||
- *capella
|
||||
- path_regex: hosts/homelab/secrets.yaml$
|
||||
key_groups:
|
||||
- age:
|
||||
- *tux
|
||||
- *homelab
|
||||
154
README.md
@@ -22,132 +22,48 @@
|
||||
|
||||
## Hosts
|
||||
|
||||
| | Hostname | Board | CPU | RAM | GPU | Purpose |
|
||||
| --- | ---------- | ----------------- | ------------------ | ----- | ------------------------- | -------------------------------------------------------------------------------- |
|
||||
| 🖥️ | `sirius` | MSI X570-A Pro | Ryzen 7 5700X3D | 64GB | RTX 3080 TI + RTX 3060 TI | Triple-monitor desktop running Windows Subsystem for Linux. |
|
||||
| 💻 | `canopus` | Asus Zephyrus G15 | Ryzen 9 5900HS | 16GB | RTX 3060 | Optimized for productivity on the go and some gaming. |
|
||||
| ☁️ | `homelab` | Minisforum MS-A1 | Ryzen 7 8700G | 32GB | Radeon 780M | WIP |
|
||||
| ☁️ | `arcturus` | KVM | 4 Core | 8GB | | Primary server responsible for exposing my homelab applications to the internet. |
|
||||
| ☁️ | `alpha` | KVM | 4 Core | 4GB | | Monitors uptime and health status of all services across the infrastructure. |
|
||||
| 🥔 | `vega` | Raspberry Pi 3B+ | Cortex A53 | 1GB | | Running AdGuard Home for network-wide ad blocking. |
|
||||
| 📱 | `capella` | Samsung S25 Ultra | Snapdragon 8 Elite | 12GB | Adreno 830 | Primary mobile for daily usage. (Locked) |
|
||||
| 📱 | `rigel` | Motorola Edge 30 | Snapdragon 778G+ | 8GB | Adreno 642L | Secondary mobile for some fun. (Rooted) |
|
||||
| ☁️ | `node` | ASRock B565D4 | Ryzen 9 5950X | 128GB | | Running Ethereum and BSC nodes. |
|
||||
| | Hostname | Board | CPU | RAM | GPU | Purpose |
|
||||
| --- | ---------- | ----------------- | ------------------ | ---- | ------------------------- | ---------------------------------------------------------------------------------- |
|
||||
| 🖥️ | `sirius` | MSI X570-A Pro | Ryzen 7 5700X3D | 64GB | RTX 3080 TI + RTX 3060 TI | Triple-monitor desktop running Windows Subsystem for Linux. |
|
||||
| 💻 | `canopus` | Asus Zephyrus G15 | Ryzen 9 5900HS | 16GB | RTX 3060 | Optimized for productivity on the go and some gaming. |
|
||||
| ☁️ | `homelab` | Minisforum MS-A1 | Ryzen 7 8700G | 32GB | Radeon 780M | WIP |
|
||||
| ☁️ | `arcturus` | KVM | 4 Core | 8GB | | Primary server responsible for exposing my homelab applications to the internet. |
|
||||
| ☁️ | `alpha` | KVM | 4 Core | 4GB | | Monitors uptime and health status of all services across the infrastructure. |
|
||||
| 🥔 | `vega` | Raspberry Pi 3B+ | Cortex A53 | 1GB | | Running AdGuard Home for network-wide ad blocking. |
|
||||
| 📱 | `capella` | Samsung S25 Ultra | Snapdragon 8 Elite | 12GB | Adreno 830 | Primary mobile for daily usage. (Locked) |
|
||||
| 📱 | `rigel` | Motorola Edge 30 | Snapdragon 778G+ | 8GB | Adreno 642L | Secondary mobile for some fun. (Rooted) |
|
||||
| ☁️ | `node` | KVM | i9-13900 | 64GB | | Running Ethereum and BSC nodes. Currently in the process of migrating from Ubuntu. |
|
||||
|
||||
## Installation
|
||||
|
||||
> [!NOTE]
|
||||
> This will get your base system ready, but keep in mind that many things might not work correctly — such as monitor resolution, font size, and more.
|
||||
Boot into NixOS bootable USB and then enter the following commands
|
||||
|
||||
### Prerequisites
|
||||
|
||||
Boot into the NixOS bootable USB before proceeding with the installation steps.
|
||||
|
||||
### Installation Steps
|
||||
|
||||
#### 1. Clone the repository
|
||||
|
||||
```bash
|
||||
```
|
||||
# Clone this repositry
|
||||
git clone https://github.com/tuxdotrs/nix-config.git
|
||||
|
||||
# Navigate to the repository directory
|
||||
cd nix-config
|
||||
```
|
||||
|
||||
#### 2. Gain root privileges
|
||||
# Install disko for disk partitioning
|
||||
nix-shell -p disko
|
||||
|
||||
```bash
|
||||
sudo su
|
||||
|
||||
```
|
||||
|
||||
#### 3. Set up disk partitioning
|
||||
|
||||
Install the required tools:
|
||||
|
||||
```bash
|
||||
nix-shell -p disko neovim
|
||||
```
|
||||
|
||||
Partition your disk using disko. **This will wipe your drive.** Replace `DISK_PATH` with your actual disk path (e.g., `/dev/vda` or `/dev/nvme0n1`):
|
||||
|
||||
```bash
|
||||
# Partition the disk and make sure to replace DISK_PATH (eg. /dev/vda)
|
||||
disko --mode disko ./hosts/canopus/disko.nix --arg device '"DISK_PATH"'
|
||||
```
|
||||
|
||||
#### 4. Configure your disk
|
||||
|
||||
Edit the configuration file:
|
||||
|
||||
```bash
|
||||
nvim ./hosts/canopus/default.nix
|
||||
```
|
||||
|
||||
In the imports statement, replace:
|
||||
|
||||
```nix
|
||||
(import ./disko.nix {device = "/dev/nvme0n1";})
|
||||
```
|
||||
|
||||
with:
|
||||
|
||||
```nix
|
||||
(import ./disko.nix {device = "DISK_PATH";})
|
||||
```
|
||||
|
||||
Make sure to replace `DISK_PATH` with your actual disk path.
|
||||
|
||||
#### 5. Generate hardware configuration
|
||||
|
||||
```bash
|
||||
# Generate the hardware.nix file for your system
|
||||
nixos-generate-config --no-filesystems --root /mnt
|
||||
```
|
||||
|
||||
Copy the generated hardware configuration to the repository:
|
||||
|
||||
```bash
|
||||
# Replace the hardware.nix with generated one
|
||||
cp /mnt/etc/nixos/hardware-configuration.nix ./hosts/canopus/hardware.nix
|
||||
```
|
||||
|
||||
#### 6. Install NixOS
|
||||
|
||||
```bash
|
||||
# Install
|
||||
nixos-install --root /mnt --flake .#canopus
|
||||
```
|
||||
|
||||
#### 7. Enter into the new system
|
||||
|
||||
```bash
|
||||
nixos-enter --root /mnt
|
||||
```
|
||||
|
||||
#### 8. Set up directories and permissions
|
||||
|
||||
```bash
|
||||
mkdir -p /persist/home
|
||||
chown -R tux:users /persist/home
|
||||
```
|
||||
|
||||
#### 9. Set passwords
|
||||
|
||||
Set the root password:
|
||||
|
||||
```bash
|
||||
passwd root
|
||||
```
|
||||
|
||||
Set the user password:
|
||||
|
||||
```bash
|
||||
passwd tux
|
||||
```
|
||||
|
||||
#### 10. Reboot
|
||||
|
||||
```bash
|
||||
# Reboot to your beautiful DE
|
||||
reboot
|
||||
```
|
||||
|
||||
Your NixOS system should now boot into a beautiful DE.
|
||||
|
||||
## Components
|
||||
|
||||
| | Wayland | Xorg |
|
||||
@@ -155,30 +71,16 @@ Your NixOS system should now boot into a beautiful DE.
|
||||
| DM | ly | ly |
|
||||
| WM/DE | Hyprland | AwesomeWM |
|
||||
| Compositor | Hyprland | Picom (Jonaburg) |
|
||||
| Bar | tPanel | Wibar |
|
||||
| Bar | Astal | Wibar |
|
||||
| Hotkeys | Hyprland | Awful |
|
||||
| Launcher | tPanel | Rofi |
|
||||
| Notifications | tPanel | Naughty |
|
||||
| Terminal | Wezterm | Wezterm |
|
||||
| Launcher | Astal | Rofi |
|
||||
| Notifications | Astal | Naughty |
|
||||
| Terminal | Ghostty | Wezterm |
|
||||
| Editor | Neovim | Neovim |
|
||||
|
||||
## Showcase
|
||||
|
||||
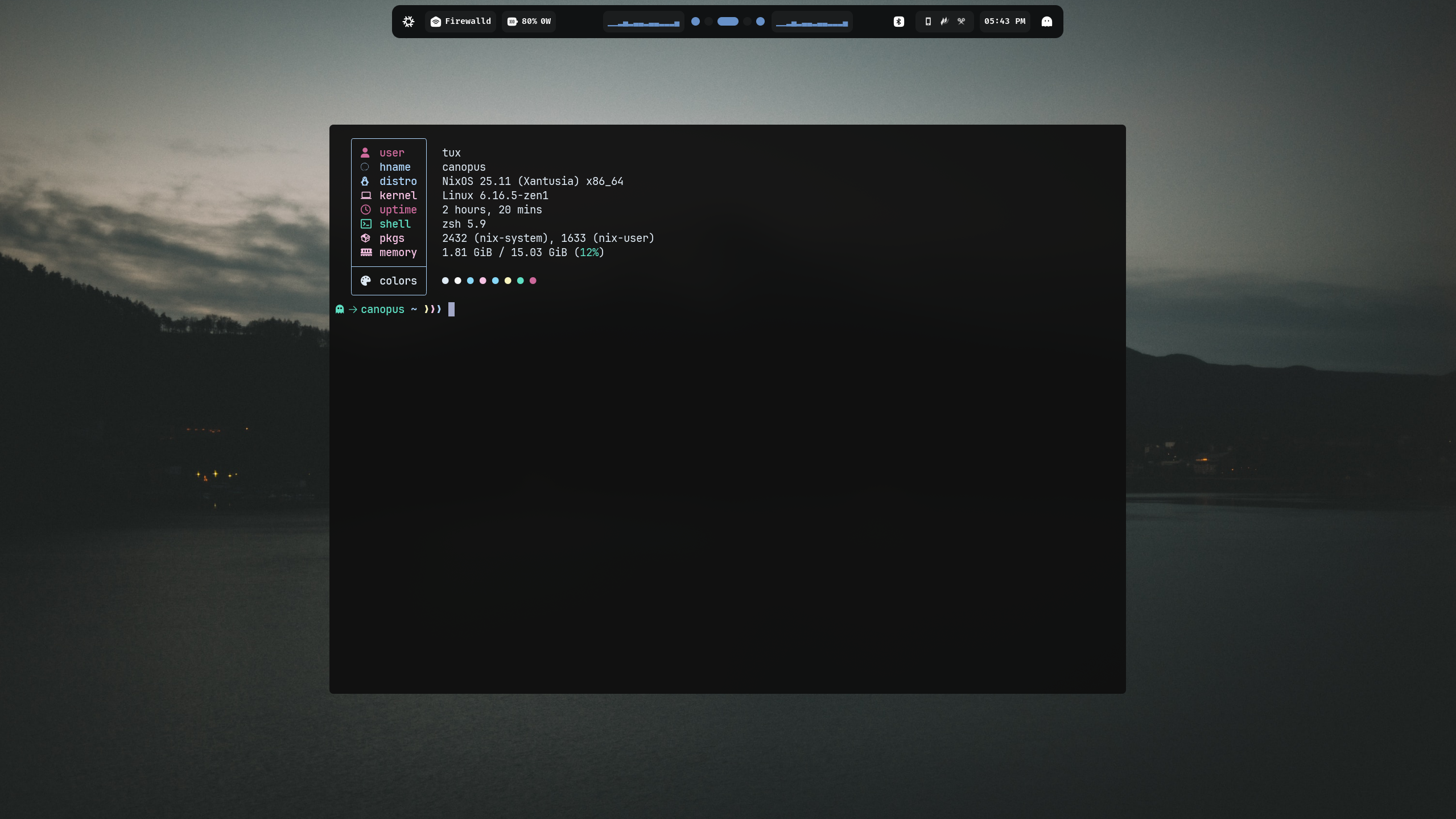
### Desktop Hyprland
|
||||
|
||||
|
||||
|
||||
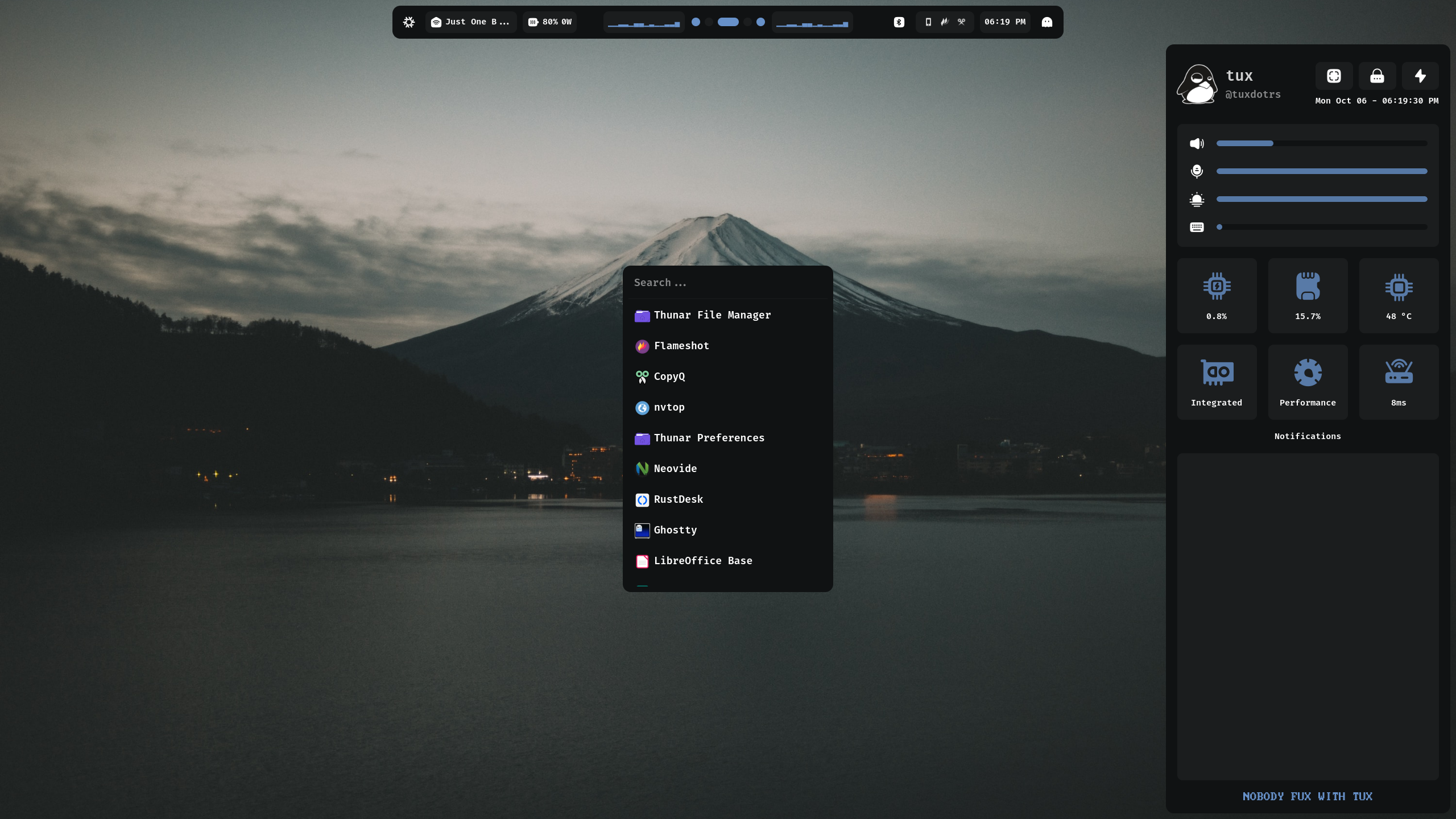
### tPanel
|
||||
|
||||
|
||||
|
||||
### Workflow
|
||||
|
||||

|
||||
|
||||
## Showcase
|
||||
|
||||
### Desktop AwesomeWM
|
||||
### Desktop
|
||||
|
||||

|
||||
|
||||
|
||||
|
Before Width: | Height: | Size: 3.2 MiB After Width: | Height: | Size: 3.2 MiB |
|
Before Width: | Height: | Size: 2.6 MiB After Width: | Height: | Size: 2.6 MiB |
|
Before Width: | Height: | Size: 439 KiB After Width: | Height: | Size: 439 KiB |
|
Before Width: | Height: | Size: 1.6 MiB |
|
Before Width: | Height: | Size: 1.9 MiB |
|
Before Width: | Height: | Size: 642 KiB |
|
Before Width: | Height: | Size: 487 KiB After Width: | Height: | Size: 487 KiB |
|
Before Width: | Height: | Size: 559 KiB After Width: | Height: | Size: 559 KiB |
|
Before Width: | Height: | Size: 574 KiB After Width: | Height: | Size: 574 KiB |
|
Before Width: | Height: | Size: 645 KiB After Width: | Height: | Size: 645 KiB |
1829
flake.lock
generated
Executable file
170
flake.nix
Executable file
@@ -0,0 +1,170 @@
|
||||
{
|
||||
description = "tux's Nix Flake";
|
||||
|
||||
outputs = {
|
||||
self,
|
||||
nixpkgs,
|
||||
deploy-rs,
|
||||
...
|
||||
} @ inputs: let
|
||||
inherit (self) outputs;
|
||||
inherit (inputs.nixpkgs.lib) nixosSystem;
|
||||
inherit (inputs.nix-on-droid.lib) nixOnDroidConfiguration;
|
||||
forAllSystems = nixpkgs.lib.genAttrs [
|
||||
"x86_64-linux"
|
||||
"aarch64-linux"
|
||||
];
|
||||
username = "tux";
|
||||
email = "t@tux.rs";
|
||||
|
||||
mkNixOSConfig = host: {
|
||||
specialArgs = {inherit inputs outputs username email;};
|
||||
modules = [./hosts/${host}];
|
||||
};
|
||||
|
||||
mkDroidConfig = host: {
|
||||
pkgs = import nixpkgs {system = "aarch64-linux";};
|
||||
extraSpecialArgs = {inherit inputs outputs username email;};
|
||||
modules = [./hosts/${host}];
|
||||
};
|
||||
|
||||
mkNixOSNode = hostname: {
|
||||
inherit hostname;
|
||||
profiles.system = {
|
||||
user = "root";
|
||||
path = deploy-rs.lib.x86_64-linux.activate.nixos self.nixosConfigurations.${hostname};
|
||||
};
|
||||
};
|
||||
|
||||
activateNixOnDroid = configuration:
|
||||
deploy-rs.lib.aarch64-linux.activate.custom
|
||||
configuration.activationPackage
|
||||
"${configuration.activationPackage}/activate";
|
||||
|
||||
mkDroidNode = hostname: {
|
||||
inherit hostname;
|
||||
profiles.system = {
|
||||
sshUser = "nix-on-droid";
|
||||
user = "nix-on-droid";
|
||||
magicRollback = true;
|
||||
sshOpts = ["-p" "8033"];
|
||||
path = activateNixOnDroid self.nixOnDroidConfigurations.${hostname};
|
||||
};
|
||||
};
|
||||
in {
|
||||
packages = forAllSystems (system: import ./pkgs nixpkgs.legacyPackages.${system});
|
||||
formatter = forAllSystems (system: nixpkgs.legacyPackages.${system}.alejandra);
|
||||
|
||||
# Custom packages and modifications, exported as overlays
|
||||
overlays = import ./overlays {inherit inputs;};
|
||||
|
||||
# NixOS configuration entrypoint
|
||||
# 'nixos-rebuild switch --flake .#your-hostname'
|
||||
nixosConfigurations = {
|
||||
arcturus = nixosSystem (mkNixOSConfig "arcturus");
|
||||
canopus = nixosSystem (mkNixOSConfig "canopus");
|
||||
alpha = nixosSystem (mkNixOSConfig "alpha");
|
||||
sirius = nixosSystem (mkNixOSConfig "sirius");
|
||||
vega = nixosSystem (mkNixOSConfig "vega");
|
||||
vps = nixosSystem (mkNixOSConfig "vps");
|
||||
isoImage = nixosSystem (mkNixOSConfig "isoImage");
|
||||
homelab = nixosSystem (mkNixOSConfig "homelab");
|
||||
};
|
||||
|
||||
# NixOnDroid configuration entrypoint
|
||||
# 'nix-on-droid switch --flake .#your-hostname'
|
||||
nixOnDroidConfigurations = {
|
||||
capella = nixOnDroidConfiguration (mkDroidConfig "capella");
|
||||
rigel = nixOnDroidConfiguration (mkDroidConfig "rigel");
|
||||
};
|
||||
|
||||
deploy = {
|
||||
nodes = {
|
||||
arcturus = mkNixOSNode "arcturus";
|
||||
canopus = mkNixOSNode "canopus";
|
||||
alpha = mkNixOSNode "alpha";
|
||||
sirius = mkNixOSNode "sirius";
|
||||
vega = mkNixOSNode "vega";
|
||||
homelab = mkNixOSNode "homelab";
|
||||
capella = mkDroidNode "capella";
|
||||
rigel = mkDroidNode "rigel";
|
||||
};
|
||||
};
|
||||
checks = builtins.mapAttrs (system: deployLib: deployLib.deployChecks self.deploy) deploy-rs.lib;
|
||||
};
|
||||
|
||||
inputs = {
|
||||
nixpkgs.url = "github:nixos/nixpkgs/nixos-unstable";
|
||||
nixpkgs-stable.url = "github:nixos/nixpkgs/release-24.11";
|
||||
nixos-wsl = {
|
||||
url = "github:nix-community/nixos-wsl";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
home-manager = {
|
||||
url = "github:nix-community/home-manager";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
nix-vscode-extensions = {
|
||||
url = "github:nix-community/nix-vscode-extensions";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
wezterm-flake = {
|
||||
url = "github:wez/wezterm/main?dir=nix";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
disko = {
|
||||
url = "github:nix-community/disko";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
nix-secrets = {
|
||||
url = "git+ssh://git@github.com/tuxdotrs/nix-secrets.git?shallow=1";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
nix-on-droid = {
|
||||
url = "github:nix-community/nix-on-droid/release-24.05";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
inputs.home-manager.follows = "home-manager";
|
||||
};
|
||||
tawm = {
|
||||
url = "github:tuxdotrs/tawm";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
tnvim = {
|
||||
url = "github:tuxdotrs/tnvim";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
trok = {
|
||||
url = "github:tuxdotrs/trok";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
tpanel = {
|
||||
url = "github:tuxdotrs/tpanel";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
tfolio = {
|
||||
url = "git+ssh://git@github.com/tuxdotrs/tfolio.git";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
cyber-tux = {
|
||||
url = "git+ssh://git@github.com/tuxdotrs/cyber-tux.git";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
nix-index-database = {
|
||||
url = "github:nix-community/nix-index-database";
|
||||
inputs.nixpkgs.follows = "nixpkgs";
|
||||
};
|
||||
hyprland.url = "github:hyprwm/Hyprland";
|
||||
hyprland-plugins = {
|
||||
url = "github:hyprwm/hyprland-plugins";
|
||||
inputs.hyprland.follows = "hyprland";
|
||||
};
|
||||
ghostty.url = "github:ghostty-org/ghostty";
|
||||
nixos-hardware.url = "github:nixos/nixos-hardware";
|
||||
nixpkgs-f2k.url = "github:moni-dz/nixpkgs-f2k";
|
||||
nur.url = "github:nix-community/nur";
|
||||
sops-nix.url = "github:Mic92/sops-nix";
|
||||
impermanence.url = "github:nix-community/impermanence";
|
||||
deploy-rs.url = "github:serokell/deploy-rs";
|
||||
nixcord.url = "github:kaylorben/nixcord";
|
||||
};
|
||||
}
|
||||
163
hosts/alpha/default.nix
Normal file
@@ -0,0 +1,163 @@
|
||||
{
|
||||
modulesPath,
|
||||
inputs,
|
||||
username,
|
||||
lib,
|
||||
email,
|
||||
config,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
(modulesPath + "/installer/scan/not-detected.nix")
|
||||
(modulesPath + "/profiles/qemu-guest.nix")
|
||||
inputs.disko.nixosModules.default
|
||||
(import ./disko.nix {device = "/dev/vda";})
|
||||
|
||||
../common
|
||||
../../modules/nixos/selfhosted/uptime-kuma.nix
|
||||
];
|
||||
|
||||
tux.services.openssh.enable = true;
|
||||
tux.services.openssh.ports = [23];
|
||||
|
||||
tux.services.tfolio.enable = true;
|
||||
|
||||
tux.services.nginxStreamProxy = {
|
||||
enable = true;
|
||||
upstreamServers = inputs.nix-secrets.proxy-servers;
|
||||
};
|
||||
|
||||
sops.secrets = {
|
||||
borg_encryption_key = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
"cloudflare_credentials/email" = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
"cloudflare_credentials/dns_api_token" = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
};
|
||||
|
||||
nixpkgs = {
|
||||
hostPlatform = "x86_64-linux";
|
||||
};
|
||||
|
||||
boot = {
|
||||
initrd.systemd = {
|
||||
enable = lib.mkForce true;
|
||||
|
||||
services.wipe-my-fs = {
|
||||
wantedBy = ["initrd.target"];
|
||||
after = ["initrd-root-device.target"];
|
||||
before = ["sysroot.mount"];
|
||||
unitConfig.DefaultDependencies = "no";
|
||||
serviceConfig.Type = "oneshot";
|
||||
script = ''
|
||||
mkdir /btrfs_tmp
|
||||
mount /dev/disk/by-partlabel/disk-primary-root /btrfs_tmp
|
||||
|
||||
if [[ -e /btrfs_tmp/root ]]; then
|
||||
mkdir -p /btrfs_tmp/old_roots
|
||||
timestamp=$(date --date="@$(stat -c %Y /btrfs_tmp/root)" "+%Y-%m-%-d_%H:%M:%S")
|
||||
mv /btrfs_tmp/root "/btrfs_tmp/old_roots/$timestamp"
|
||||
fi
|
||||
|
||||
delete_subvolume_recursively() {
|
||||
IFS=$'\n'
|
||||
for i in $(btrfs subvolume list -o "$1" | cut -f 9- -d ' '); do
|
||||
delete_subvolume_recursively "/btrfs_tmp/$i"
|
||||
done
|
||||
btrfs subvolume delete "$1"
|
||||
}
|
||||
|
||||
for i in $(find /btrfs_tmp/old_roots/ -maxdepth 1 -mtime +30); do
|
||||
delete_subvolume_recursively "$i"
|
||||
done
|
||||
|
||||
btrfs subvolume create /btrfs_tmp/root
|
||||
umount /btrfs_tmp
|
||||
'';
|
||||
};
|
||||
};
|
||||
|
||||
loader = {
|
||||
grub = {
|
||||
efiSupport = true;
|
||||
efiInstallAsRemovable = true;
|
||||
};
|
||||
};
|
||||
};
|
||||
|
||||
networking = {
|
||||
hostName = "alpha";
|
||||
|
||||
firewall = {
|
||||
enable = true;
|
||||
allowedTCPPorts = [80 443 22 23];
|
||||
};
|
||||
};
|
||||
|
||||
security = {
|
||||
acme = {
|
||||
acceptTerms = true;
|
||||
defaults.email = "${email}";
|
||||
certs = {
|
||||
"tux.rs" = {
|
||||
group = "nginx";
|
||||
domain = "*.tux.rs";
|
||||
extraDomainNames = ["tux.rs"];
|
||||
dnsProvider = "cloudflare";
|
||||
credentialFiles = {
|
||||
CLOUDFLARE_EMAIL_FILE = config.sops.secrets."cloudflare_credentials/email".path;
|
||||
CLOUDFLARE_DNS_API_TOKEN_FILE = config.sops.secrets."cloudflare_credentials/dns_api_token".path;
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
|
||||
users.users.nginx.extraGroups = ["acme"];
|
||||
|
||||
services = {
|
||||
nginx = {
|
||||
recommendedGzipSettings = true;
|
||||
recommendedOptimisation = true;
|
||||
recommendedProxySettings = true;
|
||||
recommendedTlsSettings = true;
|
||||
};
|
||||
};
|
||||
|
||||
programs = {
|
||||
zsh.enable = true;
|
||||
dconf.enable = true;
|
||||
};
|
||||
|
||||
programs.fuse.userAllowOther = true;
|
||||
fileSystems."/persist".neededForBoot = true;
|
||||
environment.persistence."/persist" = {
|
||||
hideMounts = true;
|
||||
directories = [
|
||||
"/var/log"
|
||||
"/var/lib/acme"
|
||||
"/var/lib/nixos"
|
||||
"/var/lib/private"
|
||||
];
|
||||
files = [
|
||||
"/etc/ssh/ssh_host_ed25519_key"
|
||||
"/etc/ssh/ssh_host_ed25519_key.pub"
|
||||
"/etc/ssh/ssh_host_rsa_key"
|
||||
"/etc/ssh/ssh_host_rsa_key.pub"
|
||||
];
|
||||
};
|
||||
|
||||
home-manager.users.${username} = {
|
||||
imports = [
|
||||
./home.nix
|
||||
];
|
||||
};
|
||||
|
||||
system.stateVersion = "24.11";
|
||||
}
|
||||
53
hosts/alpha/disko.nix
Normal file
@@ -0,0 +1,53 @@
|
||||
{device ? throw "Set this to the disk device, e.g. /dev/nvme0n1", ...}: {
|
||||
disko.devices.disk.primary = {
|
||||
inherit device;
|
||||
type = "disk";
|
||||
content = {
|
||||
type = "gpt"; # GPT partitioning scheme
|
||||
partitions = {
|
||||
boot = {
|
||||
name = "boot";
|
||||
size = "1M";
|
||||
type = "EF02";
|
||||
};
|
||||
# EFI Partition
|
||||
ESP = {
|
||||
size = "512M";
|
||||
type = "EF00";
|
||||
content = {
|
||||
type = "filesystem";
|
||||
format = "vfat";
|
||||
mountpoint = "/boot";
|
||||
mountOptions = ["defaults" "umask=0077"];
|
||||
};
|
||||
};
|
||||
# Btrfs Root Partition
|
||||
root = {
|
||||
size = "100%"; # Use remaining space
|
||||
type = "8300"; # Linux filesystem type
|
||||
content = {
|
||||
type = "btrfs";
|
||||
subvolumes = {
|
||||
"/root" = {
|
||||
mountOptions = ["compress=zstd"]; # Compression for better performance
|
||||
mountpoint = "/"; # Root subvolume
|
||||
};
|
||||
"/persist" = {
|
||||
mountOptions = ["compress=zstd"]; # Compression for persistent data
|
||||
mountpoint = "/persist"; # Persistent subvolume
|
||||
};
|
||||
"/nix" = {
|
||||
mountOptions = [
|
||||
"compress=zstd"
|
||||
"noatime"
|
||||
"noacl"
|
||||
]; # Optimize for Nix store
|
||||
mountpoint = "/nix"; # Nix subvolume
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
12
hosts/alpha/home.nix
Normal file
@@ -0,0 +1,12 @@
|
||||
{username, ...}: {
|
||||
home.persistence."/persist/home/${username}" = {
|
||||
directories = [
|
||||
"Projects"
|
||||
".ssh"
|
||||
".local/share/zsh"
|
||||
];
|
||||
allowOther = true;
|
||||
};
|
||||
|
||||
home.stateVersion = "24.11";
|
||||
}
|
||||
28
hosts/alpha/secrets.yaml
Normal file
@@ -0,0 +1,28 @@
|
||||
borg_encryption_key: ENC[AES256_GCM,data:EK1f7J4ea80K7LO16pPmkh246xmXoJEiCKzPbiRCmjQ=,iv:3vae+IAAgDx+0NPgml07kbT9kc4RpzDd1oj2Qb6ZqdM=,tag:aXj3IwzfeQ8+tGjSpq76bw==,type:str]
|
||||
cloudflare_credentials:
|
||||
email: ENC[AES256_GCM,data:w9ghChGxgV7OVeM=,iv:Qtl/pMmXGjhZ9dMRkxeyEDncGfY/YPy51eJrZ6mOgGg=,tag:oi7OoTf4TnUknblZ3lPDzQ==,type:str]
|
||||
dns_api_token: ENC[AES256_GCM,data:lMoqQs9MZ646ESJUxN2dtIopNS8P55JARk6wyfaJ8ad9ABvk268oWQ==,iv:Ez4y/kKPsRuIH9mEcpS3IU4j3kK8F6iBBFOnIf9Ck60=,tag:7I0eE8PoohH9KtiHziagrg==,type:str]
|
||||
sops:
|
||||
age:
|
||||
- recipient: age14vktfes95f33vuefwnmuvryas7az04u76dsgyhfvsx73czkvmp2q7njkl4
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSB3NjIrVVlPVW9qTU9vMlMw
|
||||
K3BtRHZaS0h0WmlmMjF3YjhHSFZtNmFzdjNZCjRKQ0UwWTc2L3NOY1AyZnR2K2hF
|
||||
QkQ4blQvd0paRHd6c3dWaU5XbmV4S28KLS0tIExtWnR0djB5WU9lajVJeU5udlBQ
|
||||
eDlMemQ1c1FkazlRaDhPUzNBcVh2bWsK544MNSGooJPKL7hxQ+yvPRROw3RER7p8
|
||||
jbUVxMp4ZD/0ut/qFrKdyvfSPDcDkUR5eBoeaeUBkMAAPL+YeIxKhQ==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1zujp5gxy7suv8ysnygv43cmzuvv36nxfg0ch7r3xg2emc6fz3vmqqujheq
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSBvWlN0bWNMZTlMM3Mvdmdn
|
||||
M2M1RzBaNUl3Qkc4Sm5QbmE3cFpuODBNakZzCk9SbjBvM25pK2pGdmRqMXd4eTJu
|
||||
ZU8vTmtSN1RYK2RmQ01QempKUG43eHMKLS0tIHVINVgvNTluS1grSm1YSHkzalMx
|
||||
SGM4ditJZFducVNEaDlJSkhuUnpxQzAKvvHbDuTQUpW+O/qtgjAFZlYc4iRRj4G1
|
||||
BP/QyzuTnpP6PuAG9pJYHx164+uS2Ftog/QnCFD0YAJdJtxaoUHzOw==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
lastmodified: "2025-07-09T19:44:56Z"
|
||||
mac: ENC[AES256_GCM,data:1sXY3aEfbsit5hGBdE7x0pbdSLnW67NRNNDTEjS1fI85TaPpMmcgrxxvEDsg1A6psRMdBwFMUIVHH/rf4rkZ9tXSmHZBFTZrTQGn09bPF9yNC0MnJXKkcNcQiQJveg986LMWFwT/WE8PWbeDh7o+ASJF+IgT+5ikq8DMBgoyK/E=,iv:Ssy66et65Oq2WwbF12ubLGk87bSv/KSruf49T7v04NY=,tag:Y89PxwRFlJUBZniS2clybw==,type:str]
|
||||
unencrypted_suffix: _unencrypted
|
||||
version: 3.10.2
|
||||
217
hosts/arcturus/default.nix
Normal file
@@ -0,0 +1,217 @@
|
||||
{
|
||||
modulesPath,
|
||||
inputs,
|
||||
username,
|
||||
lib,
|
||||
email,
|
||||
config,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
(modulesPath + "/installer/scan/not-detected.nix")
|
||||
(modulesPath + "/profiles/qemu-guest.nix")
|
||||
inputs.disko.nixosModules.default
|
||||
(import ./disko.nix {device = "/dev/vda";})
|
||||
|
||||
../common
|
||||
../../modules/nixos/virtualisation/docker.nix
|
||||
../../modules/nixos/selfhosted/postgresql.nix
|
||||
../../modules/nixos/selfhosted/headscale.nix
|
||||
../../modules/nixos/selfhosted/vaultwarden.nix
|
||||
../../modules/nixos/selfhosted/gitea.nix
|
||||
../../modules/nixos/selfhosted/plausible.nix
|
||||
../../modules/nixos/selfhosted/monitoring/grafana.nix
|
||||
../../modules/nixos/selfhosted/monitoring/loki.nix
|
||||
../../modules/nixos/selfhosted/monitoring/promtail.nix
|
||||
../../modules/nixos/selfhosted/ntfy-sh.nix
|
||||
../../modules/nixos/selfhosted/searx.nix
|
||||
../../modules/nixos/selfhosted/wakapi.nix
|
||||
../../modules/nixos/selfhosted/nextcloud.nix
|
||||
../../modules/nixos/selfhosted/silver-bullet.nix
|
||||
../../modules/nixos/selfhosted/rustdesk-server.nix
|
||||
../../modules/nixos/selfhosted/kasmweb.nix
|
||||
../../modules/nixos/selfhosted/open-webui.nix
|
||||
../../modules/nixos/selfhosted/glance
|
||||
];
|
||||
|
||||
tux.services.openssh.enable = true;
|
||||
|
||||
sops.secrets = {
|
||||
borg_encryption_key = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
searx_secret_key = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
"cloudflare_credentials/email" = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
"cloudflare_credentials/dns_api_token" = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
plausible_key = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
wakapi_salt = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
nextcloud_password = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
owner = "nextcloud";
|
||||
};
|
||||
|
||||
silver_bullet = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
"cs2_secrets/SRCDS_TOKEN" = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
"cs2_secrets/CS2_RCONPW" = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
|
||||
"cs2_secrets/CS2_PW" = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
};
|
||||
|
||||
nixpkgs = {
|
||||
hostPlatform = "x86_64-linux";
|
||||
};
|
||||
|
||||
boot = {
|
||||
kernel.sysctl = {
|
||||
"vm.swappiness" = 10;
|
||||
};
|
||||
|
||||
initrd.systemd = {
|
||||
enable = lib.mkForce true;
|
||||
|
||||
services.wipe-my-fs = {
|
||||
wantedBy = ["initrd.target"];
|
||||
after = ["initrd-root-device.target"];
|
||||
before = ["sysroot.mount"];
|
||||
unitConfig.DefaultDependencies = "no";
|
||||
serviceConfig.Type = "oneshot";
|
||||
script = ''
|
||||
mkdir /btrfs_tmp
|
||||
mount /dev/disk/by-partlabel/disk-primary-root /btrfs_tmp
|
||||
|
||||
if [[ -e /btrfs_tmp/root ]]; then
|
||||
mkdir -p /btrfs_tmp/old_roots
|
||||
timestamp=$(date --date="@$(stat -c %Y /btrfs_tmp/root)" "+%Y-%m-%-d_%H:%M:%S")
|
||||
mv /btrfs_tmp/root "/btrfs_tmp/old_roots/$timestamp"
|
||||
fi
|
||||
|
||||
delete_subvolume_recursively() {
|
||||
IFS=$'\n'
|
||||
for i in $(btrfs subvolume list -o "$1" | cut -f 9- -d ' '); do
|
||||
delete_subvolume_recursively "/btrfs_tmp/$i"
|
||||
done
|
||||
btrfs subvolume delete "$1"
|
||||
}
|
||||
|
||||
for i in $(find /btrfs_tmp/old_roots/ -maxdepth 1 -mtime +30); do
|
||||
delete_subvolume_recursively "$i"
|
||||
done
|
||||
|
||||
btrfs subvolume create /btrfs_tmp/root
|
||||
umount /btrfs_tmp
|
||||
'';
|
||||
};
|
||||
};
|
||||
|
||||
loader = {
|
||||
grub = {
|
||||
efiSupport = true;
|
||||
efiInstallAsRemovable = true;
|
||||
configurationLimit = 10;
|
||||
};
|
||||
timeout = 1;
|
||||
};
|
||||
};
|
||||
|
||||
networking = {
|
||||
hostName = "arcturus";
|
||||
|
||||
firewall = {
|
||||
enable = true;
|
||||
allowedTCPPorts = [80 443 22 3333 8081];
|
||||
};
|
||||
};
|
||||
|
||||
security = {
|
||||
acme = {
|
||||
acceptTerms = true;
|
||||
defaults.email = "${email}";
|
||||
certs = {
|
||||
"tux.rs" = {
|
||||
group = "nginx";
|
||||
domain = "*.tux.rs";
|
||||
extraDomainNames = ["tux.rs"];
|
||||
dnsProvider = "cloudflare";
|
||||
credentialFiles = {
|
||||
CLOUDFLARE_EMAIL_FILE = config.sops.secrets."cloudflare_credentials/email".path;
|
||||
CLOUDFLARE_DNS_API_TOKEN_FILE = config.sops.secrets."cloudflare_credentials/dns_api_token".path;
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
|
||||
users.users.nginx.extraGroups = ["acme"];
|
||||
|
||||
services = {
|
||||
nginx = {
|
||||
recommendedTlsSettings = true;
|
||||
recommendedBrotliSettings = true;
|
||||
recommendedOptimisation = true;
|
||||
recommendedGzipSettings = true;
|
||||
recommendedProxySettings = true;
|
||||
};
|
||||
};
|
||||
|
||||
programs.fuse.userAllowOther = true;
|
||||
fileSystems."/persist".neededForBoot = true;
|
||||
environment.persistence."/persist" = {
|
||||
hideMounts = true;
|
||||
directories = [
|
||||
"/var/log"
|
||||
"/var/lib/nixos"
|
||||
"/var/lib/acme"
|
||||
"/var/lib/postgresql"
|
||||
"/var/lib/headscale"
|
||||
"/var/lib/vaultwarden"
|
||||
"/var/lib/gitea"
|
||||
"/var/lib/clickhouse"
|
||||
"/var/lib/grafana"
|
||||
"/var/lib/promtail"
|
||||
"/var/lib/private"
|
||||
"/var/lib/nextcloud"
|
||||
"/var/lib/silverbullet"
|
||||
"/var/lib/kasmweb"
|
||||
];
|
||||
files = [
|
||||
"/etc/ssh/ssh_host_ed25519_key"
|
||||
"/etc/ssh/ssh_host_ed25519_key.pub"
|
||||
"/etc/ssh/ssh_host_rsa_key"
|
||||
"/etc/ssh/ssh_host_rsa_key.pub"
|
||||
];
|
||||
};
|
||||
|
||||
home-manager.users.${username} = {
|
||||
imports = [
|
||||
./home.nix
|
||||
];
|
||||
};
|
||||
|
||||
system.stateVersion = "24.11";
|
||||
}
|
||||
53
hosts/arcturus/disko.nix
Normal file
@@ -0,0 +1,53 @@
|
||||
{device ? throw "Set this to the disk device, e.g. /dev/nvme0n1", ...}: {
|
||||
disko.devices.disk.primary = {
|
||||
inherit device;
|
||||
type = "disk";
|
||||
content = {
|
||||
type = "gpt"; # GPT partitioning scheme
|
||||
partitions = {
|
||||
boot = {
|
||||
name = "boot";
|
||||
size = "1M";
|
||||
type = "EF02";
|
||||
};
|
||||
# EFI Partition
|
||||
ESP = {
|
||||
size = "512M";
|
||||
type = "EF00";
|
||||
content = {
|
||||
type = "filesystem";
|
||||
format = "vfat";
|
||||
mountpoint = "/boot";
|
||||
mountOptions = ["defaults" "umask=0077"];
|
||||
};
|
||||
};
|
||||
# Btrfs Root Partition
|
||||
root = {
|
||||
size = "100%"; # Use remaining space
|
||||
type = "8300"; # Linux filesystem type
|
||||
content = {
|
||||
type = "btrfs";
|
||||
subvolumes = {
|
||||
"/root" = {
|
||||
mountOptions = ["compress=zstd"]; # Compression for better performance
|
||||
mountpoint = "/"; # Root subvolume
|
||||
};
|
||||
"/persist" = {
|
||||
mountOptions = ["compress=zstd"]; # Compression for persistent data
|
||||
mountpoint = "/persist"; # Persistent subvolume
|
||||
};
|
||||
"/nix" = {
|
||||
mountOptions = [
|
||||
"compress=zstd"
|
||||
"noatime"
|
||||
"noacl"
|
||||
]; # Optimize for Nix store
|
||||
mountpoint = "/nix"; # Nix subvolume
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
13
hosts/arcturus/home.nix
Normal file
@@ -0,0 +1,13 @@
|
||||
{username, ...}: {
|
||||
home.persistence."/persist/home/${username}" = {
|
||||
directories = [
|
||||
"Projects"
|
||||
"Stuff"
|
||||
".ssh"
|
||||
".local/share/zsh"
|
||||
];
|
||||
allowOther = true;
|
||||
};
|
||||
|
||||
home.stateVersion = "24.11";
|
||||
}
|
||||
42
hosts/arcturus/secrets.yaml
Normal file
@@ -0,0 +1,42 @@
|
||||
borg_encryption_key: ENC[AES256_GCM,data:7DZQaoS2a5mPjTej25vr1aO1yAAPyXT2tf/VxKrLxF0=,iv:it8JlyEj4r4Z+qDvoEWMQlGkbVh08M/BCkGLVzRCVKQ=,tag:81gRhru8J3hkQhIbgUOgBg==,type:str]
|
||||
searx_secret_key: ENC[AES256_GCM,data:Z49PJ2gNI5CI0IfzOta+r67VNUvjoPpMVv5lajGhUMPzSy1KWZC5wIM3d02jWwCOsNjXdU5hE3j9W0rkoy5ZhFPXBJRUEv5b6IcaLA==,iv:364zGZkD2LO189nkvizl8yjedi1IgYEEQMA67SexSSI=,tag:qPqefG6jUaBOpUy6d7E++w==,type:str]
|
||||
plausible_key: ENC[AES256_GCM,data:Ynf2aJ6RLRdAkT9ltLpCXTl8zg/VESDchlf67PmKjc93rSfDgq9tFqv1q55Km2lDo7y9iLu5WyLLg24CSSwy8Q==,iv:yW5hgP4dhfkvunv3iYmXGEH9w29OOmrG4ourPagslVg=,tag:C5PVfEseP5gJdoQQL4gERQ==,type:str]
|
||||
wakapi_salt: ENC[AES256_GCM,data:Vk5Lezv0f/0ehHqXXBCsQxWFYE2KFujTfII0r7Gd1BXFrwiPEdX62aZ+9LQx7s1RTHh0n+LP/5t0cmHO/fJhGw==,iv:ZUlRwNXUCQ53Lymi9fO4qoBWjLpHVWfTnYM0Z1I6F5o=,tag:dadkEKV7paH4+qAz7Bxxqg==,type:str]
|
||||
cloudflare_credentials:
|
||||
email: ENC[AES256_GCM,data:qesgxkzUglKdYPI=,iv:2XDEoQzmtagSiILWZzJPswdhkQ+qjdZfNd+LL1nHPx8=,tag:K1F23Za2Zq78tzf0fl5zEw==,type:str]
|
||||
dns_api_token: ENC[AES256_GCM,data:ibSL4KWYhqgHjo27fiSqB1iN9NWU3/qGGuLpmiMpBf+qCuh8uxR7Yw==,iv:NapMvfUSm5rgeROK7KuxGyog8s2PW9CCKtjRG87FoCQ=,tag:/Oah7PRCe4XPts0IYt83zw==,type:str]
|
||||
nextcloud_password: ENC[AES256_GCM,data:o37mq4YHQT5pbi+cXrk=,iv:8HiDwdHTozNM2lHpgqVhdsspuifppsL2I6Z31xEnYFI=,tag:xTnfn8HcubfiQwLYIkpxjw==,type:str]
|
||||
silver_bullet: ENC[AES256_GCM,data:waEPGskjkkdX98PKzgZG1bzS+NwL6GR8kok=,iv:8a8IeXla8XSHFzjKcVY3QYUK5aFk2kPHVIRvs1y7So0=,tag:p++o6wvLtG5DbDmUusRQLg==,type:str]
|
||||
cs2_secrets:
|
||||
SRCDS_TOKEN: ENC[AES256_GCM,data:SzPz4sHDgEoioX8ylLFM6AUUS60gWYpR3ifxUD8A8IQga24t6GM0dyGDryc=,iv:XefIn9yCLPLKVRA+rZiSGUH3l6ZANIJoGRuM/3vFLIw=,tag:flEjl9c7i3XBlHJaq41QYQ==,type:str]
|
||||
CS2_RCONPW: ENC[AES256_GCM,data:ZyVeoOngZjxKR/ObYo5yJC1ViCNufuA=,iv:+fJK0sY39V/iH7OjT0AzQq6RefVzLZCDETYcAMFnZNU=,tag:IOhRUQRdffNMXa2cKZvi/w==,type:str]
|
||||
CS2_PW: ENC[AES256_GCM,data:W1Cur7YT1F/+45vmqif2JbpjVURfnfo=,iv:sBNDM2N+QWDAMculBBZtYZcM7ILEfpwkwOd7ErORQhI=,tag:XFsxTUjctZKU38RQUfJ8HQ==,type:str]
|
||||
sops:
|
||||
kms: []
|
||||
gcp_kms: []
|
||||
azure_kv: []
|
||||
hc_vault: []
|
||||
age:
|
||||
- recipient: age14vktfes95f33vuefwnmuvryas7az04u76dsgyhfvsx73czkvmp2q7njkl4
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSB6TGpVMzNDZjNQSkNDQmM3
|
||||
eXpvZDRPZW9Kbm81Z2VVUVZIckFNUC9zTEZzCmliUkNWS01YMHVRaUoxTS84VmxQ
|
||||
UDZtbkhmZmdZVWVsaHN3djkwSERGQ1kKLS0tIEh0ckhDTkQvcEM0UFI2MUVXVHI5
|
||||
WnhEdnRqazdZWmczYXYxNy9BMHdwdEUKYgB34OOezF3iF706pIfDmQ0FJEHXBbGF
|
||||
EJRNmA4Zl1AwyzkN3NSlctzvxx201T1GWL4qZeyVafRv5jQ9oSfK7g==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1zsl5d4vj6gl3h96y5p53sq5y4vr4vtlwp727h7rp9a4xfkxm53lqrh6r50
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSBHeXNrT3c1bENOK0lNZWNT
|
||||
eFBqYm1BRHBhakFQMVVIKzR0SDRDOW9jUXdBCmFIQWZRSnBlOFBralVFakQ2clNY
|
||||
Q1Nma0pRVHh4L3IwQm1GbTdqb1BUcWsKLS0tIFRQOVIxb1FRc29WSVVERWsxSDhq
|
||||
NGprRGVyZ2plWVNrM3drM3JSUjM2L0UKuNk5DqYn2DIfRpY72zDRP5BKoVAXtNv9
|
||||
uLI//8wc7f4I3uBdARQdpRE1fapY1UOJOn3i0yndrZARPEbdohRK1Q==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
lastmodified: "2025-01-24T12:59:25Z"
|
||||
mac: ENC[AES256_GCM,data:WGWGvbqu07XZ5oU2HBGUbP/9oNCavPBXb2SIm10CG2s377QAWZmpdOC2AGAX8J3NfLtyWEHm8WUQSKjNKvKWARsXU24lNnY+BTSIkF8ymrAU/rRMX8VJi92IYjregAfVBIaYomxqJFhNuAhmsQ75ZYMpRBTusxiEFEdl/H9obiY=,iv:VXIVkpnOY2gZ/xDX/oFvZn08K5Gp49tpiJQGK20blro=,tag:Hkk92ZQWTRY9oQb3Mm6R3w==,type:str]
|
||||
pgp: []
|
||||
unencrypted_suffix: _unencrypted
|
||||
version: 3.9.3
|
||||
395
hosts/canopus/default.nix
Executable file
@@ -0,0 +1,395 @@
|
||||
{
|
||||
inputs,
|
||||
username,
|
||||
pkgs,
|
||||
lib,
|
||||
config,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
inputs.nixos-hardware.nixosModules.asus-zephyrus-ga503
|
||||
inputs.disko.nixosModules.default
|
||||
|
||||
(import ./disko.nix {device = "/dev/nvme0n1";})
|
||||
./hardware.nix
|
||||
|
||||
../common
|
||||
../../modules/nixos/desktop
|
||||
../../modules/nixos/desktop/awesome
|
||||
../../modules/nixos/desktop/hyprland
|
||||
../../modules/nixos/virtualisation
|
||||
../../modules/nixos/steam.nix
|
||||
];
|
||||
|
||||
tux.services.openssh.enable = true;
|
||||
|
||||
nixpkgs.config.cudaSupport = true;
|
||||
|
||||
sops.secrets = {
|
||||
hyperbolic_api_key = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
owner = "${username}";
|
||||
};
|
||||
|
||||
gemini_api_key = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
owner = "${username}";
|
||||
};
|
||||
};
|
||||
|
||||
networking = {
|
||||
hostName = "canopus";
|
||||
networkmanager = {
|
||||
enable = true;
|
||||
wifi.powersave = false;
|
||||
};
|
||||
firewall = {
|
||||
enable = true;
|
||||
allowedTCPPorts = [80 443 22 3000 6666 8081];
|
||||
|
||||
# Facilitate firewall punching
|
||||
allowedUDPPorts = [41641];
|
||||
|
||||
allowedTCPPortRanges = [
|
||||
{
|
||||
from = 1714;
|
||||
to = 1764;
|
||||
}
|
||||
];
|
||||
allowedUDPPortRanges = [
|
||||
{
|
||||
from = 1714;
|
||||
to = 1764;
|
||||
}
|
||||
];
|
||||
};
|
||||
};
|
||||
|
||||
boot = {
|
||||
binfmt.emulatedSystems = ["aarch64-linux"];
|
||||
|
||||
plymouth = {
|
||||
enable = true;
|
||||
theme = "spinner-monochrome";
|
||||
themePackages = [
|
||||
(pkgs.plymouth-spinner-monochrome.override {inherit (config.boot.plymouth) logo;})
|
||||
];
|
||||
};
|
||||
|
||||
kernelParams = [
|
||||
"quiet"
|
||||
"loglevel=3"
|
||||
"systemd.show_status=auto"
|
||||
"udev.log_level=3"
|
||||
"rd.udev.log_level=3"
|
||||
"vt.global_cursor_default=0"
|
||||
];
|
||||
consoleLogLevel = 0;
|
||||
initrd.verbose = false;
|
||||
|
||||
kernelPackages = pkgs.linuxPackages_zen;
|
||||
supportedFilesystems = ["ntfs"];
|
||||
|
||||
initrd.systemd = {
|
||||
enable = lib.mkForce true;
|
||||
|
||||
services.wipe-my-fs = {
|
||||
wantedBy = ["initrd.target"];
|
||||
after = ["initrd-root-device.target"];
|
||||
before = ["sysroot.mount"];
|
||||
unitConfig.DefaultDependencies = "no";
|
||||
serviceConfig.Type = "oneshot";
|
||||
script = ''
|
||||
mkdir /btrfs_tmp
|
||||
mount /dev/disk/by-partlabel/disk-primary-root /btrfs_tmp
|
||||
|
||||
if [[ -e /btrfs_tmp/root ]]; then
|
||||
mkdir -p /btrfs_tmp/old_roots
|
||||
timestamp=$(date --date="@$(stat -c %Y /btrfs_tmp/root)" "+%Y-%m-%-d_%H:%M:%S")
|
||||
mv /btrfs_tmp/root "/btrfs_tmp/old_roots/$timestamp"
|
||||
fi
|
||||
|
||||
delete_subvolume_recursively() {
|
||||
IFS=$'\n'
|
||||
for i in $(btrfs subvolume list -o "$1" | cut -f 9- -d ' '); do
|
||||
delete_subvolume_recursively "/btrfs_tmp/$i"
|
||||
done
|
||||
btrfs subvolume delete "$1"
|
||||
}
|
||||
|
||||
for i in $(find /btrfs_tmp/old_roots/ -maxdepth 1 -mtime +30); do
|
||||
delete_subvolume_recursively "$i"
|
||||
done
|
||||
|
||||
btrfs subvolume create /btrfs_tmp/root
|
||||
umount /btrfs_tmp
|
||||
'';
|
||||
};
|
||||
};
|
||||
|
||||
loader = {
|
||||
systemd-boot = {
|
||||
enable = true;
|
||||
configurationLimit = 5;
|
||||
};
|
||||
efi.canTouchEfiVariables = true;
|
||||
timeout = 1;
|
||||
};
|
||||
};
|
||||
|
||||
hardware = {
|
||||
bluetooth.enable = true;
|
||||
bluetooth.powerOnBoot = true;
|
||||
graphics.enable32Bit = true;
|
||||
};
|
||||
|
||||
security = {
|
||||
polkit.enable = true;
|
||||
rtkit.enable = true;
|
||||
};
|
||||
|
||||
systemd = {
|
||||
enableEmergencyMode = false;
|
||||
|
||||
user = {
|
||||
services.polkit-gnome-authentication-agent-1 = {
|
||||
description = "polkit-gnome-authentication-agent-1";
|
||||
wantedBy = ["graphical-session.target"];
|
||||
wants = ["graphical-session.target"];
|
||||
after = ["graphical-session.target"];
|
||||
serviceConfig = {
|
||||
Type = "simple";
|
||||
ExecStart = "${pkgs.polkit_gnome}/libexec/polkit-gnome-authentication-agent-1";
|
||||
Restart = "on-failure";
|
||||
RestartSec = 1;
|
||||
TimeoutStopSec = 10;
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
|
||||
programs = {
|
||||
ssh.startAgent = true;
|
||||
xfconf.enable = true;
|
||||
file-roller.enable = true;
|
||||
thunar = {
|
||||
enable = true;
|
||||
plugins = with pkgs.xfce; [thunar-archive-plugin thunar-volman];
|
||||
};
|
||||
nix-ld = {
|
||||
enable = true;
|
||||
package = pkgs.nix-ld-rs;
|
||||
};
|
||||
nm-applet.enable = true;
|
||||
noisetorch.enable = true;
|
||||
};
|
||||
|
||||
services = {
|
||||
resolved.enable = true;
|
||||
flatpak.enable = true;
|
||||
|
||||
pipewire = {
|
||||
enable = true;
|
||||
alsa.enable = true;
|
||||
alsa.support32Bit = true;
|
||||
pulse.enable = true;
|
||||
wireplumber.enable = true;
|
||||
};
|
||||
|
||||
logind = {
|
||||
extraConfig = "HandlePowerKey=suspend";
|
||||
lidSwitch = "suspend";
|
||||
lidSwitchExternalPower = "suspend";
|
||||
};
|
||||
|
||||
xrdp = {
|
||||
enable = true;
|
||||
openFirewall = true;
|
||||
defaultWindowManager = "awesome";
|
||||
audio.enable = true;
|
||||
};
|
||||
|
||||
syncthing = {
|
||||
enable = true;
|
||||
user = "tux";
|
||||
dataDir = "/home/tux/";
|
||||
openDefaultPorts = true;
|
||||
};
|
||||
|
||||
xserver = {
|
||||
enable = true;
|
||||
xkb = {
|
||||
layout = "in";
|
||||
variant = "eng";
|
||||
};
|
||||
};
|
||||
|
||||
libinput.touchpad.naturalScrolling = true;
|
||||
|
||||
# To use Auto-cpufreq we need to
|
||||
# disable TLP because it's enabled by nixos-hardware
|
||||
tlp.enable = false;
|
||||
auto-cpufreq = {
|
||||
enable = true;
|
||||
settings = {
|
||||
battery = {
|
||||
platform_profile = "balanced";
|
||||
governor = "powersave";
|
||||
energy_performance_preference = "performance";
|
||||
turbo = "never";
|
||||
scaling_min_freq = 400000;
|
||||
scaling_max_freq = 3800000;
|
||||
};
|
||||
charger = {
|
||||
platform_profile = "performance";
|
||||
governor = "performance";
|
||||
energy_performance_preference = "performance";
|
||||
turbo = "auto";
|
||||
scaling_min_freq = 400000;
|
||||
scaling_max_freq = 3800000;
|
||||
};
|
||||
};
|
||||
};
|
||||
|
||||
blueman.enable = true;
|
||||
|
||||
supergfxd = {
|
||||
enable = true;
|
||||
settings = {
|
||||
mode = "Integrated";
|
||||
vfio_enable = false;
|
||||
vfio_save = false;
|
||||
always_reboot = false;
|
||||
no_logind = false;
|
||||
logout_timeout_s = 180;
|
||||
hotplug_type = "None";
|
||||
};
|
||||
};
|
||||
|
||||
asusd = {
|
||||
enable = true;
|
||||
enableUserService = true;
|
||||
asusdConfig.text = ''
|
||||
(
|
||||
charge_control_end_threshold: 100,
|
||||
panel_od: false,
|
||||
mini_led_mode: false,
|
||||
disable_nvidia_powerd_on_battery: true,
|
||||
ac_command: "",
|
||||
bat_command: "",
|
||||
platform_policy_on_battery: Quiet,
|
||||
platform_policy_on_ac: Quiet,
|
||||
ppt_pl1_spl: None,
|
||||
ppt_pl2_sppt: None,
|
||||
ppt_fppt: None,
|
||||
ppt_apu_sppt: None,
|
||||
ppt_platform_sppt: None,
|
||||
nv_dynamic_boost: None,
|
||||
nv_temp_target: None,
|
||||
)
|
||||
'';
|
||||
profileConfig.text = ''
|
||||
(
|
||||
active_profile: Balanced,
|
||||
)
|
||||
'';
|
||||
fanCurvesConfig.text = ''
|
||||
(
|
||||
profiles: (
|
||||
balanced: [
|
||||
(
|
||||
fan: CPU,
|
||||
pwm: (2, 22, 45, 68, 91, 153, 153, 153),
|
||||
temp: (55, 62, 66, 70, 74, 78, 78, 78),
|
||||
enabled: true,
|
||||
),
|
||||
(
|
||||
fan: GPU,
|
||||
pwm: (2, 25, 48, 71, 94, 165, 165, 165)
|
||||
temp: (55, 62, 66, 70, 74, 78, 78, 78),
|
||||
enabled: true,
|
||||
),
|
||||
],
|
||||
performance: [
|
||||
(
|
||||
fan: CPU,
|
||||
pwm: (35, 68, 79, 91, 114, 175, 175, 175),
|
||||
temp: (58, 62, 66, 70, 74, 78, 78, 78),
|
||||
enabled: true,
|
||||
),
|
||||
(
|
||||
fan: GPU,
|
||||
pwm: (35, 71, 84, 94, 119, 188, 188, 188),
|
||||
temp: (58, 62, 66, 70, 74, 78, 78, 78),
|
||||
enabled: true,
|
||||
),
|
||||
],
|
||||
quiet: [
|
||||
(
|
||||
fan: CPU,
|
||||
pwm: (2, 12, 25, 35, 48, 61, 84, 90),
|
||||
temp: (55, 62, 66, 70, 74, 78, 82, 82),
|
||||
enabled: true,
|
||||
),
|
||||
(
|
||||
fan: GPU,
|
||||
pwm: (2, 12, 25, 35, 48, 61, 84, 84),
|
||||
temp: (55, 62, 66, 70, 74, 78, 82, 82),
|
||||
enabled: true,
|
||||
),
|
||||
],
|
||||
custom: [],
|
||||
),
|
||||
)
|
||||
'';
|
||||
};
|
||||
|
||||
gvfs.enable = true;
|
||||
tumbler.enable = true;
|
||||
# @FIX gnome gcr agent conflicts with programs.ssh.startAgent;
|
||||
# gnome.gnome-keyring.enable = true;
|
||||
tailscale = {
|
||||
enable = true;
|
||||
extraUpFlags = ["--login-server https://hs.tux.rs"];
|
||||
};
|
||||
mullvad-vpn = {
|
||||
enable = true;
|
||||
package = pkgs.mullvad-vpn;
|
||||
};
|
||||
};
|
||||
|
||||
fonts.packages = with pkgs.nerd-fonts; [
|
||||
fira-code
|
||||
jetbrains-mono
|
||||
];
|
||||
|
||||
programs.fuse.userAllowOther = true;
|
||||
fileSystems."/persist".neededForBoot = true;
|
||||
environment.persistence."/persist" = {
|
||||
hideMounts = true;
|
||||
directories = [
|
||||
"/var/log"
|
||||
"/var/lib/bluetooth"
|
||||
"/var/lib/tailscale"
|
||||
"/var/lib/nixos"
|
||||
"/var/lib/docker"
|
||||
"/var/lib/waydroid"
|
||||
"/etc/NetworkManager/system-connections"
|
||||
];
|
||||
files = [
|
||||
# "/etc/machine-id"
|
||||
"/etc/ssh/ssh_host_ed25519_key"
|
||||
"/etc/ssh/ssh_host_ed25519_key.pub"
|
||||
"/etc/ssh/ssh_host_rsa_key"
|
||||
"/etc/ssh/ssh_host_rsa_key.pub"
|
||||
];
|
||||
};
|
||||
|
||||
home-manager.users.${username} = {
|
||||
imports = [
|
||||
./home.nix
|
||||
];
|
||||
};
|
||||
|
||||
system.stateVersion = "24.11";
|
||||
}
|
||||
48
hosts/canopus/disko.nix
Normal file
@@ -0,0 +1,48 @@
|
||||
{device ? throw "Set this to the disk device, e.g. /dev/nvme0n1", ...}: {
|
||||
disko.devices.disk.primary = {
|
||||
inherit device;
|
||||
type = "disk";
|
||||
content = {
|
||||
type = "gpt"; # GPT partitioning scheme
|
||||
partitions = {
|
||||
# EFI Partition
|
||||
ESP = {
|
||||
size = "512M";
|
||||
type = "EF00";
|
||||
content = {
|
||||
type = "filesystem";
|
||||
format = "vfat";
|
||||
mountpoint = "/boot";
|
||||
mountOptions = ["defaults" "umask=0077"];
|
||||
};
|
||||
};
|
||||
# Btrfs Root Partition
|
||||
root = {
|
||||
size = "100%"; # Use remaining space
|
||||
type = "8300"; # Linux filesystem type
|
||||
content = {
|
||||
type = "btrfs";
|
||||
subvolumes = {
|
||||
"/root" = {
|
||||
mountOptions = ["compress=zstd"]; # Compression for better performance
|
||||
mountpoint = "/"; # Root subvolume
|
||||
};
|
||||
"/persist" = {
|
||||
mountOptions = ["compress=zstd"]; # Compression for persistent data
|
||||
mountpoint = "/persist"; # Persistent subvolume
|
||||
};
|
||||
"/nix" = {
|
||||
mountOptions = [
|
||||
"compress=zstd"
|
||||
"noatime"
|
||||
"noacl"
|
||||
]; # Optimize for Nix store
|
||||
mountpoint = "/nix"; # Nix subvolume
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
26
hosts/canopus/hardware.nix
Executable file
@@ -0,0 +1,26 @@
|
||||
# Do not modify this file! It was generated by ‘nixos-generate-config’
|
||||
# and may be overwritten by future invocations. Please make changes
|
||||
# to /etc/nixos/configuration.nix instead.
|
||||
{ config, lib, pkgs, modulesPath, ... }:
|
||||
|
||||
{
|
||||
imports =
|
||||
[ (modulesPath + "/installer/scan/not-detected.nix")
|
||||
];
|
||||
|
||||
boot.initrd.availableKernelModules = [ "nvme" "xhci_pci" "usbhid" "usb_storage" "sd_mod" "sdhci_pci" ];
|
||||
boot.initrd.kernelModules = [ ];
|
||||
boot.kernelModules = [ "kvm-amd" ];
|
||||
boot.extraModulePackages = [ ];
|
||||
|
||||
# Enables DHCP on each ethernet and wireless interface. In case of scripted networking
|
||||
# (the default) this is the recommended approach. When using systemd-networkd it's
|
||||
# still possible to use this option, but it's recommended to use it in conjunction
|
||||
# with explicit per-interface declarations with `networking.interfaces.<interface>.useDHCP`.
|
||||
networking.useDHCP = lib.mkDefault true;
|
||||
# networking.interfaces.enp3s0.useDHCP = lib.mkDefault true;
|
||||
# networking.interfaces.wlp4s0.useDHCP = lib.mkDefault true;
|
||||
|
||||
nixpkgs.hostPlatform = lib.mkDefault "x86_64-linux";
|
||||
hardware.cpu.amd.updateMicrocode = lib.mkDefault config.hardware.enableRedistributableFirmware;
|
||||
}
|
||||
110
hosts/canopus/home.nix
Normal file
@@ -0,0 +1,110 @@
|
||||
{
|
||||
pkgs,
|
||||
username,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
../../modules/home/desktop/awesome
|
||||
../../modules/home/desktop/hyprland
|
||||
../../modules/home/picom
|
||||
../../modules/home/alacritty
|
||||
../../modules/home/wezterm
|
||||
../../modules/home/ghostty
|
||||
../../modules/home/desktop/rofi
|
||||
../../modules/home/barrier
|
||||
../../modules/home/firefox
|
||||
../../modules/home/brave
|
||||
../../modules/home/vs-code
|
||||
../../modules/home/mopidy
|
||||
../../modules/home/thunderbird
|
||||
../../modules/home/easyeffects
|
||||
../../modules/home/discord
|
||||
../../modules/home/kdeconnect
|
||||
../../modules/home/obs-studio
|
||||
];
|
||||
|
||||
home.pointerCursor = {
|
||||
package = pkgs.bibata-cursors;
|
||||
name = "Bibata-Modern-Ice";
|
||||
};
|
||||
|
||||
qt.enable = true;
|
||||
qt.platformTheme.name = "gtk";
|
||||
qt.style.name = "adwaita-dark";
|
||||
qt.style.package = pkgs.adwaita-qt;
|
||||
|
||||
gtk = {
|
||||
enable = true;
|
||||
theme = {
|
||||
name = "Materia-dark";
|
||||
package = pkgs.materia-theme;
|
||||
};
|
||||
iconTheme = {
|
||||
package = pkgs.tela-icon-theme;
|
||||
name = "Tela-black";
|
||||
};
|
||||
};
|
||||
|
||||
services.flameshot = {
|
||||
enable = true;
|
||||
package = pkgs.flameshot.override {enableWlrSupport = true;};
|
||||
};
|
||||
|
||||
home.packages = with pkgs; [
|
||||
telegram-desktop
|
||||
anydesk
|
||||
stable.rustdesk-flutter
|
||||
rawtherapee
|
||||
stable.beekeeper-studio
|
||||
libreoffice-qt
|
||||
spotify
|
||||
stremio
|
||||
galaxy-buds-client
|
||||
copyq
|
||||
vlc
|
||||
tor-browser
|
||||
distrobox
|
||||
];
|
||||
|
||||
home.persistence."/persist/home/${username}" = {
|
||||
directories = [
|
||||
"Downloads"
|
||||
"Music"
|
||||
"Wallpapers"
|
||||
"Documents"
|
||||
"Videos"
|
||||
"Projects"
|
||||
"Stuff"
|
||||
"go"
|
||||
".mozilla"
|
||||
".ssh"
|
||||
".wakatime"
|
||||
".rustup"
|
||||
".cargo"
|
||||
".config/BraveSoftware"
|
||||
".config/copyq"
|
||||
".config/discord"
|
||||
".config/Vencord"
|
||||
".config/vesktop"
|
||||
".config/sops"
|
||||
".config/obs-studio"
|
||||
".config/rustdesk"
|
||||
".config/spotify"
|
||||
".local/share/nvim"
|
||||
".local/share/zsh"
|
||||
".local/share/zoxide"
|
||||
".local/share/Smart\ Code\ ltd"
|
||||
".local/share/GalaxyBudsClient"
|
||||
".local/share/TelegramDesktop"
|
||||
".local/state/lazygit"
|
||||
".cache/spotify"
|
||||
];
|
||||
files = [
|
||||
".wakatime.cfg"
|
||||
".config/aichat/.env"
|
||||
];
|
||||
allowOther = true;
|
||||
};
|
||||
|
||||
home.stateVersion = "24.11";
|
||||
}
|
||||
26
hosts/canopus/secrets.yaml
Normal file
@@ -0,0 +1,26 @@
|
||||
hyperbolic_api_key: ENC[AES256_GCM,data:FjDSbdutLa9hnVGRR+k2MznVfDGAx1/rNfjY/vaBuvKoBRj7aHqGpQ1cvhfxjyLMqPLqLnmimEtZeykvgkIIjKGzw5PewE23+lrN3oQyoYJvK+b8PRStjSaxOfzOnuLXi+YVnsU939nStLwnmSYKDabNWgFcWYsHwtHDafuWyovM9sVwasTn,iv:bxseG6GLKBL/CJOS8SrhgiLEyvMGSNQIMJSYLk2MqEo=,tag:4wxmkUwlcu23d7pMHbvIoQ==,type:str]
|
||||
gemini_api_key: ENC[AES256_GCM,data:HiseQDB9nJBynCvdqLx0NcJZHB71uEvBlA3l/Lw2EMHFUXSHqPoS,iv:4C5EGUdfwxhT6ExDYNcbc+MFE+rGvLRsZjbo9L/o/Eo=,tag:hvaODOzhFoywgsXZSQKeKA==,type:str]
|
||||
sops:
|
||||
age:
|
||||
- recipient: age14vktfes95f33vuefwnmuvryas7az04u76dsgyhfvsx73czkvmp2q7njkl4
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSBwUnhkNzR0TnNzL29xV3cv
|
||||
R3lqYUtVWWlNOVFTZHhTMWJZL1ZJUDIxaG0wCnIvQnkxSWJxWTZYVEkvS1ZWSEhk
|
||||
YmhuK2JtS3lmUjV6MW50SGZrTnpkeDAKLS0tIDkvbk5abnhkNlA0dmgwV0Z0L1BS
|
||||
UUduZUV3OGcvaFdBOFFsc0xzVCtQcUUKrmZvR2onMD0snqPw8okxaK6Tz5sA/cmR
|
||||
1ZczgwLslJA7kwGKYOslUGA7aGB4jyP+M74wBAVa71BqWatypp0RfA==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1udt3cssu7ahdrhsvckt8450rswrr6mknn36xpq74dkfp9lpajvnq84kdzj
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSBEOE0xbDN0UmdVdE1DR1lo
|
||||
dmNudDk2TjNQdHFGc0lJTSt0dVVRU3BPRlg0ClV1ZUdxRVNpSmhYQm80QjdhdFc5
|
||||
SVI4bi93WDBDWHQvejJIV21Bc2NsMjgKLS0tIEduZ2hHSnI3UXlGU2ZFZkpTRDJo
|
||||
K0tiZ0swMmpuVW02OHMrRThlOXBWUjQKYHyJZuvQABh+gJ+THQ5SakVEqsKkyBMb
|
||||
k6KnjRATpdZlmm0GjbD4aasF/j/V2fuH327Z72jPWQuI1y5ZfbDhSg==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
lastmodified: "2025-08-08T13:20:36Z"
|
||||
mac: ENC[AES256_GCM,data:WvY1VWONZarkRNjArqa2ASPLLRsUgOxA+QX2YPcUPvoAdpwuFS9Fs2kIaU61lOKQLKDwcR3XvtB2BhnwhUltF0OPSNY3651fc/HFQx3eIJaSAL8Qqa8OywCe897fcrNyvHROhi/h4HX6RI+NakTR1UVS8fR769IIkafE/Zbbn+8=,iv:wAg/ea6ScBK7kPYKjgfMMtACCxIh5agNIqv42iCwycg=,tag:tsWH1E+ulsLquT1TqtmN0A==,type:str]
|
||||
unencrypted_suffix: _unencrypted
|
||||
version: 3.10.2
|
||||
63
hosts/capella/default.nix
Normal file
@@ -0,0 +1,63 @@
|
||||
{
|
||||
pkgs,
|
||||
username,
|
||||
outputs,
|
||||
inputs,
|
||||
email,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
../../modules/droid/sshd.nix
|
||||
];
|
||||
|
||||
android-integration.am.enable = true;
|
||||
android-integration.termux-open-url.enable = true;
|
||||
android-integration.xdg-open.enable = true;
|
||||
android-integration.termux-setup-storage.enable = true;
|
||||
android-integration.termux-reload-settings.enable = true;
|
||||
|
||||
terminal.font = let
|
||||
firacode = pkgs.nerd-fonts.fira-code;
|
||||
fontPath = "share/fonts/truetype/NerdFonts/FiraCode/FiraCodeNerdFont-Regular.ttf";
|
||||
in "${firacode}/${fontPath}";
|
||||
|
||||
time.timeZone = "Asia/Kolkata";
|
||||
|
||||
tux.services.openssh = {
|
||||
enable = true;
|
||||
ports = [8033];
|
||||
authorizedKeys = [
|
||||
"ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIL+OzPUe2ECPC929DqpkM39tl/vdNAXfsRnmrGfR+X3D ${email}"
|
||||
];
|
||||
};
|
||||
|
||||
user = {
|
||||
uid = 10479;
|
||||
gid = 10479;
|
||||
shell = "${pkgs.zsh}/bin/zsh";
|
||||
};
|
||||
|
||||
environment.etcBackupExtension = ".backup";
|
||||
environment.motd = '''';
|
||||
environment.packages = with pkgs; [
|
||||
nano
|
||||
git
|
||||
neovim
|
||||
openssh
|
||||
inputs.trok.packages."aarch64-linux".default
|
||||
];
|
||||
|
||||
home-manager = {
|
||||
config = ./home.nix;
|
||||
backupFileExtension = "backup";
|
||||
extraSpecialArgs = {inherit inputs outputs username email;};
|
||||
useGlobalPkgs = true;
|
||||
};
|
||||
|
||||
# Set up nix for flakes
|
||||
nix.extraOptions = ''
|
||||
experimental-features = nix-command flakes
|
||||
'';
|
||||
|
||||
system.stateVersion = "24.05";
|
||||
}
|
||||
35
hosts/capella/home.nix
Normal file
@@ -0,0 +1,35 @@
|
||||
{pkgs, ...}: {
|
||||
imports = [
|
||||
../../modules/home/git
|
||||
../../modules/home/starship
|
||||
../../modules/home/fastfetch
|
||||
];
|
||||
|
||||
programs = {
|
||||
bat.enable = true;
|
||||
zoxide = {
|
||||
enable = true;
|
||||
options = ["--cmd cd"];
|
||||
};
|
||||
zsh = {
|
||||
enable = true;
|
||||
shellAliases = {
|
||||
ls = "lsd";
|
||||
};
|
||||
syntaxHighlighting.enable = true;
|
||||
autosuggestion.enable = true;
|
||||
initContent = ''
|
||||
fastfetch
|
||||
'';
|
||||
};
|
||||
};
|
||||
|
||||
home.packages = with pkgs; [
|
||||
neovim
|
||||
busybox
|
||||
lsd
|
||||
fastfetch
|
||||
];
|
||||
|
||||
home.stateVersion = "24.05";
|
||||
}
|
||||
58
hosts/common/default.nix
Normal file
@@ -0,0 +1,58 @@
|
||||
{
|
||||
username,
|
||||
outputs,
|
||||
inputs,
|
||||
email,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
inputs.impermanence.nixosModules.impermanence
|
||||
inputs.home-manager.nixosModules.home-manager
|
||||
inputs.nix-index-database.nixosModules.nix-index
|
||||
|
||||
../../modules/base
|
||||
../../modules/nixos/fail2ban.nix
|
||||
../../modules/nixos/selfhosted/upstream-proxy.nix
|
||||
../../modules/nixos/selfhosted/tfolio.nix
|
||||
../../modules/nixos/selfhosted/cyber-tux.nix
|
||||
../../modules/nixos/networking/ssh.nix
|
||||
];
|
||||
|
||||
sops.secrets.tux-password = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
neededForUsers = true;
|
||||
};
|
||||
|
||||
time.timeZone = "Asia/Kolkata";
|
||||
i18n = {
|
||||
defaultLocale = "en_US.UTF-8";
|
||||
extraLocaleSettings = {
|
||||
LC_ADDRESS = "en_IN";
|
||||
LC_IDENTIFICATION = "en_IN";
|
||||
LC_MEASUREMENT = "en_IN";
|
||||
LC_MONETARY = "en_IN";
|
||||
LC_NAME = "en_IN";
|
||||
LC_NUMERIC = "en_IN";
|
||||
LC_PAPER = "en_IN";
|
||||
LC_TELEPHONE = "en_IN";
|
||||
LC_TIME = "en_IN";
|
||||
};
|
||||
};
|
||||
|
||||
security.sudo.wheelNeedsPassword = false;
|
||||
|
||||
programs = {
|
||||
zsh.enable = true;
|
||||
};
|
||||
|
||||
home-manager = {
|
||||
backupFileExtension = "hm-backup";
|
||||
useUserPackages = true;
|
||||
extraSpecialArgs = {inherit inputs outputs username email;};
|
||||
users.${username} = {
|
||||
imports = [
|
||||
./home.nix
|
||||
];
|
||||
};
|
||||
};
|
||||
}
|
||||
45
hosts/common/home.nix
Normal file
@@ -0,0 +1,45 @@
|
||||
{
|
||||
outputs,
|
||||
username,
|
||||
inputs,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
inputs.impermanence.nixosModules.home-manager.impermanence
|
||||
inputs.nix-index-database.homeModules.nix-index
|
||||
|
||||
../../modules/home/shell
|
||||
../../modules/home/git
|
||||
../../modules/home/starship
|
||||
../../modules/home/fastfetch
|
||||
../../modules/home/nvim
|
||||
../../modules/home/tmux
|
||||
../../modules/home/helix
|
||||
../../modules/home/aria2
|
||||
];
|
||||
|
||||
nixpkgs = {
|
||||
overlays = [
|
||||
outputs.overlays.additions
|
||||
outputs.overlays.modifications
|
||||
outputs.overlays.stable-packages
|
||||
outputs.overlays.nur
|
||||
outputs.overlays.nix-vscode-extensions
|
||||
];
|
||||
|
||||
config = {
|
||||
allowUnfree = true;
|
||||
allowUnfreePredicate = _: true;
|
||||
joypixels.acceptLicense = true;
|
||||
};
|
||||
};
|
||||
|
||||
home = {
|
||||
username = "${username}";
|
||||
homeDirectory = "/home/${username}";
|
||||
};
|
||||
|
||||
programs.home-manager.enable = true;
|
||||
|
||||
systemd.user.startServices = "sd-switch";
|
||||
}
|
||||
79
hosts/common/secrets.yaml
Normal file
@@ -0,0 +1,79 @@
|
||||
tux-password: ENC[AES256_GCM,data:ysw9mJef/l7WdXP9cCSM88GX019UMr8od80rSwZBftN8tWDGPe0/mdRmePXxaEY9yEXhvRON/4IaFIPVQ3VnbExcGrnbV5+u9A==,iv:P+BnLLJs7ePJvsBHgsaISvjy33KtLFQENS+YB2eroGI=,tag:D4dTQXzmBkeCkdFu2Ozlcg==,type:str]
|
||||
sops:
|
||||
age:
|
||||
- recipient: age14vktfes95f33vuefwnmuvryas7az04u76dsgyhfvsx73czkvmp2q7njkl4
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSByVkUyUU8wbXNqY0JVb2RD
|
||||
N3NiNXJ3Tzc0bjU2QnJrbDcxTDVQeUJUYVhFCnNud3lXWmh5azByaEk0dkIyT1dP
|
||||
V0NKMzlpdTZaM2JpTyt4L1V1M2l1MGsKLS0tIDlzbjVHNUw4ci9mZ0tBaVhSNjJS
|
||||
MFdDa3hHMTlmU05TN2UxY3dhdGVFdU0KQ+hjPwBpv8g3x/N+Yd4kwUtiIxXDcZRx
|
||||
EFjLnDiOA5gkZqXCo05E1lXJN17wU59pYs1+1pfBYbGKc2oV+3oquw==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1f860dfewlx5jtt9ejr47gywx70p3dmyc8mat29gpr75psljwjv8q5xyxkq
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSBqM1Z4MlNwY1VxdXF6RG1P
|
||||
cWQ0S0hMOWh0aUUrdVF5VDVWZVNDYi82NERjCmZFSEdyNXNLMXBHeUp4NUNpZnp4
|
||||
UEVWZEJhZC9YSzgzb1VVMDNsdUk2K00KLS0tIGpqaS92NmJzVXRRb09SSGhJYTlE
|
||||
ZmpXd09Eam5EN1ExZFdYVXUxUEp5S0UKWZG87YOWIZR/eIFRjyZt4Jf8St+NEk/L
|
||||
obwyOlDnRJ9wI30g9VXMoYTUdZcebY6t6tmRvIKL4pbadua2JXwamg==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1udt3cssu7ahdrhsvckt8450rswrr6mknn36xpq74dkfp9lpajvnq84kdzj
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSBQelFwUGIzc1RuVFpGYzd6
|
||||
cjZOM3FGUDlPVTVuRkxqalEwamhlVjNFdVVBCjBiWFN0RVArYWNoL2ZuYXhSN0Y0
|
||||
eTFEWFdYUFJVWU53cmNURS9jNEJTSDgKLS0tIHd3SFlISGdVSTBJSmd3UUp0VVBE
|
||||
MCt6ZnMzRDNEK3I3ZXFucjRXRDJ3Wm8KltIXRrGVkr3AOvQ44/nlsqmGW6s/hlHF
|
||||
84elOBidwgb95RIhetUppD6jUJz2p0GHIsIvEc9AuZRbPkntmVjHkA==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1jg642q775gmnmxeu29gcf3lph8vem4xr8t84cxe809dpd0myrussh49h60
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSAxQXR2QVJCSk92WGF1dGxK
|
||||
K0o3V3dPTS9ZZHBDUEcrVWxKMzZpem5uL0VFCnB2c2hIcmxQTWdmTHhnVFhLQXhT
|
||||
b3V4Y01JSUdYMThqNy8zVEI4QXc3SmcKLS0tIDBuekhnaWRGUVF4a0tseUQxZW55
|
||||
L1VsWHljZ3VaMjNkbHhhYlVTU0dTL1UKXe4osbjCyMzBuJoD8bnhnAJSmaeOmtpr
|
||||
Gee9MSubfgxXKN+GNOjMF0DBB3SDlJTXjF7LpqqkiSbg0Jy4W6b+mA==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1zsl5d4vj6gl3h96y5p53sq5y4vr4vtlwp727h7rp9a4xfkxm53lqrh6r50
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSBmT3hudFJ5QTVLbHh1Zjg3
|
||||
elA1VEw4TzdhNTJqSVk3MWdwUnhUZ0V3ZmgwCkdOKzJ4RlVuR1VJL0NhbTc0SnZY
|
||||
MlFrbnhuN1UwYmE2ZlhpWnZVTWc4RncKLS0tIFdLT2k3dWdwQXJlSHQxWWJUd3Yx
|
||||
UHJ1aDhWVXprMUcyVHQxTlJEV21MMjQKveI0EjbGWwsBlIzHUIvjrTM5G7ZtulM/
|
||||
AuhqsH3qkDU4L3FdkVR5oG8yaCDbBxLDFhCDnXAGKrGCwOr1KB5hmQ==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1zujp5gxy7suv8ysnygv43cmzuvv36nxfg0ch7r3xg2emc6fz3vmqqujheq
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSBkZlhyVVh6K2tvd2ZGODhY
|
||||
ODRLbFFiYmlPM3F5L3VwNS9EVGtuSWQ1VHlvCk1GTWlRUk9WVURWOEdBVlVHb1Rw
|
||||
c09EYlhFWFZHQmV3MUU5eU1ZYVE2MlEKLS0tIEFMV1FDTnBNMTEvTWREY3VFZjJ6
|
||||
QVV5U3dvTDFBT2s4bTQ1SXQ4U2RaYnMKs8q7OeaK188bTvVmAia0oF5SnpMOPKTd
|
||||
V31tngEgvmI7MxH9BrgjWneJye91Q/hCED0/aK0AuXIRapWgi1hGlA==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1ydkclhk9kwqdq74utesqdfupt43lz64d5k65gz2z9uyljcqq9fcq3hv28l
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSBESVVPNGpGYnB0aFAzYnF3
|
||||
aUhkZkI1a2dWd2txSm9aWnpOKzBPdzg0VGdzCkJkeDJlZDdSZUVGTHVwQ2M2UjBj
|
||||
MjRnM2lNMWNVNFF1bTA0NGI3SGNPdFUKLS0tIGV6UkRQUWFYWjBrMzhhTmd4QlBV
|
||||
RTkvRVBSeUFUVXpyVHhHTFpZNzR3NlkKOksXAReInUnFJPuFsfu08MRQoA5J0j/H
|
||||
3cUt2jBIheWXBtg1Plz9UcXdjPaUEROadFcRveiGBaBEVz0LyBs8WA==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1y4luzn2jls7rvgphej23srvdlx563lxq29tvf66vhwwzaf7c3f3qzvresh
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSA0UVY1a1JFRTBZalRDeFll
|
||||
aHVNTnQ0MEtpN0pObnhaMlYwaXp2b2tKM2gwCmIrL2dzb0xGR0NCZzFIL0o2SS8w
|
||||
YnE2OE9rZFFWakgrYkNVcFpjUXJpbXMKLS0tIE9rZEoxNjdJbG9adVAydk1DVnhK
|
||||
WGhPaC96dk9qUzNxT1hadTZZSGZKQ28KiNhLhLaUSTVltWzyYHWLk6M8M3lxgvHj
|
||||
rPgFNVEcpVKN9f2v4N+XJipDaVgnP1YwwIlT0XSRQNrGWcO2JL6nmg==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
lastmodified: "2025-07-09T22:50:12Z"
|
||||
mac: ENC[AES256_GCM,data:xf2fW1ajcrAx/oPwYvZmNKNJ6yHF/v3aVt3bIyENyfmB90yPDhHiw9twj7MYy1hVJyKE1Iy+1bmEgERBwaum2sROvzpCzuKbB8avJfBfeqpwBPob2yRdoAKFN29xgiJVJjtw2zKFf8NzMnv9Y5sLxgnhq5VB7aCavZ9+o0603kI=,iv:8aS9jVOm4rZpU/JTi9uUKoEfvo44Zhy43e6/GsIM7CE=,tag:D9I31EQwI6bCAN3tU4jGJg==,type:str]
|
||||
unencrypted_suffix: _unencrypted
|
||||
version: 3.10.2
|
||||
150
hosts/homelab/default.nix
Executable file
@@ -0,0 +1,150 @@
|
||||
{
|
||||
inputs,
|
||||
username,
|
||||
pkgs,
|
||||
lib,
|
||||
config,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
inputs.disko.nixosModules.default
|
||||
|
||||
(import ./disko.nix {device = "/dev/nvme0n1";})
|
||||
./hardware.nix
|
||||
|
||||
../common
|
||||
../../modules/nixos/desktop
|
||||
../../modules/nixos/virtualisation/docker.nix
|
||||
];
|
||||
|
||||
tux.services.openssh.enable = true;
|
||||
|
||||
sops.secrets = {
|
||||
discord_token = {
|
||||
sopsFile = ./secrets.yaml;
|
||||
};
|
||||
};
|
||||
|
||||
tux.services.cyber-tux = {
|
||||
enable = true;
|
||||
environmentFile = config.sops.secrets.discord_token.path;
|
||||
};
|
||||
|
||||
networking = {
|
||||
hostName = "homelab";
|
||||
networkmanager = {
|
||||
enable = true;
|
||||
wifi.powersave = false;
|
||||
};
|
||||
firewall = {
|
||||
enable = true;
|
||||
allowedTCPPorts = [22];
|
||||
|
||||
# Facilitate firewall punching
|
||||
allowedUDPPorts = [41641];
|
||||
};
|
||||
};
|
||||
|
||||
boot = {
|
||||
consoleLogLevel = 0;
|
||||
initrd.verbose = false;
|
||||
|
||||
kernelPackages = pkgs.linuxPackages_zen;
|
||||
|
||||
initrd.systemd = {
|
||||
enable = lib.mkForce true;
|
||||
|
||||
services.wipe-my-fs = {
|
||||
wantedBy = ["initrd.target"];
|
||||
after = ["initrd-root-device.target"];
|
||||
before = ["sysroot.mount"];
|
||||
unitConfig.DefaultDependencies = "no";
|
||||
serviceConfig.Type = "oneshot";
|
||||
script = ''
|
||||
mkdir /btrfs_tmp
|
||||
mount /dev/disk/by-partlabel/disk-primary-root /btrfs_tmp
|
||||
|
||||
if [[ -e /btrfs_tmp/root ]]; then
|
||||
mkdir -p /btrfs_tmp/old_roots
|
||||
timestamp=$(date --date="@$(stat -c %Y /btrfs_tmp/root)" "+%Y-%m-%-d_%H:%M:%S")
|
||||
mv /btrfs_tmp/root "/btrfs_tmp/old_roots/$timestamp"
|
||||
fi
|
||||
|
||||
delete_subvolume_recursively() {
|
||||
IFS=$'\n'
|
||||
for i in $(btrfs subvolume list -o "$1" | cut -f 9- -d ' '); do
|
||||
delete_subvolume_recursively "/btrfs_tmp/$i"
|
||||
done
|
||||
btrfs subvolume delete "$1"
|
||||
}
|
||||
|
||||
for i in $(find /btrfs_tmp/old_roots/ -maxdepth 1 -mtime +30); do
|
||||
delete_subvolume_recursively "$i"
|
||||
done
|
||||
|
||||
btrfs subvolume create /btrfs_tmp/root
|
||||
umount /btrfs_tmp
|
||||
'';
|
||||
};
|
||||
};
|
||||
|
||||
loader = {
|
||||
systemd-boot = {
|
||||
enable = true;
|
||||
configurationLimit = 5;
|
||||
};
|
||||
efi.canTouchEfiVariables = true;
|
||||
timeout = 1;
|
||||
};
|
||||
};
|
||||
|
||||
hardware = {
|
||||
graphics.enable32Bit = true;
|
||||
};
|
||||
|
||||
security = {
|
||||
rtkit.enable = true;
|
||||
};
|
||||
|
||||
programs = {
|
||||
nix-ld = {
|
||||
enable = true;
|
||||
package = pkgs.nix-ld-rs;
|
||||
};
|
||||
};
|
||||
|
||||
services = {
|
||||
tailscale = {
|
||||
enable = true;
|
||||
extraUpFlags = ["--login-server https://hs.tux.rs"];
|
||||
};
|
||||
};
|
||||
|
||||
programs.fuse.userAllowOther = true;
|
||||
fileSystems."/persist".neededForBoot = true;
|
||||
environment.persistence."/persist" = {
|
||||
hideMounts = true;
|
||||
directories = [
|
||||
"/var/log"
|
||||
"/var/lib/tailscale"
|
||||
"/var/lib/nixos"
|
||||
"/etc/NetworkManager/system-connections"
|
||||
];
|
||||
files = [
|
||||
"/etc/ssh/ssh_host_ed25519_key"
|
||||
"/etc/ssh/ssh_host_ed25519_key.pub"
|
||||
"/etc/ssh/ssh_host_rsa_key"
|
||||
"/etc/ssh/ssh_host_rsa_key.pub"
|
||||
];
|
||||
};
|
||||
|
||||
home-manager.users.${username} = {
|
||||
imports = [
|
||||
./home.nix
|
||||
];
|
||||
};
|
||||
|
||||
environment.systemPackages = with pkgs; [go-wol];
|
||||
|
||||
system.stateVersion = "24.11";
|
||||
}
|
||||
48
hosts/homelab/disko.nix
Normal file
@@ -0,0 +1,48 @@
|
||||
{device ? throw "Set this to the disk device, e.g. /dev/nvme0n1", ...}: {
|
||||
disko.devices.disk.primary = {
|
||||
inherit device;
|
||||
type = "disk";
|
||||
content = {
|
||||
type = "gpt"; # GPT partitioning scheme
|
||||
partitions = {
|
||||
# EFI Partition
|
||||
ESP = {
|
||||
size = "512M";
|
||||
type = "EF00";
|
||||
content = {
|
||||
type = "filesystem";
|
||||
format = "vfat";
|
||||
mountpoint = "/boot";
|
||||
mountOptions = ["defaults" "umask=0077"];
|
||||
};
|
||||
};
|
||||
# Btrfs Root Partition
|
||||
root = {
|
||||
size = "100%"; # Use remaining space
|
||||
type = "8300"; # Linux filesystem type
|
||||
content = {
|
||||
type = "btrfs";
|
||||
subvolumes = {
|
||||
"/root" = {
|
||||
mountOptions = ["compress=zstd"]; # Compression for better performance
|
||||
mountpoint = "/"; # Root subvolume
|
||||
};
|
||||
"/persist" = {
|
||||
mountOptions = ["compress=zstd"]; # Compression for persistent data
|
||||
mountpoint = "/persist"; # Persistent subvolume
|
||||
};
|
||||
"/nix" = {
|
||||
mountOptions = [
|
||||
"compress=zstd"
|
||||
"noatime"
|
||||
"noacl"
|
||||
]; # Optimize for Nix store
|
||||
mountpoint = "/nix"; # Nix subvolume
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
26
hosts/homelab/hardware.nix
Executable file
@@ -0,0 +1,26 @@
|
||||
# Do not modify this file! It was generated by ‘nixos-generate-config’
|
||||
# and may be overwritten by future invocations. Please make changes
|
||||
# to /etc/nixos/configuration.nix instead.
|
||||
{ config, lib, pkgs, modulesPath, ... }:
|
||||
|
||||
{
|
||||
imports =
|
||||
[ (modulesPath + "/installer/scan/not-detected.nix")
|
||||
];
|
||||
|
||||
boot.initrd.availableKernelModules = [ "nvme" "xhci_pci" "usbhid" "usb_storage" "sd_mod" "sdhci_pci" ];
|
||||
boot.initrd.kernelModules = [ ];
|
||||
boot.kernelModules = [ "kvm-amd" ];
|
||||
boot.extraModulePackages = [ ];
|
||||
|
||||
# Enables DHCP on each ethernet and wireless interface. In case of scripted networking
|
||||
# (the default) this is the recommended approach. When using systemd-networkd it's
|
||||
# still possible to use this option, but it's recommended to use it in conjunction
|
||||
# with explicit per-interface declarations with `networking.interfaces.<interface>.useDHCP`.
|
||||
networking.useDHCP = lib.mkDefault true;
|
||||
# networking.interfaces.enp3s0.useDHCP = lib.mkDefault true;
|
||||
# networking.interfaces.wlp4s0.useDHCP = lib.mkDefault true;
|
||||
|
||||
nixpkgs.hostPlatform = lib.mkDefault "x86_64-linux";
|
||||
hardware.cpu.amd.updateMicrocode = lib.mkDefault config.hardware.enableRedistributableFirmware;
|
||||
}
|
||||
22
hosts/homelab/home.nix
Normal file
@@ -0,0 +1,22 @@
|
||||
{username, ...}: {
|
||||
home.persistence."/persist/home/${username}" = {
|
||||
directories = [
|
||||
"Projects"
|
||||
"Stuff"
|
||||
".ssh"
|
||||
".wakatime"
|
||||
".config/sops"
|
||||
".config/go-wol"
|
||||
".local/share/nvim"
|
||||
".local/share/zsh"
|
||||
".local/share/zoxide"
|
||||
".local/state/lazygit"
|
||||
];
|
||||
files = [
|
||||
".wakatime.cfg"
|
||||
];
|
||||
allowOther = true;
|
||||
};
|
||||
|
||||
home.stateVersion = "24.11";
|
||||
}
|
||||
30
hosts/homelab/secrets.yaml
Normal file
@@ -0,0 +1,30 @@
|
||||
discord_token: ENC[AES256_GCM,data:fZqz6LD3+Svtton5gNCXO5ddWAqW1IyxP3M2DAIXZEIYRHUfAq8h9LES2IHWepjl5qKimxB35zacE/TYK2fitngWtRGVoMDBzzU6VTKNulNV3yFWrPA=,iv:YOplYld+c9vHVC0Srfm89qrh4yUygDiW67X2TdwHKMc=,tag:Ioc2wNLX818fRQ/2PSO7Sw==,type:str]
|
||||
sops:
|
||||
kms: []
|
||||
gcp_kms: []
|
||||
azure_kv: []
|
||||
hc_vault: []
|
||||
age:
|
||||
- recipient: age14vktfes95f33vuefwnmuvryas7az04u76dsgyhfvsx73czkvmp2q7njkl4
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSB2YktFRE9KS0h0T0hDTlpF
|
||||
ZEk0VzNTcVE0ampsWVRtSzJ3UHBXL2NlUUh3Cjk5ZnFKVENmTTJHQjgrVWlyOUE1
|
||||
THUrTUFzdWhKejNUNXpsNVpvZVdJWm8KLS0tIDZ5bmYzSVBUVlVORHAzSGtCQmVo
|
||||
a2JuSWVtMi9FMkova3BCd2F0U2VCRzQKonG/AkEn2X2l3vyr0UlJprGW2ZSwrczq
|
||||
xHafyGiU/I1AO/HoB3BXyP8t/Sgn/dy42lspqZ3MoLLlmx7dQeTd+g==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
- recipient: age1jg642q775gmnmxeu29gcf3lph8vem4xr8t84cxe809dpd0myrussh49h60
|
||||
enc: |
|
||||
-----BEGIN AGE ENCRYPTED FILE-----
|
||||
YWdlLWVuY3J5cHRpb24ub3JnL3YxCi0+IFgyNTUxOSBxWUowUlB2cWVOclpRMENn
|
||||
TU5za0Y2UHZ5eFNZMEdQWm9xdTZFYkVwS2hNCnRBUU1ndFdiQ09sQjBDb1greC93
|
||||
ejl2OVZTTEtIcWpxUk5RRngrbjRWREEKLS0tIDVrSHhxbmJFdWwyQS9xeWlFZitJ
|
||||
Y1RHaFdXaE9DODJtSTFCSVZWb0xVeUEK4qeBKg3u+vhBIM1dQ7BaOWi/C7Q8hk60
|
||||
vu9Zr075n0+kb5Ab+RH24ZmEoP5PJXjwEfbAnmRTjn0reYn1nfcNYA==
|
||||
-----END AGE ENCRYPTED FILE-----
|
||||
lastmodified: "2025-02-15T12:45:59Z"
|
||||
mac: ENC[AES256_GCM,data:NLGe7L/oiG62x4PmQ6FobnuisFmMxYoGhxfqQ4qZdy9emYL/+FnrtFsKTKqZ9IHjrNnCmbk7y+Cds/azC1xGVcaj50jEox87vtqIZ3z0XsD1mJjCAdHkBVzzpQGwHas/5y0Inyj+oKsvQrqVacqYHVA/ES+zMvou8nD+EWIH2LE=,iv:fBVOnwih+QFkYZ8IfMBpQiT1XwSZtzo3VYaBOL3I5o4=,tag:p+ePQsrmcLcnLr2fgWQXQg==,type:str]
|
||||
pgp: []
|
||||
unencrypted_suffix: _unencrypted
|
||||
version: 3.9.4
|
||||
92
hosts/isoImage/default.nix
Normal file
@@ -0,0 +1,92 @@
|
||||
{
|
||||
pkgs,
|
||||
modulesPath,
|
||||
inputs,
|
||||
username,
|
||||
lib,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
"${modulesPath}/installer/cd-dvd/installation-cd-minimal.nix"
|
||||
inputs.home-manager.nixosModules.home-manager
|
||||
|
||||
../common
|
||||
../../modules/nixos/desktop
|
||||
../../modules/nixos/desktop/awesome
|
||||
../../modules/nixos/desktop/hyprland
|
||||
];
|
||||
|
||||
nixpkgs.hostPlatform = "x86_64-linux";
|
||||
|
||||
networking = {
|
||||
hostName = "iso";
|
||||
};
|
||||
|
||||
hardware = {
|
||||
bluetooth.enable = true;
|
||||
bluetooth.powerOnBoot = true;
|
||||
};
|
||||
|
||||
security = {
|
||||
rtkit.enable = true;
|
||||
};
|
||||
|
||||
programs = {
|
||||
ssh.startAgent = true;
|
||||
thunar = {
|
||||
enable = true;
|
||||
plugins = with pkgs.xfce; [thunar-archive-plugin thunar-volman];
|
||||
};
|
||||
nm-applet.enable = true;
|
||||
};
|
||||
|
||||
services = {
|
||||
resolved.enable = true;
|
||||
|
||||
pipewire = {
|
||||
enable = true;
|
||||
alsa.enable = true;
|
||||
alsa.support32Bit = true;
|
||||
pulse.enable = true;
|
||||
};
|
||||
|
||||
logind = {
|
||||
extraConfig = "HandlePowerKey=suspend";
|
||||
lidSwitch = "suspend";
|
||||
lidSwitchExternalPower = "suspend";
|
||||
};
|
||||
|
||||
xserver = {
|
||||
enable = true;
|
||||
xkb = {
|
||||
layout = "in";
|
||||
variant = "eng";
|
||||
};
|
||||
};
|
||||
|
||||
libinput.touchpad.naturalScrolling = true;
|
||||
|
||||
blueman.enable = true;
|
||||
|
||||
gvfs.enable = true;
|
||||
tumbler.enable = true;
|
||||
};
|
||||
|
||||
fonts.packages = with pkgs.nerd-fonts; [
|
||||
fira-code
|
||||
jetbrains-mono
|
||||
];
|
||||
|
||||
home-manager.users.${username} = {
|
||||
imports = [
|
||||
./home.nix
|
||||
];
|
||||
};
|
||||
|
||||
users.users.${username} = {
|
||||
hashedPasswordFile = lib.mkForce null;
|
||||
initialPassword = username;
|
||||
};
|
||||
|
||||
system.stateVersion = "23.11";
|
||||
}
|
||||
24
hosts/isoImage/home.nix
Normal file
@@ -0,0 +1,24 @@
|
||||
{pkgs, ...}: {
|
||||
imports = [
|
||||
../../modules/home/desktop/awesome
|
||||
../../modules/home/desktop/hyprland
|
||||
../../modules/home/picom
|
||||
../../modules/home/alacritty
|
||||
../../modules/home/wezterm
|
||||
../../modules/home/ghostty
|
||||
../../modules/home/desktop/rofi
|
||||
../../modules/home/barrier
|
||||
../../modules/home/firefox
|
||||
../../modules/home/brave
|
||||
../../modules/home/vs-code
|
||||
../../modules/home/mopidy
|
||||
../../modules/home/thunderbird
|
||||
];
|
||||
|
||||
home.pointerCursor = {
|
||||
package = pkgs.bibata-cursors;
|
||||
name = "Bibata-Modern-Ice";
|
||||
};
|
||||
|
||||
home.stateVersion = "24.11";
|
||||
}
|
||||
63
hosts/rigel/default.nix
Normal file
@@ -0,0 +1,63 @@
|
||||
{
|
||||
pkgs,
|
||||
username,
|
||||
outputs,
|
||||
inputs,
|
||||
email,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
../../modules/droid/sshd.nix
|
||||
];
|
||||
|
||||
android-integration.am.enable = true;
|
||||
android-integration.termux-open-url.enable = true;
|
||||
android-integration.xdg-open.enable = true;
|
||||
android-integration.termux-setup-storage.enable = true;
|
||||
android-integration.termux-reload-settings.enable = true;
|
||||
|
||||
terminal.font = let
|
||||
firacode = pkgs.nerd-fonts.fira-code;
|
||||
fontPath = "share/fonts/truetype/NerdFonts/FiraCode/FiraCodeNerdFont-Regular.ttf";
|
||||
in "${firacode}/${fontPath}";
|
||||
|
||||
time.timeZone = "Asia/Kolkata";
|
||||
|
||||
tux.services.openssh = {
|
||||
enable = true;
|
||||
ports = [8033];
|
||||
authorizedKeys = [
|
||||
"ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIL+OzPUe2ECPC929DqpkM39tl/vdNAXfsRnmrGfR+X3D ${email}"
|
||||
];
|
||||
};
|
||||
|
||||
user = {
|
||||
uid = 10225;
|
||||
gid = 10225;
|
||||
shell = "${pkgs.zsh}/bin/zsh";
|
||||
};
|
||||
|
||||
environment.etcBackupExtension = ".backup";
|
||||
environment.motd = '''';
|
||||
environment.packages = with pkgs; [
|
||||
nano
|
||||
git
|
||||
neovim
|
||||
openssh
|
||||
inputs.trok.packages."aarch64-linux".default
|
||||
];
|
||||
|
||||
home-manager = {
|
||||
config = ./home.nix;
|
||||
backupFileExtension = "backup";
|
||||
extraSpecialArgs = {inherit inputs outputs username email;};
|
||||
useGlobalPkgs = true;
|
||||
};
|
||||
|
||||
# Set up nix for flakes
|
||||
nix.extraOptions = ''
|
||||
experimental-features = nix-command flakes
|
||||
'';
|
||||
|
||||
system.stateVersion = "24.05";
|
||||
}
|
||||
35
hosts/rigel/home.nix
Normal file
@@ -0,0 +1,35 @@
|
||||
{pkgs, ...}: {
|
||||
imports = [
|
||||
../../modules/home/git
|
||||
../../modules/home/starship
|
||||
../../modules/home/fastfetch
|
||||
];
|
||||
|
||||
programs = {
|
||||
bat.enable = true;
|
||||
zoxide = {
|
||||
enable = true;
|
||||
options = ["--cmd cd"];
|
||||
};
|
||||
zsh = {
|
||||
enable = true;
|
||||
shellAliases = {
|
||||
ls = "lsd";
|
||||
};
|
||||
syntaxHighlighting.enable = true;
|
||||
autosuggestion.enable = true;
|
||||
initContent = ''
|
||||
fastfetch
|
||||
'';
|
||||
};
|
||||
};
|
||||
|
||||
home.packages = with pkgs; [
|
||||
neovim
|
||||
busybox
|
||||
lsd
|
||||
fastfetch
|
||||
];
|
||||
|
||||
home.stateVersion = "24.05";
|
||||
}
|
||||
56
hosts/sirius/default.nix
Normal file
@@ -0,0 +1,56 @@
|
||||
{
|
||||
pkgs,
|
||||
inputs,
|
||||
username,
|
||||
config,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
inputs.nixos-wsl.nixosModules.wsl
|
||||
|
||||
../common
|
||||
../../modules/nixos/virtualisation/docker.nix
|
||||
];
|
||||
|
||||
tux.services.openssh.enable = true;
|
||||
|
||||
boot.binfmt.emulatedSystems = ["aarch64-linux"];
|
||||
|
||||
nixpkgs = {
|
||||
config.cudaSupport = true;
|
||||
hostPlatform = "x86_64-linux";
|
||||
};
|
||||
|
||||
wsl = {
|
||||
enable = true;
|
||||
defaultUser = "${username}";
|
||||
useWindowsDriver = true;
|
||||
};
|
||||
|
||||
networking.hostName = "sirius";
|
||||
|
||||
programs = {
|
||||
ssh.startAgent = true;
|
||||
zsh.enable = true;
|
||||
|
||||
nix-ld = {
|
||||
enable = true;
|
||||
libraries = config.hardware.graphics.extraPackages;
|
||||
package = pkgs.nix-ld-rs;
|
||||
};
|
||||
|
||||
dconf.enable = true;
|
||||
};
|
||||
|
||||
environment.persistence."/persist" = {
|
||||
enable = false;
|
||||
};
|
||||
|
||||
home-manager.users.${username} = {
|
||||
imports = [
|
||||
./home.nix
|
||||
];
|
||||
};
|
||||
|
||||
system.stateVersion = "23.11";
|
||||
}
|
||||
3
hosts/sirius/home.nix
Normal file
@@ -0,0 +1,3 @@
|
||||
{...}: {
|
||||
home.stateVersion = "23.11";
|
||||
}
|
||||
66
hosts/vega/default.nix
Normal file
@@ -0,0 +1,66 @@
|
||||
{
|
||||
pkgs,
|
||||
username,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
./hardware.nix
|
||||
../common
|
||||
|
||||
../../modules/nixos/selfhosted/adguard.nix
|
||||
];
|
||||
|
||||
tux.services.openssh.enable = true;
|
||||
|
||||
boot.initrd.availableKernelModules = [
|
||||
"usbhid"
|
||||
"usb_storage"
|
||||
"vc4"
|
||||
"pcie_brcmstb" # required for the pcie bus to work
|
||||
"reset-raspberrypi" # required for vl805 firmware to load
|
||||
];
|
||||
|
||||
# Use the extlinux boot loader. (NixOS wants to enable GRUB by default)
|
||||
boot.loader.grub.enable = false;
|
||||
# Enables the generation of /boot/extlinux/extlinux.conf
|
||||
boot.loader.generic-extlinux-compatible.enable = true;
|
||||
|
||||
hardware.enableRedistributableFirmware = true;
|
||||
powerManagement.cpuFreqGovernor = "ondemand";
|
||||
|
||||
networking = {
|
||||
hostName = "vega";
|
||||
networkmanager = {
|
||||
enable = true;
|
||||
wifi.powersave = false;
|
||||
};
|
||||
firewall = {
|
||||
enable = true;
|
||||
allowedTCPPorts = [22];
|
||||
|
||||
# Facilitate firewall punching
|
||||
allowedUDPPorts = [41641];
|
||||
};
|
||||
};
|
||||
|
||||
services = {
|
||||
tailscale = {
|
||||
enable = true;
|
||||
extraUpFlags = ["--login-server https://hs.tux.rs"];
|
||||
};
|
||||
};
|
||||
|
||||
environment.systemPackages = with pkgs; [go-wol];
|
||||
|
||||
environment.persistence."/persist" = {
|
||||
enable = false;
|
||||
};
|
||||
|
||||
home-manager.users.${username} = {
|
||||
imports = [
|
||||
./home.nix
|
||||
];
|
||||
};
|
||||
|
||||
system.stateVersion = "24.11";
|
||||
}
|
||||
32
hosts/vega/hardware.nix
Normal file
@@ -0,0 +1,32 @@
|
||||
# Do not modify this file! It was generated by ‘nixos-generate-config’
|
||||
# and may be overwritten by future invocations. Please make changes
|
||||
# to /etc/nixos/configuration.nix instead.
|
||||
{ config, lib, pkgs, modulesPath, ... }:
|
||||
|
||||
{
|
||||
imports =
|
||||
[ (modulesPath + "/installer/scan/not-detected.nix")
|
||||
];
|
||||
|
||||
boot.initrd.availableKernelModules = [ ];
|
||||
boot.initrd.kernelModules = [ ];
|
||||
boot.kernelModules = [ ];
|
||||
boot.extraModulePackages = [ ];
|
||||
|
||||
fileSystems."/" =
|
||||
{ device = "/dev/disk/by-uuid/44444444-4444-4444-8888-888888888888";
|
||||
fsType = "ext4";
|
||||
};
|
||||
|
||||
swapDevices = [ ];
|
||||
|
||||
# Enables DHCP on each ethernet and wireless interface. In case of scripted networking
|
||||
# (the default) this is the recommended approach. When using systemd-networkd it's
|
||||
# still possible to use this option, but it's recommended to use it in conjunction
|
||||
# with explicit per-interface declarations with `networking.interfaces.<interface>.useDHCP`.
|
||||
networking.useDHCP = lib.mkDefault true;
|
||||
# networking.interfaces.enu1u1.useDHCP = lib.mkDefault true;
|
||||
# networking.interfaces.wlan0.useDHCP = lib.mkDefault true;
|
||||
|
||||
nixpkgs.hostPlatform = lib.mkDefault "aarch64-linux";
|
||||
}
|
||||
3
hosts/vega/home.nix
Normal file
@@ -0,0 +1,3 @@
|
||||
{...}: {
|
||||
home.stateVersion = "24.11";
|
||||
}
|
||||
101
hosts/vps/default.nix
Normal file
@@ -0,0 +1,101 @@
|
||||
{
|
||||
modulesPath,
|
||||
inputs,
|
||||
username,
|
||||
lib,
|
||||
...
|
||||
}: {
|
||||
imports = [
|
||||
(modulesPath + "/installer/scan/not-detected.nix")
|
||||
(modulesPath + "/profiles/qemu-guest.nix")
|
||||
inputs.disko.nixosModules.default
|
||||
(import ./disko.nix {device = "/dev/sda";})
|
||||
|
||||
../common
|
||||
];
|
||||
|
||||
tux.services.openssh.enable = true;
|
||||
|
||||
nixpkgs = {
|
||||
hostPlatform = "x86_64-linux";
|
||||
};
|
||||
|
||||
boot = {
|
||||
initrd.systemd = {
|
||||
enable = lib.mkForce true;
|
||||
|
||||
services.wipe-my-fs = {
|
||||
wantedBy = ["initrd.target"];
|
||||
after = ["initrd-root-device.target"];
|
||||
before = ["sysroot.mount"];
|
||||
unitConfig.DefaultDependencies = "no";
|
||||
serviceConfig.Type = "oneshot";
|
||||
script = ''
|
||||
mkdir /btrfs_tmp
|
||||
mount /dev/disk/by-partlabel/disk-primary-root /btrfs_tmp
|
||||
|
||||
if [[ -e /btrfs_tmp/root ]]; then
|
||||
mkdir -p /btrfs_tmp/old_roots
|
||||
timestamp=$(date --date="@$(stat -c %Y /btrfs_tmp/root)" "+%Y-%m-%-d_%H:%M:%S")
|
||||
mv /btrfs_tmp/root "/btrfs_tmp/old_roots/$timestamp"
|
||||
fi
|
||||
|
||||
delete_subvolume_recursively() {
|
||||
IFS=$'\n'
|
||||
for i in $(btrfs subvolume list -o "$1" | cut -f 9- -d ' '); do
|
||||
delete_subvolume_recursively "/btrfs_tmp/$i"
|
||||
done
|
||||
btrfs subvolume delete "$1"
|
||||
}
|
||||
|
||||
for i in $(find /btrfs_tmp/old_roots/ -maxdepth 1 -mtime +30); do
|
||||
delete_subvolume_recursively "$i"
|
||||
done
|
||||
|
||||
btrfs subvolume create /btrfs_tmp/root
|
||||
umount /btrfs_tmp
|
||||
'';
|
||||
};
|
||||
};
|
||||
|
||||
loader = {
|
||||
grub = {
|
||||
efiSupport = true;
|
||||
efiInstallAsRemovable = true;
|
||||
};
|
||||
};
|
||||
};
|
||||
|
||||
networking.hostName = "vps";
|
||||
|
||||
users = {
|
||||
users.${username} = {
|
||||
password = "${username}";
|
||||
hashedPasswordFile = lib.mkForce null;
|
||||
};
|
||||
};
|
||||
|
||||
programs.fuse.userAllowOther = true;
|
||||
fileSystems."/persist".neededForBoot = true;
|
||||
environment.persistence."/persist" = {
|
||||
hideMounts = true;
|
||||
directories = [
|
||||
"/var/log"
|
||||
"/var/lib/nixos"
|
||||
];
|
||||
files = [
|
||||
"/etc/ssh/ssh_host_ed25519_key"
|
||||
"/etc/ssh/ssh_host_ed25519_key.pub"
|
||||
"/etc/ssh/ssh_host_rsa_key"
|
||||
"/etc/ssh/ssh_host_rsa_key.pub"
|
||||
];
|
||||
};
|
||||
|
||||
home-manager.users.${username} = {
|
||||
imports = [
|
||||
./home.nix
|
||||
];
|
||||
};
|
||||
|
||||
system.stateVersion = "24.11";
|
||||
}
|
||||
53
hosts/vps/disko.nix
Normal file
@@ -0,0 +1,53 @@
|
||||
{device ? throw "Set this to the disk device, e.g. /dev/nvme0n1", ...}: {
|
||||
disko.devices.disk.primary = {
|
||||
inherit device;
|
||||
type = "disk";
|
||||
content = {
|
||||
type = "gpt"; # GPT partitioning scheme
|
||||
partitions = {
|
||||
boot = {
|
||||
name = "boot";
|
||||
size = "1M";
|
||||
type = "EF02";
|
||||
};
|
||||
# EFI Partition
|
||||
ESP = {
|
||||
size = "512M";
|
||||
type = "EF00";
|
||||
content = {
|
||||
type = "filesystem";
|
||||
format = "vfat";
|
||||
mountpoint = "/boot";
|
||||
mountOptions = ["defaults" "umask=0077"];
|
||||
};
|
||||
};
|
||||
# Btrfs Root Partition
|
||||
root = {
|
||||
size = "100%"; # Use remaining space
|
||||
type = "8300"; # Linux filesystem type
|
||||
content = {
|
||||
type = "btrfs";
|
||||
subvolumes = {
|
||||
"/root" = {
|
||||
mountOptions = ["compress=zstd"]; # Compression for better performance
|
||||
mountpoint = "/"; # Root subvolume
|
||||
};
|
||||
"/persist" = {
|
||||
mountOptions = ["compress=zstd"]; # Compression for persistent data
|
||||
mountpoint = "/persist"; # Persistent subvolume
|
||||
};
|
||||
"/nix" = {
|
||||
mountOptions = [
|
||||
"compress=zstd"
|
||||
"noatime"
|
||||
"noacl"
|
||||
]; # Optimize for Nix store
|
||||
mountpoint = "/nix"; # Nix subvolume
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
12
hosts/vps/home.nix
Normal file
@@ -0,0 +1,12 @@
|
||||
{username, ...}: {
|
||||
home.persistence."/persist/home/${username}" = {
|
||||
directories = [
|
||||
"Projects"
|
||||
".ssh"
|
||||
".local/share/zsh"
|
||||
];
|
||||
allowOther = true;
|
||||
};
|
||||
|
||||
home.stateVersion = "24.11";
|
||||
}
|
||||
11
modules/base/default.nix
Normal file
@@ -0,0 +1,11 @@
|
||||
{
|
||||
imports = [
|
||||
./nix.nix
|
||||
./nixpkgs.nix
|
||||
./nh.nix
|
||||
./overlays.nix
|
||||
./sops.nix
|
||||
./substituters.nix
|
||||
./user.nix
|
||||
];
|
||||
}
|
||||
16
modules/base/nh.nix
Normal file
@@ -0,0 +1,16 @@
|
||||
{
|
||||
config,
|
||||
username,
|
||||
...
|
||||
}: {
|
||||
programs.nh = {
|
||||
enable = true;
|
||||
|
||||
clean = {
|
||||
enable = !config.nix.gc.automatic;
|
||||
dates = "weekly";
|
||||
};
|
||||
|
||||
flake = "/home/${username}/Projects/nixos-config";
|
||||
};
|
||||
}
|
||||
27
modules/base/nix.nix
Normal file
@@ -0,0 +1,27 @@
|
||||
{
|
||||
pkgs,
|
||||
username,
|
||||
...
|
||||
}: {
|
||||
nix = {
|
||||
package = pkgs.lix;
|
||||
|
||||
gc = {
|
||||
automatic = true;
|
||||
options = "--delete-older-than 3d";
|
||||
};
|
||||
|
||||
channel.enable = false;
|
||||
|
||||
settings = {
|
||||
extra-platforms = ["aarch64-linux" "arm-linux"];
|
||||
auto-optimise-store = true;
|
||||
allowed-users = ["${username}"];
|
||||
trusted-users = ["${username}"];
|
||||
experimental-features = "nix-command flakes";
|
||||
keep-going = true;
|
||||
warn-dirty = false;
|
||||
http-connections = 50;
|
||||
};
|
||||
};
|
||||
}
|
||||
8
modules/base/nixpkgs.nix
Normal file
@@ -0,0 +1,8 @@
|
||||
{
|
||||
nixpkgs = {
|
||||
config = {
|
||||
allowUnfree = true;
|
||||
joypixels.acceptLicense = true;
|
||||
};
|
||||
};
|
||||
}
|
||||
9
modules/base/overlays.nix
Normal file
@@ -0,0 +1,9 @@
|
||||
{outputs, ...}: {
|
||||
nixpkgs.overlays = [
|
||||
outputs.overlays.additions
|
||||
outputs.overlays.modifications
|
||||
outputs.overlays.stable-packages
|
||||
outputs.overlays.nur
|
||||
outputs.overlays.nix-vscode-extensions
|
||||
];
|
||||
}
|
||||
20
modules/base/sops.nix
Normal file
@@ -0,0 +1,20 @@
|
||||
{
|
||||
inputs,
|
||||
config,
|
||||
pkgs,
|
||||
...
|
||||
}: let
|
||||
isEd25519 = k: k.type == "ed25519";
|
||||
getKeyPath = k: k.path;
|
||||
keys = builtins.filter isEd25519 config.services.openssh.hostKeys;
|
||||
in {
|
||||
imports = [inputs.sops-nix.nixosModules.sops];
|
||||
|
||||
sops.age = {
|
||||
sshKeyPaths = map getKeyPath keys;
|
||||
keyFile = "/var/lib/sops-nix/key.txt";
|
||||
generateKey = true;
|
||||
};
|
||||
|
||||
environment.systemPackages = with pkgs; [sops];
|
||||
}
|
||||
27
modules/base/substituters.nix
Normal file
@@ -0,0 +1,27 @@
|
||||
{
|
||||
nix.settings = {
|
||||
substituters = [
|
||||
"https://cache.nixos.org?priority=10"
|
||||
"https://anyrun.cachix.org"
|
||||
"https://fufexan.cachix.org"
|
||||
"https://helix.cachix.org"
|
||||
"https://hyprland.cachix.org"
|
||||
"https://nix-community.cachix.org"
|
||||
"https://nix-gaming.cachix.org"
|
||||
"https://yazi.cachix.org"
|
||||
"https://nix-on-droid.cachix.org"
|
||||
];
|
||||
trusted-substituters = ["https://nix-on-droid.cachix.org"];
|
||||
trusted-public-keys = [
|
||||
"cache.nixos.org-1:6NCHdD59X431o0gWypbMrAURkbJ16ZPMQFGspcDShjY="
|
||||
"anyrun.cachix.org-1:pqBobmOjI7nKlsUMV25u9QHa9btJK65/C8vnO3p346s="
|
||||
"fufexan.cachix.org-1:LwCDjCJNJQf5XD2BV+yamQIMZfcKWR9ISIFy5curUsY="
|
||||
"helix.cachix.org-1:ejp9KQpR1FBI2onstMQ34yogDm4OgU2ru6lIwPvuCVs="
|
||||
"hyprland.cachix.org-1:a7pgxzMz7+chwVL3/pzj6jIBMioiJM7ypFP8PwtkuGc="
|
||||
"nix-community.cachix.org-1:mB9FSh9qf2dCimDSUo8Zy7bkq5CX+/rkCWyvRCYg3Fs="
|
||||
"nix-gaming.cachix.org-1:nbjlureqMbRAxR1gJ/f3hxemL9svXaZF/Ees8vCUUs4="
|
||||
"yazi.cachix.org-1:Dcdz63NZKfvUCbDGngQDAZq6kOroIrFoyO064uvLh8k="
|
||||
"nix-on-droid.cachix.org-1:56snoMJTXmDRC1Ei24CmKoUqvHJ9XCp+nidK7qkMQrU="
|
||||
];
|
||||
};
|
||||
}
|
||||
20
modules/base/user.nix
Normal file
@@ -0,0 +1,20 @@
|
||||
{
|
||||
config,
|
||||
pkgs,
|
||||
username,
|
||||
email,
|
||||
...
|
||||
}: {
|
||||
users = {
|
||||
mutableUsers = false;
|
||||
defaultUserShell = pkgs.zsh;
|
||||
users.${username} = {
|
||||
hashedPasswordFile = config.sops.secrets.tux-password.path;
|
||||
isNormalUser = true;
|
||||
extraGroups = ["networkmanager" "wheel" "storage"];
|
||||
openssh.authorizedKeys.keys = [
|
||||
''ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIL+OzPUe2ECPC929DqpkM39tl/vdNAXfsRnmrGfR+X3D ${email}''
|
||||
];
|
||||
};
|
||||
};
|
||||
}
|
||||
106
modules/droid/sshd.nix
Normal file
@@ -0,0 +1,106 @@
|
||||
{
|
||||
config,
|
||||
lib,
|
||||
pkgs,
|
||||
...
|
||||
}: let
|
||||
# utility functions
|
||||
concatLines = list: builtins.concatStringsSep "\n" list;
|
||||
|
||||
prefixLines = mapper: list: concatLines (map mapper list);
|
||||
|
||||
# could be put in the config
|
||||
configPath = "ssh/sshd_config";
|
||||
|
||||
keysFolder = "/etc/ssh";
|
||||
|
||||
authorizedKeysFolder = "/etc/ssh/authorized_keys.d";
|
||||
|
||||
supportedKeysTypes = [
|
||||
"rsa"
|
||||
"ed25519"
|
||||
];
|
||||
|
||||
sshd-start-bin = "sshd-start";
|
||||
|
||||
# real config
|
||||
cfg = config.tux.services.openssh;
|
||||
|
||||
pathOfKeyOf = type: "${keysFolder}/ssh_host_${type}_key";
|
||||
|
||||
generateKeyOf = type: ''
|
||||
${lib.getExe' pkgs.openssh "ssh-keygen"} \
|
||||
-t "${type}" \
|
||||
-f "${pathOfKeyOf type}" \
|
||||
-N ""
|
||||
'';
|
||||
|
||||
generateKeyWhenNeededOf = type: ''
|
||||
if [ ! -f ${pathOfKeyOf type} ]; then
|
||||
mkdir --parents ${keysFolder}
|
||||
${generateKeyOf type}
|
||||
fi
|
||||
'';
|
||||
|
||||
sshd-start = pkgs.writeScriptBin sshd-start-bin ''
|
||||
#!${pkgs.runtimeShell}
|
||||
${prefixLines generateKeyWhenNeededOf supportedKeysTypes}
|
||||
|
||||
mkdir --parents "${authorizedKeysFolder}"
|
||||
echo "${lib.concatStringsSep "\n" cfg.authorizedKeys}" > ${authorizedKeysFolder}/${config.user.userName}
|
||||
|
||||
echo "Starting sshd in non-daemonized way on port ${lib.concatMapStrings toString cfg.ports}"
|
||||
${lib.getExe' pkgs.openssh "sshd"} \
|
||||
-f "/etc/${configPath}" \
|
||||
-D # don't detach into a daemon process
|
||||
'';
|
||||
in {
|
||||
options = {
|
||||
tux.services.openssh = {
|
||||
enable = lib.mkEnableOption ''
|
||||
Whether to enable the OpenSSH secure shell daemon, which
|
||||
allows secure remote logins.
|
||||
'';
|
||||
|
||||
ports = lib.mkOption {
|
||||
type = lib.types.listOf lib.types.port;
|
||||
default = [22];
|
||||
description = ''
|
||||
Specifies on which ports the SSH daemon listens.
|
||||
'';
|
||||
};
|
||||
|
||||
authorizedKeys = lib.mkOption {
|
||||
type = lib.types.listOf lib.types.str;
|
||||
default = [];
|
||||
description = ''
|
||||
Specify a list of public keys to be added to the authorized_keys file.
|
||||
'';
|
||||
};
|
||||
};
|
||||
};
|
||||
|
||||
config = lib.mkIf cfg.enable {
|
||||
environment.etc = {
|
||||
"${configPath}".text = ''
|
||||
${prefixLines (port: "Port ${toString port}") cfg.ports}
|
||||
|
||||
AuthorizedKeysFile ${authorizedKeysFolder}/%u
|
||||
|
||||
LogLevel VERBOSE
|
||||
'';
|
||||
};
|
||||
|
||||
environment.packages = [
|
||||
sshd-start
|
||||
pkgs.openssh
|
||||
];
|
||||
|
||||
build.activationAfter.sshd = ''
|
||||
SERVER_PID=$(${lib.getExe' pkgs.procps "ps"} -a | ${lib.getExe' pkgs.toybox "grep"} sshd || true)
|
||||
if [ -z "$SERVER_PID" ]; then
|
||||
$DRY_RUN_CMD ${lib.getExe sshd-start}
|
||||
fi
|
||||
'';
|
||||
};
|
||||
}
|
||||
69
modules/home/alacritty/default.nix
Executable file
@@ -0,0 +1,69 @@
|
||||
{...}: {
|
||||
programs.alacritty = {
|
||||
enable = true;
|
||||
|
||||
settings = {
|
||||
font = {
|
||||
normal.family = "JetBrainsMono Nerd Font";
|
||||
bold.family = "JetBrainsMono Nerd Font";
|
||||
italic.family = "JetBrainsMono Nerd Font";
|
||||
bold_italic.family = "JetBrainsMono Nerd Font";
|
||||
size = 16;
|
||||
};
|
||||
|
||||
window = {
|
||||
padding = {
|
||||
x = 15;
|
||||
y = 15;
|
||||
};
|
||||
|
||||
decorations = "none";
|
||||
opacity = 1.0;
|
||||
dynamic_title = true;
|
||||
};
|
||||
|
||||
selection.save_to_clipboard = false;
|
||||
|
||||
general.live_config_reload = true;
|
||||
|
||||
colors = {
|
||||
primary = {
|
||||
background = "#0d0f18";
|
||||
foreground = "#a5b6cf";
|
||||
};
|
||||
normal = {
|
||||
black = "#1c1e27";
|
||||
blue = "#8baff1";
|
||||
cyan = "#98d3ee";
|
||||
green = "#95d3af";
|
||||
magenta = "#c79bf0";
|
||||
red = "#e26c7c";
|
||||
white = "#d0d3d8";
|
||||
yellow = "#f1d8a5";
|
||||
};
|
||||
bright = {
|
||||
black = "#151720";
|
||||
blue = "#86aaec";
|
||||
cyan = "#93cee9";
|
||||
green = "#90ceaa";
|
||||
magenta = "#c296eb";
|
||||
red = "#dd6777";
|
||||
white = "#cbced3";
|
||||
yellow = "#ecd3a0";
|
||||
};
|
||||
cursor = {
|
||||
cursor = "#a5b6cf";
|
||||
text = "CellForeground";
|
||||
};
|
||||
selection = {
|
||||
text = "CellForeground";
|
||||
background = "0x303340";
|
||||
};
|
||||
vi_mode_cursor = {
|
||||
text = "CellBackground";
|
||||
cursor = "CellForeground";
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
44
modules/home/aria2/default.nix
Normal file
@@ -0,0 +1,44 @@
|
||||
{...}: {
|
||||
programs.aria2 = {
|
||||
enable = true;
|
||||
settings = {
|
||||
file-allocation = "none";
|
||||
log-level = "warn";
|
||||
max-connection-per-server = 16;
|
||||
min-split-size = "1M";
|
||||
human-readable = true;
|
||||
reuse-uri = true;
|
||||
rpc-save-upload-metadata = true;
|
||||
max-file-not-found = 0;
|
||||
remote-time = true;
|
||||
async-dns = true;
|
||||
stop = 0;
|
||||
allow-piece-length-change = true;
|
||||
optimize-concurrent-downloads = true;
|
||||
deferred-input = true;
|
||||
continue = true;
|
||||
check-integrity = true;
|
||||
realtime-chunk-checksum = true;
|
||||
piece-length = "1M";
|
||||
split = 16;
|
||||
# Seconds:
|
||||
save-session-interval = 60;
|
||||
# Caches in memory
|
||||
disk-cache = "32M";
|
||||
save-not-found = true;
|
||||
download-result = "full";
|
||||
truncate-console-readout = true;
|
||||
retry-wait = 30;
|
||||
max-tries = 15;
|
||||
enable-color = true;
|
||||
enable-http-keep-alive = true;
|
||||
enable-http-pipelining = true;
|
||||
http-accept-gzip = true;
|
||||
follow-torrent = true;
|
||||
bt-save-metadata = true;
|
||||
seed-time = 0;
|
||||
bt-load-saved-metadata = true;
|
||||
metalink-preferred-protocol = "https";
|
||||
};
|
||||
};
|
||||
}
|
||||
7
modules/home/barrier/default.nix
Executable file
@@ -0,0 +1,7 @@
|
||||
{pkgs, ...}: {
|
||||
# services.barrier.client.enable = true;
|
||||
|
||||
home.packages = with pkgs; [
|
||||
barrier
|
||||
];
|
||||
}
|
||||
17
modules/home/bitwarden/default.nix
Normal file
@@ -0,0 +1,17 @@
|
||||
{
|
||||
pkgs,
|
||||
email,
|
||||
...
|
||||
}: {
|
||||
programs.rbw = {
|
||||
enable = true;
|
||||
settings = {
|
||||
base_url = "https://bw.tux.rs";
|
||||
email = "${email}";
|
||||
};
|
||||
};
|
||||
|
||||
home.packages = with pkgs; [
|
||||
bitwarden
|
||||
];
|
||||
}
|
||||
16
modules/home/brave/default.nix
Normal file
@@ -0,0 +1,16 @@
|
||||
{pkgs, ...}: {
|
||||
programs.chromium = {
|
||||
enable = true;
|
||||
package = pkgs.brave;
|
||||
extensions = [
|
||||
{id = "nkbihfbeogaeaoehlefnkodbefgpgknn";} # Metamask
|
||||
{id = "gppongmhjkpfnbhagpmjfkannfbllamg";} # Wappalyzer
|
||||
{id = "nngceckbapebfimnlniiiahkandclblb";} # Bitwarden
|
||||
{id = "bfnaelmomeimhlpmgjnjophhpkkoljpa";} # Phantom
|
||||
{id = "eimadpbcbfnmbkopoojfekhnkhdbieeh";} # DarkReader
|
||||
];
|
||||
commandLineArgs = [
|
||||
"--disable-features=WebRtcAllowInputVolumeAdjustment"
|
||||
];
|
||||
};
|
||||
}
|
||||
8
modules/home/desktop/awesome/default.nix
Normal file
@@ -0,0 +1,8 @@
|
||||
{pkgs, ...}: {
|
||||
home.file = {
|
||||
".config/awesome" = {
|
||||
recursive = true;
|
||||
source = "${pkgs.tawm}";
|
||||
};
|
||||
};
|
||||
}
|
||||
271
modules/home/desktop/hyprland/default.nix
Normal file
@@ -0,0 +1,271 @@
|
||||
{pkgs, ...}: {
|
||||
home.packages = with pkgs; [astal];
|
||||
|
||||
wayland.windowManager.hyprland = {
|
||||
enable = true;
|
||||
package = null;
|
||||
portalPackage = null;
|
||||
xwayland.enable = true;
|
||||
systemd.variables = ["--all"];
|
||||
|
||||
plugins = with pkgs.hyprland-plugins; [
|
||||
hyprexpo
|
||||
];
|
||||
|
||||
settings = let
|
||||
# Hyprland
|
||||
border_size = 0;
|
||||
gaps_in = 5;
|
||||
gaps_out = 10;
|
||||
gaps_ws = -10;
|
||||
rounding = 8;
|
||||
active_border_col = "rgba(90ceaaff) rgba(ecd3a0ff) 45deg";
|
||||
inactive_border_col = "rgba(86aaeccc) rgba(93cee9cc) 45deg";
|
||||
|
||||
# Apps
|
||||
terminal = "wezterm";
|
||||
floating_terminal = "wezterm start --class wezterm-floating";
|
||||
editor = "wezterm -e nvim";
|
||||
browser = "brave";
|
||||
filemanager = "thunar";
|
||||
in {
|
||||
#-- Output
|
||||
# See https://wiki.hyprland.org/Configuring/Monitors
|
||||
monitor = ",preferred,auto,1";
|
||||
|
||||
#-- Input: Keyboard, Mouse, Touchpad
|
||||
input = {
|
||||
sensitivity = 0;
|
||||
scroll_method = "2 fg";
|
||||
natural_scroll = true;
|
||||
touchpad = {
|
||||
natural_scroll = true;
|
||||
clickfinger_behavior = false;
|
||||
};
|
||||
};
|
||||
|
||||
#-- General
|
||||
# See https://wiki.hyprland.org/Configuring/Variables
|
||||
general = {
|
||||
border_size = border_size;
|
||||
gaps_in = gaps_in;
|
||||
gaps_out = gaps_out;
|
||||
gaps_workspaces = gaps_ws;
|
||||
layout = "master";
|
||||
resize_on_border = true;
|
||||
|
||||
"col.active_border" = active_border_col;
|
||||
"col.inactive_border" = inactive_border_col;
|
||||
};
|
||||
|
||||
ecosystem = {
|
||||
no_update_news = true;
|
||||
no_donation_nag = true;
|
||||
};
|
||||
|
||||
#-- Decoration
|
||||
# See https://wiki.hyprland.org/Configuring/Variables/#decoration
|
||||
decoration = {
|
||||
rounding = rounding;
|
||||
active_opacity = 0.95;
|
||||
inactive_opacity = 0.95;
|
||||
fullscreen_opacity = 1.0;
|
||||
|
||||
blur = {
|
||||
enabled = true;
|
||||
size = 6;
|
||||
passes = 3;
|
||||
new_optimizations = true;
|
||||
xray = true;
|
||||
special = true;
|
||||
brightness = 1;
|
||||
noise = 0.01;
|
||||
contrast = 1;
|
||||
popups = true;
|
||||
popups_ignorealpha = 0.6;
|
||||
};
|
||||
|
||||
shadow = {
|
||||
enabled = false;
|
||||
};
|
||||
};
|
||||
|
||||
#-- Animations
|
||||
# See https://wiki.hyprland.org/Configuring/Animations
|
||||
animations = {
|
||||
enabled = true;
|
||||
|
||||
bezier = [
|
||||
"linear, 0, 0, 1, 1"
|
||||
"md3_standard, 0.2, 0, 0, 1"
|
||||
"md3_decel, 0.05, 0.7, 0.1, 1"
|
||||
"md3_accel, 0.3, 0, 0.8, 0.15"
|
||||
"overshot, 0.05, 0.9, 0.1, 1.1"
|
||||
"crazyshot, 0.1, 1.5, 0.76, 0.92"
|
||||
"hyprnostretch, 0.05, 0.9, 0.1, 1.0"
|
||||
"menu_decel, 0.1, 1, 0, 1"
|
||||
"menu_accel, 0.38, 0.04, 1, 0.07"
|
||||
"easeInOutCirc, 0.85, 0, 0.15, 1"
|
||||
"easeOutCirc, 0, 0.55, 0.45, 1"
|
||||
"easeOutExpo, 0.16, 1, 0.3, 1"
|
||||
"softAcDecel, 0.26, 0.26, 0.15, 1"
|
||||
"md2, 0.4, 0, 0.2, 1" # use with .2s duration
|
||||
];
|
||||
|
||||
animation = [
|
||||
"windows, 1, 3, md3_decel, popin 60%"
|
||||
"windowsIn, 1, 3, md3_decel, popin 60%"
|
||||
"windowsOut, 1, 3, md3_accel, popin 60%"
|
||||
"border, 1, 10, default"
|
||||
"fade, 1, 3, md3_decel"
|
||||
"layersIn, 1, 3, menu_decel, slide"
|
||||
"layersOut, 1, 1.6, menu_accel"
|
||||
"fadeLayersIn, 1, 3, menu_decel"
|
||||
"fadeLayersOut, 1, 1.6, menu_accel"
|
||||
"workspaces, 1, 7, menu_decel, slide"
|
||||
"specialWorkspace, 1, 3, md3_decel, slidevert"
|
||||
];
|
||||
};
|
||||
|
||||
#-- Layout : Master
|
||||
# See https://wiki.hyprland.org/Configuring/Master-Layout
|
||||
master = {
|
||||
allow_small_split = false;
|
||||
special_scale_factor = 0.8;
|
||||
mfact = 0.5;
|
||||
new_on_top = false;
|
||||
orientation = "left";
|
||||
inherit_fullscreen = true;
|
||||
smart_resizing = true;
|
||||
drop_at_cursor = true;
|
||||
};
|
||||
|
||||
#-- Window Rules
|
||||
# See https://wiki.hyprland.org/Configuring/Window-Rules
|
||||
windowrulev2 = [
|
||||
"float, class:com.github.hluk.copyq"
|
||||
"size 800 600, class:com.github.hluk.copyq"
|
||||
|
||||
"float, class:org.pulseaudio.pavucontrol"
|
||||
"size 800 600, class:org.pulseaudio.pavucontrol"
|
||||
|
||||
"float, class:com.ghostty.floating"
|
||||
"size 900 700, class:com.ghostty.floating"
|
||||
|
||||
"float, class:GalaxyBudsClient"
|
||||
"size 900 700, class:GalaxyBudsClient"
|
||||
|
||||
"workspace 3 silent, class:(firefox|Brave-browser)"
|
||||
"workspace 5 silent, class:(discord|Spotify|org.telegram.desktop)"
|
||||
];
|
||||
|
||||
plugin = {
|
||||
hyprexpo = {
|
||||
columns = 3;
|
||||
gap_size = 5;
|
||||
bg_col = "rgb(111111)";
|
||||
workspace_method = "center current";
|
||||
|
||||
enable_gesture = true;
|
||||
gesture_fingers = 3;
|
||||
gesture_distance = 300;
|
||||
gesture_positive = true;
|
||||
};
|
||||
};
|
||||
|
||||
bind = [
|
||||
# apps
|
||||
"SUPER, Return, exec, ${terminal}"
|
||||
"SUPER, A, exec, astal -t app-launcher"
|
||||
"SUPER, F, exec, ${filemanager}"
|
||||
"SUPER, E, exec, ${editor}"
|
||||
"SUPER, B, exec, ${browser}"
|
||||
"SUPER, G, exec, GalaxyBudsClient"
|
||||
"SUPER, D, exec, discord"
|
||||
"SUPER, S, exec, spotify"
|
||||
"SUPER, V, exec, copyq show"
|
||||
|
||||
"SUPER_SHIFT, Return, exec, ${floating_terminal}"
|
||||
"SUPER_SHIFT, S, exec, flameshot gui"
|
||||
|
||||
# astal
|
||||
"SUPER_SHIFT, R, exec, astal -q; ${pkgs.tpanel}/bin/tpanel"
|
||||
"SUPER_SHIFT, B, exec, astal toggle-bar"
|
||||
|
||||
# hyprland
|
||||
"SUPER, Q, killactive"
|
||||
"SUPER, grave, hyprexpo:expo, toggle"
|
||||
"SUPER_SHIFT, Q, forcekillactive"
|
||||
"SUPER_SHIFT, F, fullscreen, 0"
|
||||
"SUPER_SHIFT, Space, togglefloating"
|
||||
|
||||
# shutdown
|
||||
"SUPER_SHIFT, P, exec, poweroff"
|
||||
|
||||
# change focus
|
||||
"SUPER, left, movefocus, l"
|
||||
"SUPER, right, movefocus, r"
|
||||
"SUPER, up, movefocus, u"
|
||||
"SUPER, down, movefocus, d"
|
||||
|
||||
# move active
|
||||
"SUPER_SHIFT, left, movewindow, l"
|
||||
"SUPER_SHIFT, right, movewindow, r"
|
||||
"SUPER_SHIFT, up, movewindow, u"
|
||||
"SUPER_SHIFT, down, movewindow, d"
|
||||
|
||||
# workspaces
|
||||
"SUPER, 1, workspace, 1"
|
||||
"SUPER, 2, workspace, 2"
|
||||
"SUPER, 3, workspace, 3"
|
||||
"SUPER, 4, workspace, 4"
|
||||
"SUPER, 5, workspace, 5"
|
||||
|
||||
# send to workspaces
|
||||
"SUPER_SHIFT, 1, movetoworkspacesilent, 1"
|
||||
"SUPER_SHIFT, 2, movetoworkspacesilent, 2"
|
||||
"SUPER_SHIFT, 3, movetoworkspacesilent, 3"
|
||||
"SUPER_SHIFT, 4, movetoworkspacesilent, 4"
|
||||
"SUPER_SHIFT, 5, movetoworkspacesilent, 5"
|
||||
];
|
||||
|
||||
binde = [
|
||||
# resize active
|
||||
"SUPER_CTRL, left, resizeactive, -20 0"
|
||||
"SUPER_CTRL, right, resizeactive, 20 0"
|
||||
"SUPER_CTRL, up, resizeactive, 0 -20"
|
||||
"SUPER_CTRL, down, resizeactive, 0 20"
|
||||
|
||||
# move active (Floating Only)
|
||||
"SUPER_ALT, left, moveactive, -20 0"
|
||||
"SUPER_ALT, right, moveactive, 20 0"
|
||||
"SUPER_ALT, up, moveactive, 0 -20"
|
||||
"SUPER_ALT, down, moveactive, 0 20"
|
||||
|
||||
# speaker and mic volume control
|
||||
" , XF86AudioRaiseVolume, exec, wpctl set-volume -l 1 @DEFAULT_AUDIO_SINK@ 10%+"
|
||||
" , XF86AudioLowerVolume, exec, wpctl set-volume -l 1 @DEFAULT_AUDIO_SINK@ 10%-"
|
||||
" , XF86AudioMute, exec, wpctl set-mute @DEFAULT_AUDIO_SINK@ toggle"
|
||||
" , XF86AudioMicMute, exec, wpctl set-mute @DEFAULT_AUDIO_SOURCE@ toggle"
|
||||
|
||||
# display and keyboard brightness control
|
||||
" , XF86MonBrightnessUp, exec, brightnessctl s +20%"
|
||||
" , XF86MonBrightnessDown, exec, brightnessctl s 20%-"
|
||||
" , XF86KbdBrightnessUp, exec, asusctl -n"
|
||||
" , XF86KbdBrightnessDown, exec, asusctl -p"
|
||||
|
||||
# performance
|
||||
" , XF86Launch4, exec, asusctl profile -n"
|
||||
];
|
||||
|
||||
"exec-once" = [
|
||||
# load hyprland plugins
|
||||
"hyprctl plugin load '$HYPR_PLUGIN_DIR/lib/libhyprexpo.so'"
|
||||
|
||||
"${pkgs.swaybg}/bin/swaybg -i ~/Wallpapers/city.png"
|
||||
"${pkgs.tpanel}/bin/tpanel"
|
||||
"copyq"
|
||||
];
|
||||
};
|
||||
};
|
||||
}
|
||||
317
modules/home/desktop/rofi/default.nix
Normal file
@@ -0,0 +1,317 @@
|
||||
{config, ...}: {
|
||||
programs.rofi = {
|
||||
enable = true;
|
||||
extraConfig = {
|
||||
terminal = "alacritty";
|
||||
|
||||
modes = "combi,keys";
|
||||
|
||||
display-window = "window";
|
||||
display-drun = "run";
|
||||
display-windowcd = "windowcd";
|
||||
display-run = "run";
|
||||
display-ssh = "ssh";
|
||||
display-combi = "combi";
|
||||
display-keys = "keys";
|
||||
display-filebrowser = "filebrowser";
|
||||
|
||||
combi-modes = "window,drun";
|
||||
combi-hide-mode-prefix = false;
|
||||
combi-display-format = "<i>{mode}</i> {text}";
|
||||
|
||||
window-format = "<span fgalpha='65%'>[{w=-1}] </span><b>{c=-1}</b> <span weight='light' fgalpha='65%' size='small'>{t=-1}</span>";
|
||||
window-thumbnail = false;
|
||||
|
||||
drun-url-launcher = "xdg-open";
|
||||
drun-match-fields = "name,generic,exec,categories,keywords";
|
||||
drun-display-format = "<b>{name}</b>[ <span weight='light' size='small'><i>({generic})</i></span>][ <span weight='light' fgalpha='65%' size='small'>{exec}</span>]";
|
||||
drun-show-actions = true;
|
||||
|
||||
run-command = "{cmd}";
|
||||
run-list-command = "";
|
||||
run-shell-command = "{terminal} -e {cmd}";
|
||||
|
||||
matching = "normal";
|
||||
font = "JetBrains Mono 11";
|
||||
show-icons = true;
|
||||
scroll-method = 0;
|
||||
cycle = false;
|
||||
fixed-num-lines = false;
|
||||
};
|
||||
theme = let
|
||||
inherit (config.lib.formats.rasi) mkLiteral;
|
||||
in {
|
||||
"*" = {
|
||||
font = "JetBrains Mono 11";
|
||||
|
||||
black = mkLiteral "#1d1f21";
|
||||
white = mkLiteral "#c5c8c6";
|
||||
red = mkLiteral "#cc6666";
|
||||
orange = mkLiteral "#de935f";
|
||||
yellow = mkLiteral "#f0c674";
|
||||
green = mkLiteral "#7cb36b";
|
||||
cyan = mkLiteral "#78bab9";
|
||||
blue = mkLiteral "#81a2be";
|
||||
magenta = mkLiteral "#b294bb";
|
||||
|
||||
black-bright = mkLiteral "#3c4044";
|
||||
white-bright = mkLiteral "#eaeaea";
|
||||
red-bright = mkLiteral "#d54e53";
|
||||
orange-bright = mkLiteral "#e78c45";
|
||||
yellow-bright = mkLiteral "#e7c547";
|
||||
green-bright = mkLiteral "#71c464";
|
||||
cyan-bright = mkLiteral "#6acdcc";
|
||||
blue-bright = mkLiteral "#7aa6da";
|
||||
magenta-bright = mkLiteral "#c397d8";
|
||||
|
||||
black-66 = mkLiteral "#131415";
|
||||
white-66 = mkLiteral "#828382";
|
||||
red-66 = mkLiteral "#864343";
|
||||
orange-66 = mkLiteral "#92613e";
|
||||
yellow-66 = mkLiteral "#9e824c";
|
||||
green-66 = mkLiteral "#517646";
|
||||
cyan-66 = mkLiteral "#4f7a7a";
|
||||
blue-66 = mkLiteral "#556a7d";
|
||||
magenta-66 = mkLiteral "#75617b";
|
||||
|
||||
black-33 = mkLiteral "#090a0a";
|
||||
white-33 = mkLiteral "#414141";
|
||||
red-33 = mkLiteral "#432121";
|
||||
orange-33 = mkLiteral "#49301f";
|
||||
yellow-33 = mkLiteral "#4f4126";
|
||||
green-33 = mkLiteral "#283b23";
|
||||
cyan-33 = mkLiteral "#273d3d";
|
||||
blue-33 = mkLiteral "#2a353e";
|
||||
magenta-33 = mkLiteral "#3a303d";
|
||||
|
||||
common-background = mkLiteral "@black";
|
||||
common-background-bright = mkLiteral "@black-bright";
|
||||
common-background-66 = " @black-66";
|
||||
common-foreground = mkLiteral "@white";
|
||||
common-foreground-bright = mkLiteral "@white-bright";
|
||||
common-foreground-66 = mkLiteral "@white-66";
|
||||
common-primary = mkLiteral "@yellow";
|
||||
common-primary-bright = mkLiteral "@yellow-bright";
|
||||
common-primary-66 = mkLiteral "@yellow-66";
|
||||
common-primary-33 = mkLiteral "@yellow-33";
|
||||
common-secondary = mkLiteral "@blue";
|
||||
common-secondary-bright = mkLiteral "@blue-bright";
|
||||
common-secondary-66 = mkLiteral "@blue-66";
|
||||
common-secondary-33 = mkLiteral "@blue-33";
|
||||
common-urgent = mkLiteral "@red";
|
||||
common-urgent-bright = mkLiteral "@red-bright";
|
||||
common-urgent-66 = mkLiteral "@red-66";
|
||||
common-urgent-33 = mkLiteral "@red-33";
|
||||
|
||||
background-color = mkLiteral "transparent";
|
||||
|
||||
normal-normal-background = mkLiteral "transparent";
|
||||
normal-normal-foreground = mkLiteral "@common-foreground";
|
||||
normal-normal-border-color = mkLiteral "transparent";
|
||||
normal-active-background = mkLiteral "transparent";
|
||||
normal-active-foreground = mkLiteral "@common-secondary-bright";
|
||||
normal-active-border-color = mkLiteral "transparent";
|
||||
normal-urgent-background = mkLiteral "transparent";
|
||||
normal-urgent-foreground = mkLiteral "@common-urgent-bright";
|
||||
normal-urgent-border-color = mkLiteral "transparent";
|
||||
|
||||
selected-normal-background = mkLiteral "@common-primary-33";
|
||||
selected-normal-foreground = mkLiteral "@common-primary-bright";
|
||||
selected-normal-border-color = mkLiteral "@common-primary-66";
|
||||
selected-active-background = mkLiteral "@common-secondary-33";
|
||||
selected-active-foreground = mkLiteral "@common-secondary-bright";
|
||||
selected-active-border-color = mkLiteral "@common-secondary-66";
|
||||
selected-urgent-background = mkLiteral "@common-urgent-33";
|
||||
selected-urgent-foreground = mkLiteral "@common-urgent-bright";
|
||||
selected-urgent-border-color = mkLiteral "@common-urgent-66";
|
||||
|
||||
alternate-normal-background = mkLiteral "@normal-normal-background";
|
||||
alternate-normal-foreground = mkLiteral "@normal-normal-foreground";
|
||||
alternate-normal-border-color = mkLiteral "@normal-normal-border-color";
|
||||
alternate-active-background = mkLiteral "@normal-active-background";
|
||||
alternate-active-foreground = mkLiteral "@normal-active-foreground";
|
||||
alternate-active-border-color = mkLiteral "@normal-active-border-color";
|
||||
alternate-urgent-background = mkLiteral "@normal-urgent-background";
|
||||
alternate-urgent-foreground = mkLiteral "@normal-urgent-foreground";
|
||||
alternate-urgent-border-color = mkLiteral "@normal-urgent-border-color";
|
||||
};
|
||||
|
||||
"window" = {
|
||||
background-color = mkLiteral "#1d1f21e6"; #// @black + 0.85 alpha
|
||||
border = 3;
|
||||
border-color = mkLiteral "@black-bright";
|
||||
border-radius = 16;
|
||||
width = 1024;
|
||||
height = 460;
|
||||
};
|
||||
|
||||
"mainbox" = {
|
||||
padding = 16;
|
||||
spacing = 16;
|
||||
};
|
||||
|
||||
"inputbar" = {
|
||||
background-color = mkLiteral "#333537"; #// @black-110
|
||||
border = 1;
|
||||
border-color = mkLiteral "#606263"; #// @black-130
|
||||
border-radius = 8;
|
||||
padding = mkLiteral "12 16";
|
||||
spacing = 0;
|
||||
text-color = mkLiteral "@common-foreground";
|
||||
children = mkLiteral "[ entry, case-indicator, num-filtered-rows, textbox-num-sep, num-rows ]";
|
||||
};
|
||||
|
||||
"prompt" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
text-color = mkLiteral "@common-foreground-bright";
|
||||
spacing = 0;
|
||||
text-transform = mkLiteral "bold";
|
||||
};
|
||||
|
||||
"textbox-prompt-colon" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
text-color = mkLiteral "inherit";
|
||||
margin = mkLiteral "0 0.3em 0 0";
|
||||
expand = false;
|
||||
str = "=";
|
||||
};
|
||||
|
||||
"entry" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
text-color = mkLiteral "@common-foreground-bright";
|
||||
cursor = "text";
|
||||
placeholder-color = mkLiteral "@common-foreground-66";
|
||||
placeholder = "Type to filter";
|
||||
};
|
||||
|
||||
"case-indicator" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
text-color = mkLiteral "inherit";
|
||||
};
|
||||
|
||||
"num-filtered-rows" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
text-color = mkLiteral "inherit";
|
||||
expand = false;
|
||||
};
|
||||
|
||||
"textbox-num-sep" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
text-color = mkLiteral "inherit";
|
||||
expand = false;
|
||||
str = "/";
|
||||
};
|
||||
|
||||
"num-rows" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
text-color = mkLiteral "inherit";
|
||||
expand = false;
|
||||
};
|
||||
|
||||
"message" = {
|
||||
background-color = mkLiteral "@cyan-33";
|
||||
border = 1;
|
||||
border-color = mkLiteral "@cyan-66";
|
||||
border-radius = 8;
|
||||
padding = 16;
|
||||
};
|
||||
|
||||
"textbox" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
text-color = mkLiteral "@cyan-bright";
|
||||
};
|
||||
|
||||
"listview" = {
|
||||
dynamic = true;
|
||||
scrollbar = true;
|
||||
spacing = 0;
|
||||
};
|
||||
|
||||
"scrollbar" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
padding = 0;
|
||||
margin = mkLiteral "0 0 0 4";
|
||||
handle-width = 8;
|
||||
border = 0;
|
||||
handle-color = mkLiteral "#626463"; #// @white-50
|
||||
};
|
||||
|
||||
"element" = {
|
||||
border = 1;
|
||||
border-radius = 8;
|
||||
padding = mkLiteral "6 12";
|
||||
margin = mkLiteral "1 0";
|
||||
spacing = 12;
|
||||
children = mkLiteral "[ element-icon, element-text ]";
|
||||
};
|
||||
|
||||
"element-icon" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
text-color = mkLiteral "inherit";
|
||||
size = mkLiteral "1.0em";
|
||||
cursor = mkLiteral "inherit";
|
||||
};
|
||||
|
||||
"element-text" = {
|
||||
background-color = mkLiteral "transparent";
|
||||
text-color = mkLiteral "inherit";
|
||||
highlight = mkLiteral "inherit";
|
||||
cursor = mkLiteral "inherit";
|
||||
};
|
||||
|
||||
"element normal.normal" = {
|
||||
background-color = mkLiteral "@normal-normal-background";
|
||||
text-color = mkLiteral "@normal-normal-foreground";
|
||||
border-color = mkLiteral "@normal-normal-border-color";
|
||||
};
|
||||
|
||||
"element normal.urgent" = {
|
||||
background-color = mkLiteral "@normal-urgent-background";
|
||||
text-color = mkLiteral "@normal-urgent-foreground";
|
||||
border-color = mkLiteral "@normal-urgent-border-color";
|
||||
};
|
||||
|
||||
"element normal.active" = {
|
||||
background-color = mkLiteral "@normal-active-background";
|
||||
text-color = mkLiteral "@normal-active-foreground";
|
||||
border-color = mkLiteral "@normal-active-border-color";
|
||||
};
|
||||
|
||||
"element selected.normal" = {
|
||||
background-color = mkLiteral "@selected-normal-background";
|
||||
text-color = mkLiteral "@selected-normal-foreground";
|
||||
border-color = mkLiteral "@selected-normal-border-color";
|
||||
};
|
||||
|
||||
"element selected.urgent" = {
|
||||
background-color = mkLiteral "@selected-urgent-background";
|
||||
text-color = mkLiteral "@selected-urgent-foreground";
|
||||
border-color = mkLiteral "@selected-urgent-border-color";
|
||||
};
|
||||
|
||||
"element selected.active" = {
|
||||
background-color = mkLiteral "@selected-active-background";
|
||||
text-color = mkLiteral "@selected-active-foreground";
|
||||
border-color = mkLiteral "@selected-active-border-color";
|
||||
};
|
||||
|
||||
"element alternate.normal" = {
|
||||
background-color = mkLiteral "@alternate-normal-background";
|
||||
text-color = mkLiteral "@alternate-normal-foreground";
|
||||
border-color = mkLiteral "@alternate-normal-border-color";
|
||||
};
|
||||
|
||||
"element alternate.urgent" = {
|
||||
background-color = mkLiteral "@alternate-urgent-background";
|
||||
text-color = mkLiteral "@alternate-urgent-foreground";
|
||||
border-color = mkLiteral "@alternate-urgent-border-color";
|
||||
};
|
||||
|
||||
"element alternate.active" = {
|
||||
background-color = mkLiteral "@alternate-active-background";
|
||||
text-color = mkLiteral "@alternate-active-foreground";
|
||||
border-color = mkLiteral "@alternate-active-border-color";
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
338
modules/home/desktop/waybar/default.nix
Normal file
@@ -0,0 +1,338 @@
|
||||
{...}: {
|
||||
programs = {
|
||||
waybar = {
|
||||
enable = true;
|
||||
settings = {
|
||||
mainBar = {
|
||||
position = "top";
|
||||
layer = "top";
|
||||
height = 35;
|
||||
margin-top = 0;
|
||||
margin-bottom = 0;
|
||||
margin-left = 0;
|
||||
margin-right = 0;
|
||||
exclusive = true;
|
||||
passthrough = false;
|
||||
|
||||
modules-left = [
|
||||
"custom/l_end"
|
||||
"cpu"
|
||||
"memory"
|
||||
"custom/r_end"
|
||||
];
|
||||
modules-center = [
|
||||
"custom/l_end"
|
||||
"hyprland/workspaces"
|
||||
"custom/r_end"
|
||||
];
|
||||
modules-right = [
|
||||
"custom/l_end"
|
||||
"network"
|
||||
"bluetooth"
|
||||
"battery"
|
||||
"tray"
|
||||
"custom/r_end"
|
||||
];
|
||||
|
||||
"hyprland/workspaces" = {
|
||||
"disable-scroll" = true;
|
||||
"all-outputs" = true;
|
||||
"active-only" = false;
|
||||
"on-click" = "activate";
|
||||
"persistent-workspaces" = {
|
||||
"1" = [];
|
||||
"2" = [];
|
||||
"3" = [];
|
||||
"4" = [];
|
||||
};
|
||||
};
|
||||
|
||||
"network" = {
|
||||
"tooltip" = true;
|
||||
"format-wifi" = " <span foreground='#99ffdd'> {bandwidthDownBytes}</span> <span foreground='#ffcc66'> {bandwidthUpBytes}</span>";
|
||||
"format-ethernet" = " <span foreground='#99ffdd'> {bandwidthDownBytes}</span> <span foreground='#ffcc66'> {bandwidthUpBytes}</span>";
|
||||
"tooltip-format" = "Network= <big><b>{essid}</b></big>\nSignal strength= <b>{signaldBm}dBm ({signalStrength}%)</b>\nFrequency= <b>{frequency}MHz</b>\nInterface= <b>{ifname}</b>\nIP= <b>{ipaddr}/{cidr}</b>\nGateway= <b>{gwaddr}</b>\nNetmask= <b>{netmask}</b>";
|
||||
"format-linked" = " {ifname} (No IP)";
|
||||
"format-disconnected" = " ";
|
||||
"tooltip-format-disconnected" = "Disconnected";
|
||||
"interval" = 2;
|
||||
};
|
||||
|
||||
"battery" = {
|
||||
"states" = {
|
||||
"good" = 95;
|
||||
"warning" = 30;
|
||||
"critical" = 20;
|
||||
};
|
||||
"format" = "{icon} {capacity}%";
|
||||
"format-charging" = " {capacity}%";
|
||||
"format-plugged" = " {capacity}%";
|
||||
"format-alt" = "{time} {icon}";
|
||||
"format-icons" = ["" "" "" "" "" "" "" "" "" "" ""];
|
||||
};
|
||||
|
||||
"bluetooth" = {
|
||||
"format" = "";
|
||||
"format-disabled" = "";
|
||||
"format-connected" = " {num_connections}";
|
||||
"format-connected-battery" = "{icon} {num_connections}";
|
||||
# "format-connected-battery"= "{icon} {device_alias}-{device_battery_percentage}%";
|
||||
"format-icons" = ["" "" "" "" "" "" "" "" "" "" ""];
|
||||
# "format-device-preference"= [ "device1"; "device2" ]; // preference list deciding the displayed device If this config option is not defined or none of the devices in the list are connected; it will fall back to showing the last connected device.
|
||||
"tooltip-format" = "{controller_alias}\n{num_connections} connected";
|
||||
"tooltip-format-connected" = "{controller_alias}\n{num_connections} connected\n\n{device_enumerate}";
|
||||
"tooltip-format-enumerate-connected" = "{device_alias}";
|
||||
"tooltip-format-enumerate-connected-battery" = "{device_alias}\t{icon} {device_battery_percentage}%";
|
||||
};
|
||||
|
||||
"memory" = {
|
||||
"states" = {
|
||||
"c" = 90; # critical
|
||||
"h" = 60; # high
|
||||
"m" = 30; # medium
|
||||
};
|
||||
"interval" = 30;
|
||||
"format" = " {used}GB";
|
||||
"format-m" = " {used}GB";
|
||||
"format-h" = " {used}GB";
|
||||
"format-c" = " {used}GB";
|
||||
"format-alt" = " {percentage}%";
|
||||
"max-length" = 10;
|
||||
"tooltip" = true;
|
||||
"tooltip-format" = " {percentage}%\n {used=0.1f}GB/{total=0.1f}GB";
|
||||
};
|
||||
|
||||
"cpu" = {
|
||||
"interval" = 10;
|
||||
"format" = " {usage}%";
|
||||
"format-alt" = "{icon0}{icon1}{icon2}{icon3}";
|
||||
"format-icons" = ["▁" "▂" "▃" "▄" "▅" "▆" "▇" "█"];
|
||||
};
|
||||
|
||||
"tray" = {
|
||||
"icon-size" = 14;
|
||||
"spacing" = 5;
|
||||
};
|
||||
|
||||
"custom/l_end" = {
|
||||
"format" = " ";
|
||||
"interval" = "once";
|
||||
"tooltip" = false;
|
||||
};
|
||||
|
||||
"custom/r_end" = {
|
||||
"format" = " ";
|
||||
"interval" = "once";
|
||||
"tooltip" = false;
|
||||
};
|
||||
|
||||
"custom/sl_end" = {
|
||||
"format" = " ";
|
||||
"interval" = "once";
|
||||
"tooltip" = false;
|
||||
};
|
||||
|
||||
"custom/sr_end" = {
|
||||
"format" = " ";
|
||||
"interval" = "once";
|
||||
"tooltip" = false;
|
||||
};
|
||||
|
||||
"custom/rl_end" = {
|
||||
"format" = " ";
|
||||
"interval" = "once";
|
||||
"tooltip" = false;
|
||||
};
|
||||
|
||||
"custom/rr_end" = {
|
||||
"format" = " ";
|
||||
"interval" = "once";
|
||||
"tooltip" = false;
|
||||
};
|
||||
|
||||
"custom/padd" = {
|
||||
"format" = " ";
|
||||
"interval" = "once";
|
||||
"tooltip" = false;
|
||||
};
|
||||
};
|
||||
};
|
||||
style = let
|
||||
bar_bg = "rgba(23, 28, 34, 0.95)";
|
||||
main_bg = "#101419";
|
||||
main_fg = "#93cee9";
|
||||
|
||||
wb_act_bg = "#90ceaa";
|
||||
wb_act_fg = "#1f2328";
|
||||
|
||||
wb_hvr_bg = "#90ceaa";
|
||||
wb_hvr_fg = "#1f2328";
|
||||
in ''
|
||||
* {
|
||||
border: none;
|
||||
border-radius: 0px;
|
||||
font-family: "JetBrainsMono Nerd Font";
|
||||
font-weight: bold;
|
||||
font-size: 20px;
|
||||
min-height: 10px;
|
||||
}
|
||||
|
||||
window#waybar {
|
||||
background: ${bar_bg};
|
||||
}
|
||||
|
||||
tooltip {
|
||||
background: ${main_bg};
|
||||
color: ${main_fg};
|
||||
border-radius: 7px;
|
||||
border-width: 0px;
|
||||
}
|
||||
|
||||
#workspaces button {
|
||||
box-shadow: none;
|
||||
text-shadow: none;
|
||||
padding: 0px;
|
||||
border-radius: 9px;
|
||||
margin-top: 3px;
|
||||
margin-bottom: 3px;
|
||||
margin-left: 0px;
|
||||
padding-left: 3px;
|
||||
padding-right: 3px;
|
||||
margin-right: 0px;
|
||||
color: ${main_fg};
|
||||
animation: ws_normal 20s ease-in-out 1;
|
||||
}
|
||||
|
||||
#workspaces button.active {
|
||||
background: ${wb_act_bg};
|
||||
color: ${wb_act_fg};
|
||||
margin-left: 3px;
|
||||
padding-left: 12px;
|
||||
padding-right: 12px;
|
||||
margin-right: 3px;
|
||||
animation: ws_active 20s ease-in-out 1;
|
||||
transition: all 0.4s cubic-bezier(.55,-0.68,.48,1.682);
|
||||
}
|
||||
|
||||
#workspaces button:hover {
|
||||
background: ${wb_hvr_bg};
|
||||
color: ${wb_hvr_fg};
|
||||
animation: ws_hover 20s ease-in-out 1;
|
||||
transition: all 0.3s cubic-bezier(.55,-0.68,.48,1.682);
|
||||
}
|
||||
|
||||
#taskbar button {
|
||||
box-shadow: none;
|
||||
text-shadow: none;
|
||||
padding: 0px;
|
||||
border-radius: 9px;
|
||||
margin-top: 3px;
|
||||
margin-bottom: 3px;
|
||||
margin-left: 0px;
|
||||
padding-left: 3px;
|
||||
padding-right: 3px;
|
||||
margin-right: 0px;
|
||||
color: @wb-color;
|
||||
animation: tb_normal 20s ease-in-out 1;
|
||||
}
|
||||
|
||||
#taskbar button.active {
|
||||
background: ${wb_act_bg};
|
||||
color: @wb-act-color;
|
||||
margin-left: 3px;
|
||||
padding-left: 12px;
|
||||
padding-right: 12px;
|
||||
margin-right: 3px;
|
||||
animation: tb_active 20s ease-in-out 1;
|
||||
transition: all 0.4s cubic-bezier(.55,-0.68,.48,1.682);
|
||||
}
|
||||
|
||||
#taskbar button:hover {
|
||||
background: ${wb_hvr_bg};
|
||||
color: @wb-hvr-color;
|
||||
animation: tb_hover 20s ease-in-out 1;
|
||||
transition: all 0.3s cubic-bezier(.55,-0.68,.48,1.682);
|
||||
}
|
||||
|
||||
#backlight,
|
||||
#battery,
|
||||
#bluetooth,
|
||||
#custom-cliphist,
|
||||
#clock,
|
||||
#custom-cpuinfo,
|
||||
#cpu,
|
||||
#custom-gpuinfo,
|
||||
#idle_inhibitor,
|
||||
#language,
|
||||
#memory,
|
||||
#custom-mode,
|
||||
#mpris,
|
||||
#network,
|
||||
#custom-power,
|
||||
#pulseaudio,
|
||||
#custom-spotify,
|
||||
#taskbar,
|
||||
#tray,
|
||||
#custom-updates,
|
||||
#custom-wallchange,
|
||||
#custom-wbar,
|
||||
#window,
|
||||
#workspaces,
|
||||
#custom-l_end,
|
||||
#custom-r_end,
|
||||
#custom-sl_end,
|
||||
#custom-sr_end,
|
||||
#custom-rl_end,
|
||||
#custom-rr_end {
|
||||
color: ${main_fg};
|
||||
background: ${main_bg};
|
||||
opacity: 1;
|
||||
margin: 4px 0px 4px 0px;
|
||||
padding-left: 4px;
|
||||
padding-right: 4px;
|
||||
}
|
||||
|
||||
#workspaces,
|
||||
#taskbar {
|
||||
padding: 0px;
|
||||
}
|
||||
|
||||
#custom-r_end {
|
||||
border-radius: 0px 21px 21px 0px;
|
||||
margin-right: 9px;
|
||||
padding-right: 3px;
|
||||
}
|
||||
|
||||
#custom-l_end {
|
||||
border-radius: 21px 0px 0px 21px;
|
||||
margin-left: 9px;
|
||||
padding-left: 3px;
|
||||
}
|
||||
|
||||
#custom-sr_end {
|
||||
border-radius: 0px;
|
||||
margin-right: 9px;
|
||||
padding-right: 3px;
|
||||
}
|
||||
|
||||
#custom-sl_end {
|
||||
border-radius: 0px;
|
||||
margin-left: 9px;
|
||||
padding-left: 3px;
|
||||
}
|
||||
|
||||
#custom-rr_end {
|
||||
border-radius: 0px 7px 7px 0px;
|
||||
margin-right: 9px;
|
||||
padding-right: 3px;
|
||||
}
|
||||
|
||||
#custom-rl_end {
|
||||
border-radius: 7px 0px 0px 7px;
|
||||
margin-left: 9px;
|
||||
padding-left: 3px;
|
||||
}
|
||||
'';
|
||||
};
|
||||
};
|
||||
}
|
||||
40
modules/home/discord/default.nix
Normal file
@@ -0,0 +1,40 @@
|
||||
{inputs, ...}: {
|
||||
imports = [
|
||||
inputs.nixcord.homeModules.nixcord
|
||||
];
|
||||
|
||||
programs.nixcord = {
|
||||
enable = true;
|
||||
vesktop.enable = true;
|
||||
dorion.enable = true;
|
||||
config = {
|
||||
themeLinks = [
|
||||
"https://raw.githubusercontent.com/refact0r/system24/refs/heads/main/archive/flavors/spotify-text.theme.css"
|
||||
];
|
||||
frameless = true;
|
||||
plugins = {
|
||||
hideAttachments.enable = true;
|
||||
ignoreActivities = {
|
||||
enable = true;
|
||||
ignorePlaying = true;
|
||||
ignoreWatching = true;
|
||||
};
|
||||
};
|
||||
};
|
||||
dorion = {
|
||||
theme = "dark";
|
||||
zoom = "1.1";
|
||||
blur = "acrylic";
|
||||
sysTray = true;
|
||||
openOnStartup = true;
|
||||
autoClearCache = true;
|
||||
disableHardwareAccel = false;
|
||||
rpcServer = true;
|
||||
rpcProcessScanner = true;
|
||||
pushToTalk = true;
|
||||
pushToTalkKeys = ["RControl"];
|
||||
desktopNotifications = true;
|
||||
unreadBadge = true;
|
||||
};
|
||||
};
|
||||
}
|
||||
3
modules/home/easyeffects/default.nix
Normal file
@@ -0,0 +1,3 @@
|
||||
{...}: {
|
||||
services.easyeffects.enable = true;
|
||||
}
|
||||
73
modules/home/fastfetch/default.nix
Normal file
@@ -0,0 +1,73 @@
|
||||
{...}: {
|
||||
home.file.".config/fastfetch/config.jsonc".text = ''
|
||||
{
|
||||
"$schema": "https://github.com/fastfetch-cli/fastfetch/raw/dev/doc/json_schema.json",
|
||||
"logo": {
|
||||
"type": "none",
|
||||
},
|
||||
"display": {
|
||||
"separator": " ",
|
||||
"key": {
|
||||
"width": 18,
|
||||
},
|
||||
},
|
||||
"modules": [
|
||||
{
|
||||
"key": " ╭───────────╮",
|
||||
"type": "custom",
|
||||
},
|
||||
{
|
||||
"key": " │ │\u001b[11D{#31} user",
|
||||
"type": "title",
|
||||
"format": "{1}",
|
||||
},
|
||||
{
|
||||
"key": " │ │\u001b[11D{#34} hname",
|
||||
"type": "command",
|
||||
"text": "hostname",
|
||||
},
|
||||
{
|
||||
"key": " │ │\u001b[11D{#34} distro",
|
||||
"type": "os",
|
||||
},
|
||||
{
|
||||
"key": " │ │\u001b[11D{#35} kernel",
|
||||
"type": "kernel",
|
||||
},
|
||||
{
|
||||
"key": " │ │\u001b[11D{#31} uptime",
|
||||
"type": "uptime",
|
||||
},
|
||||
{
|
||||
"key": " │ │\u001b[11D{#32} shell",
|
||||
"type": "shell",
|
||||
},
|
||||
{
|
||||
"key": " │ │\u001b[11D{#35} pkgs",
|
||||
"type": "packages",
|
||||
},
|
||||
{
|
||||
"key": " │ │\u001b[11D{#35} memory",
|
||||
"type": "memory",
|
||||
},
|
||||
{
|
||||
"key": " ├───────────┤",
|
||||
"type": "custom",
|
||||
},
|
||||
{
|
||||
"key": " │ │\u001b[11D{#39} colors",
|
||||
"type": "colors",
|
||||
"symbol": "circle",
|
||||
},
|
||||
{
|
||||
"key": " ╰───────────╯",
|
||||
"type": "custom",
|
||||
},
|
||||
],
|
||||
}
|
||||
'';
|
||||
|
||||
programs.fastfetch = {
|
||||
enable = true;
|
||||
};
|
||||
}
|
||||
73
modules/home/firefox/default.nix
Normal file
@@ -0,0 +1,73 @@
|
||||
{
|
||||
pkgs,
|
||||
username,
|
||||
...
|
||||
}: {
|
||||
home.file.".mozilla/firefox/${username}/chrome".source = pkgs.firefox-mod-blur;
|
||||
|
||||
programs.firefox = {
|
||||
enable = true;
|
||||
|
||||
package = pkgs.firefox.override {
|
||||
extraPolicies = {
|
||||
CaptivePortal = false;
|
||||
DisableFirefoxStudies = true;
|
||||
DisablePocket = true;
|
||||
DisableTelemetry = true;
|
||||
DisableFirefoxAccounts = false;
|
||||
NoDefaultBookmarks = true;
|
||||
OfferToSaveLogins = false;
|
||||
OfferToSaveLoginsDefault = false;
|
||||
PasswordManagerEnabled = false;
|
||||
FirefoxHome = {
|
||||
Search = true;
|
||||
Pocket = false;
|
||||
Snippets = false;
|
||||
TopSites = false;
|
||||
Highlights = false;
|
||||
};
|
||||
UserMessaging = {
|
||||
ExtensionRecommendations = false;
|
||||
SkipOnboarding = true;
|
||||
};
|
||||
};
|
||||
};
|
||||
|
||||
profiles = {
|
||||
${username} = {
|
||||
id = 0;
|
||||
name = "tux";
|
||||
search = {
|
||||
force = true;
|
||||
default = "google";
|
||||
};
|
||||
settings = {
|
||||
"general.smoothScroll" = true;
|
||||
"extensions.activeThemeID" = "firefox-compact-dark@mozilla.org";
|
||||
"layout.css.prefers-color-scheme.content-override" = 0;
|
||||
"browser.compactmode.show" = true;
|
||||
"browser.tabs.firefox-view" = false;
|
||||
"browser.bookmarks.addedImportButton" = false;
|
||||
"extensions.pocket.enabled" = false;
|
||||
"browser.fullscreen.autohide" = false;
|
||||
};
|
||||
extraConfig = ''
|
||||
user_pref("toolkit.legacyUserProfileCustomizations.stylesheets", true);
|
||||
user_pref("full-screen-api.ignore-widgets", true);
|
||||
user_pref("media.ffmpeg.vaapi.enabled", true);
|
||||
user_pref("media.rdd-vpx.enabled", true);
|
||||
'';
|
||||
|
||||
extensions.packages = with pkgs.nur.repos.rycee.firefox-addons; [
|
||||
ublock-origin
|
||||
facebook-container
|
||||
metamask
|
||||
darkreader
|
||||
bitwarden
|
||||
wappalyzer
|
||||
clearurls
|
||||
];
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
46
modules/home/floorp/default.nix
Normal file
@@ -0,0 +1,46 @@
|
||||
{
|
||||
username,
|
||||
pkgs,
|
||||
...
|
||||
}: {
|
||||
programs.floorp = {
|
||||
enable = true;
|
||||
|
||||
profiles = {
|
||||
${username} = {
|
||||
id = 0;
|
||||
name = "${username}";
|
||||
search = {
|
||||
force = true;
|
||||
default = "Google";
|
||||
};
|
||||
settings = {
|
||||
"general.smoothScroll" = true;
|
||||
"extensions.activeThemeID" = "firefox-compact-dark@mozilla.org";
|
||||
"layout.css.prefers-color-scheme.content-override" = 0;
|
||||
"browser.compactmode.show" = true;
|
||||
"browser.tabs.firefox-view" = false;
|
||||
"browser.bookmarks.addedImportButton" = false;
|
||||
"extensions.pocket.enabled" = false;
|
||||
"browser.fullscreen.autohide" = false;
|
||||
};
|
||||
extraConfig = ''
|
||||
user_pref("toolkit.legacyUserProfileCustomizations.stylesheets", true);
|
||||
user_pref("full-screen-api.ignore-widgets", true);
|
||||
user_pref("media.ffmpeg.vaapi.enabled", true);
|
||||
user_pref("media.rdd-vpx.enabled", true);
|
||||
'';
|
||||
|
||||
extensions.packages = with pkgs.nur.repos.rycee.firefox-addons; [
|
||||
ublock-origin
|
||||
facebook-container
|
||||
metamask
|
||||
darkreader
|
||||
bitwarden
|
||||
wappalyzer
|
||||
clearurls
|
||||
];
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
40
modules/home/ghostty/default.nix
Normal file
@@ -0,0 +1,40 @@
|
||||
{pkgs, ...}: {
|
||||
home.file = {
|
||||
".config/ghostty/config" = {
|
||||
text = ''
|
||||
confirm-close-surface = false
|
||||
gtk-titlebar = false
|
||||
window-padding-x = 10
|
||||
window-padding-y = 10
|
||||
background-opacity = 0.9
|
||||
font-size = 14
|
||||
|
||||
palette = 0=#252b37
|
||||
palette = 1=#d0679d
|
||||
palette = 2=#5de4c7
|
||||
palette = 3=#fffac2
|
||||
palette = 4=#89ddff
|
||||
palette = 5=#fae4fc
|
||||
palette = 6=#add7ff
|
||||
palette = 7=#ffffff
|
||||
palette = 8=#a6accd
|
||||
palette = 9=#d0679d
|
||||
palette = 10=#5de4c7
|
||||
palette = 11=#fffac2
|
||||
palette = 12=#add7ff
|
||||
palette = 13=#89ddff
|
||||
palette = 14=#fcc5e9
|
||||
palette = 15=#ffffff
|
||||
background = #0f0f0f
|
||||
foreground = #a6accd
|
||||
cursor-color = #f2eacf
|
||||
selection-background = #1a1a1a
|
||||
selection-foreground = #f1f1f1
|
||||
'';
|
||||
};
|
||||
};
|
||||
|
||||
home.packages = with pkgs; [
|
||||
ghostty
|
||||
];
|
||||
}
|
||||
20
modules/home/git/default.nix
Executable file
@@ -0,0 +1,20 @@
|
||||
{
|
||||
email,
|
||||
username,
|
||||
...
|
||||
}: {
|
||||
programs.git = {
|
||||
enable = true;
|
||||
userName = "${username}";
|
||||
userEmail = "${email}";
|
||||
signing = {
|
||||
key = "~/.ssh/id_ed25519.pub";
|
||||
signByDefault = true;
|
||||
};
|
||||
extraConfig = {
|
||||
init.defaultBranch = "main";
|
||||
commit.gpgSign = true;
|
||||
gpg.format = "ssh";
|
||||
};
|
||||
};
|
||||
}
|
||||
37
modules/home/helix/default.nix
Normal file
@@ -0,0 +1,37 @@
|
||||
{pkgs, ...}: {
|
||||
programs.helix = {
|
||||
enable = true;
|
||||
settings = {
|
||||
theme = "gruvbox";
|
||||
editor = {
|
||||
line-number = "relative";
|
||||
cursorline = true;
|
||||
color-modes = true;
|
||||
bufferline = "multiple";
|
||||
|
||||
"cursor-shape" = {
|
||||
insert = "bar";
|
||||
normal = "block";
|
||||
select = "underline";
|
||||
};
|
||||
};
|
||||
};
|
||||
languages = {
|
||||
language = [
|
||||
{
|
||||
name = "nix";
|
||||
auto-format = true;
|
||||
}
|
||||
];
|
||||
|
||||
language-server = {
|
||||
nil = {
|
||||
command = "${pkgs.nil}/bin/nil";
|
||||
config.nil.formatting = {
|
||||
command = "${pkgs.alejandra}/bin/alejandra";
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
6
modules/home/kdeconnect/default.nix
Normal file
@@ -0,0 +1,6 @@
|
||||
{...}: {
|
||||
services.kdeconnect = {
|
||||
enable = true;
|
||||
indicator = true;
|
||||
};
|
||||
}
|
||||
5
modules/home/librewolf/default.nix
Normal file
@@ -0,0 +1,5 @@
|
||||
{...}: {
|
||||
programs.librewolf = {
|
||||
enable = true;
|
||||
};
|
||||
}
|
||||
39
modules/home/mopidy/default.nix
Normal file
@@ -0,0 +1,39 @@
|
||||
{pkgs, ...}: {
|
||||
programs.ncmpcpp = {
|
||||
enable = true;
|
||||
package = pkgs.ncmpcpp.override {
|
||||
visualizerSupport = true;
|
||||
clockSupport = true;
|
||||
};
|
||||
mpdMusicDir = "~/Music/";
|
||||
|
||||
settings = {
|
||||
mpd_host = "127.0.0.1";
|
||||
mpd_port = 6600;
|
||||
mpd_connection_timeout = 20;
|
||||
visualizer_data_source = "localhost:5555";
|
||||
visualizer_fps = 60;
|
||||
visualizer_output_name = "feed";
|
||||
visualizer_in_stereo = "yes";
|
||||
visualizer_type = "spectrum";
|
||||
visualizer_look = "▄▍";
|
||||
visualizer_spectrum_smooth_look = "yes";
|
||||
visualizer_sync_interval = 0;
|
||||
song_status_format = "$b$7♫ $2%a $4⟫$3⟫ $8%t $4⟫$3⟫ $5%b ";
|
||||
header_visibility = "no";
|
||||
color1 = "white";
|
||||
color2 = "green";
|
||||
};
|
||||
};
|
||||
|
||||
services.mopidy = {
|
||||
enable = true;
|
||||
|
||||
extensionPackages = with pkgs; [
|
||||
mopidy-mpd
|
||||
mopidy-spotify
|
||||
mopidy-soundcloud
|
||||
mopidy-iris
|
||||
];
|
||||
};
|
||||
}
|
||||
40
modules/home/nvim/default.nix
Executable file
@@ -0,0 +1,40 @@
|
||||
{pkgs, ...}: {
|
||||
home.file = {
|
||||
".config/nvim" = {
|
||||
recursive = true;
|
||||
source = "${pkgs.tnvim}";
|
||||
};
|
||||
};
|
||||
|
||||
programs = {
|
||||
neovim = {
|
||||
enable = true;
|
||||
defaultEditor = true;
|
||||
vimAlias = true;
|
||||
withPython3 = true;
|
||||
withNodeJs = true;
|
||||
};
|
||||
};
|
||||
|
||||
home = {
|
||||
packages = with pkgs; [
|
||||
gcc
|
||||
neovide
|
||||
|
||||
# nix
|
||||
nil # Language Server
|
||||
statix # Lints and suggestions
|
||||
deadnix # Find and remove unused
|
||||
alejandra # Code Formatter
|
||||
|
||||
# lua
|
||||
luarocks
|
||||
|
||||
# ts
|
||||
typescript
|
||||
|
||||
gdu
|
||||
ripgrep
|
||||
];
|
||||
};
|
||||
}
|
||||
6
modules/home/obs-studio/default.nix
Normal file
@@ -0,0 +1,6 @@
|
||||
{pkgs, ...}: {
|
||||
programs.obs-studio = {
|
||||
enable = true;
|
||||
plugins = with pkgs.obs-studio-plugins; [obs-vaapi];
|
||||
};
|
||||
}
|
||||
64
modules/home/picom/default.nix
Normal file
@@ -0,0 +1,64 @@
|
||||
{pkgs, ...}: {
|
||||
services.picom = {
|
||||
enable = true;
|
||||
package = pkgs.picom-next;
|
||||
|
||||
backend = "glx";
|
||||
vSync = true;
|
||||
|
||||
fade = true;
|
||||
fadeDelta = 10;
|
||||
fadeSteps = [0.05 0.05];
|
||||
fadeExclude = [
|
||||
"window_type *= 'menu'"
|
||||
];
|
||||
|
||||
activeOpacity = 1;
|
||||
inactiveOpacity = 1;
|
||||
opacityRules = [
|
||||
"90:class_g = 'rofi'"
|
||||
"90:class_g = 'thunar'"
|
||||
"90:class_g = 'spotify'"
|
||||
"90:class_g = 'discord'"
|
||||
"90:class_g = 'code'"
|
||||
"90:class_g = 'org.wezfurlong.wezterm'"
|
||||
"90:class_g = 'wezterm-floating'"
|
||||
];
|
||||
|
||||
settings = {
|
||||
glx-no-stencil = true;
|
||||
glx-copy-from-font = false;
|
||||
use-damage = false;
|
||||
|
||||
frame-opacity = 1;
|
||||
blur-background = true;
|
||||
blur-method = "dual_kawase";
|
||||
blur-strength = 10;
|
||||
|
||||
corner-radius = 8;
|
||||
|
||||
rounded-corners-exclude = [
|
||||
"window_type = 'dock'"
|
||||
];
|
||||
|
||||
# pijulius specifics
|
||||
animations = true;
|
||||
animation-stiffness = 500;
|
||||
animation-window-mass = 1.0;
|
||||
animation-dampening = 26;
|
||||
animation-delta = 10;
|
||||
animation-force_steps = false;
|
||||
animation-clamping = true;
|
||||
|
||||
animation-for-open-window = "slide-up";
|
||||
animation-for-menu-window = "slide-down";
|
||||
animation-for-transient-window = "slide-down";
|
||||
animation-for-unmap-window = "slide-up";
|
||||
|
||||
animation-for-next-tag = "slide-right";
|
||||
animation-for-prev-tag = "slide-left";
|
||||
enable-fading-next-tag = true;
|
||||
enable-fading-prev-tag = true;
|
||||
};
|
||||
};
|
||||
}
|
||||
15
modules/home/shell/aichat.nix
Normal file
@@ -0,0 +1,15 @@
|
||||
{...}: {
|
||||
programs = {
|
||||
aichat = {
|
||||
enable = true;
|
||||
settings = {
|
||||
model = "gemini:gemini-2.0-flash-lite";
|
||||
clients = [
|
||||
{
|
||||
type = "gemini";
|
||||
}
|
||||
];
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
98
modules/home/shell/default.nix
Executable file
@@ -0,0 +1,98 @@
|
||||
{pkgs, ...}: {
|
||||
imports = [
|
||||
./lazygit.nix
|
||||
./aichat.nix
|
||||
];
|
||||
|
||||
programs = {
|
||||
bat.enable = true;
|
||||
zsh = {
|
||||
enable = true;
|
||||
history = {
|
||||
append = true;
|
||||
share = true;
|
||||
expireDuplicatesFirst = true;
|
||||
ignoreDups = true;
|
||||
size = 1000000;
|
||||
save = 1000000;
|
||||
path = "$HOME/.local/share/zsh/.zsh_history";
|
||||
};
|
||||
syntaxHighlighting.enable = true;
|
||||
autosuggestion.enable = true;
|
||||
initContent = ''
|
||||
fastfetch
|
||||
export WINIT_X11_SCALE_FACTOR=1
|
||||
PATH=$PATH:~/.cargo/bin:~/.local/bin
|
||||
|
||||
bindkey "^A" vi-beginning-of-line
|
||||
bindkey "^E" vi-end-of-line
|
||||
bindkey '^R' fzf-history-widget
|
||||
'';
|
||||
};
|
||||
zoxide = {
|
||||
enable = true;
|
||||
options = ["--cmd cd"];
|
||||
enableZshIntegration = true;
|
||||
};
|
||||
ripgrep.enable = true;
|
||||
btop = {
|
||||
enable = true;
|
||||
settings = {
|
||||
theme_background = false;
|
||||
update_ms = 1000;
|
||||
presets = "cpu:0:default mem:0:default net:0:default";
|
||||
};
|
||||
};
|
||||
go.enable = true;
|
||||
yazi = {
|
||||
enable = true;
|
||||
enableZshIntegration = true;
|
||||
};
|
||||
fzf = {
|
||||
enable = true;
|
||||
enableZshIntegration = true;
|
||||
};
|
||||
lsd = {
|
||||
enable = true;
|
||||
enableZshIntegration = true;
|
||||
};
|
||||
};
|
||||
|
||||
home.packages = with pkgs; [
|
||||
systemctl-tui
|
||||
ranger
|
||||
wget
|
||||
portal
|
||||
bore-cli
|
||||
zip
|
||||
unzip
|
||||
pciutils
|
||||
gnumake
|
||||
nvtopPackages.full
|
||||
zellij
|
||||
nix-output-monitor
|
||||
duf
|
||||
jq
|
||||
atac
|
||||
termshark
|
||||
solc
|
||||
dig
|
||||
|
||||
python312
|
||||
python312Packages.pipx
|
||||
nodejs
|
||||
nodePackages.pnpm
|
||||
nodePackages.yarn
|
||||
rustup
|
||||
bun
|
||||
nixpkgs-fmt
|
||||
|
||||
hunspell
|
||||
hunspellDicts.en_US
|
||||
air
|
||||
templ
|
||||
ffmpeg
|
||||
deploy-rs
|
||||
trok
|
||||
];
|
||||
}
|
||||
79
modules/home/shell/lazygit.nix
Normal file
@@ -0,0 +1,79 @@
|
||||
{...}: {
|
||||
programs.lazygit = {
|
||||
enable = true;
|
||||
settings = {
|
||||
gui = {
|
||||
showIcons = true;
|
||||
nerdFontsVersion = "3";
|
||||
};
|
||||
customCommands = [
|
||||
{
|
||||
key = "<c-a>";
|
||||
description = "Pick AI commit";
|
||||
command = ''
|
||||
aichat "Please suggest 10 commit messages, given the following diff:
|
||||
|
||||
\`\`\`diff
|
||||
$(git diff --cached)
|
||||
\`\`\`
|
||||
|
||||
**Criteria:**
|
||||
|
||||
1. **Format:** Each commit message must follow the conventional commits format, which is \`<type>(<scope>): <description>\`.
|
||||
2. **Relevance:** Avoid mentioning a module name unless it's directly relevant to the change.
|
||||
3. **Enumeration:** List the commit messages from 1 to 10.
|
||||
4. **Clarity and Conciseness:** Each message should clearly and concisely convey the change made.
|
||||
|
||||
**Commit Message Examples:**
|
||||
|
||||
- fix(app): add password regex pattern
|
||||
- test(unit): add new test cases
|
||||
- style: remove unused imports
|
||||
- refactor(pages): extract common code to \`utils/wait.ts\`
|
||||
|
||||
**Recent Commits on Repo for Reference:**
|
||||
|
||||
\`\`\`
|
||||
$(git log -n 10 --pretty=format:'%h %s')
|
||||
\`\`\`
|
||||
|
||||
**Output Template**
|
||||
|
||||
Follow this output template and ONLY output raw commit messages without spacing, numbers or other decorations.
|
||||
|
||||
fix(app): add password regex pattern
|
||||
test(unit): add new test cases
|
||||
style: remove unused imports
|
||||
refactor(pages): extract common code to \`utils/wait.ts\`
|
||||
|
||||
|
||||
**Instructions:**
|
||||
|
||||
- Take a moment to understand the changes made in the diff.
|
||||
- Think about the impact of these changes on the project (e.g., bug fixes, new features, performance improvements, code refactoring, documentation updates). It's critical to my career you abstract the changes to a higher level and not just describe the code changes.
|
||||
- Generate commit messages that accurately describe these changes, ensuring they are helpful to someone reading the project's history.
|
||||
- Remember, a well-crafted commit message can significantly aid in the maintenance and understanding of the project over time.
|
||||
- If multiple changes are present, make sure you capture them all in each commit message.
|
||||
|
||||
Keep in mind you will suggest 10 commit messages. Only 1 will be used. It's better to push yourself (esp to synthesize to a higher level) and maybe wrong about some of the 10 commits because only one needs to be good. I'm looking for your best commit, not the best average commit. It's better to cover more scenarios than include a lot of overlap.
|
||||
|
||||
Write your 10 commit messages below in the format shown in Output Template section above." \
|
||||
| fzf --height 40% --border --ansi --preview "echo {}" --preview-window=up:wrap \
|
||||
| xargs -I {} bash -c '
|
||||
COMMIT_MSG_FILE=$(mktemp)
|
||||
echo "{}" > "$COMMIT_MSG_FILE"
|
||||
''${EDITOR:-vim} "$COMMIT_MSG_FILE"
|
||||
if [ -s "$COMMIT_MSG_FILE" ]; then
|
||||
git commit -F "$COMMIT_MSG_FILE"
|
||||
else
|
||||
echo "Commit message is empty, commit aborted."
|
||||
fi
|
||||
rm -f "$COMMIT_MSG_FILE"'
|
||||
'';
|
||||
context = "files";
|
||||
output = "terminal";
|
||||
}
|
||||
];
|
||||
};
|
||||
};
|
||||
}
|
||||
50
modules/home/starship/default.nix
Executable file
@@ -0,0 +1,50 @@
|
||||
{...}: {
|
||||
programs.starship = {
|
||||
enable = true;
|
||||
settings = {
|
||||
format = ''$os$hostname$directory$rust$golang$solidity$nodejs(bold blue)$git_branch$git_status[❯](bold yellow)[❯](bold purple)[❯](bold blue) '';
|
||||
scan_timeout = 60;
|
||||
add_newline = false;
|
||||
line_break.disabled = true;
|
||||
|
||||
os = {
|
||||
format = "[$symbol ]($style)";
|
||||
style = "bold green";
|
||||
disabled = false;
|
||||
symbols.NixOS = "";
|
||||
symbols.Linux = "";
|
||||
symbols.Arch = "";
|
||||
symbols.Ubuntu = "";
|
||||
};
|
||||
directory = {
|
||||
format = "[$path]($style)[$read_only ]($read_only_style)";
|
||||
read_only = " ";
|
||||
style = "bold blue";
|
||||
};
|
||||
git_branch.format = "[$symbol$branch]($style) ";
|
||||
hostname = {
|
||||
ssh_only = false;
|
||||
format = "[$ssh_symbol$hostname]($style) ";
|
||||
style = "bold green";
|
||||
ssh_symbol = " ";
|
||||
disabled = false;
|
||||
};
|
||||
rust = {
|
||||
format = "[$symbol]($style)";
|
||||
symbol = " ";
|
||||
};
|
||||
golang = {
|
||||
format = "[$symbol]($style)";
|
||||
symbol = " ";
|
||||
};
|
||||
solidity = {
|
||||
format = "[$symbol]($style)";
|
||||
symbol = " ";
|
||||
};
|
||||
nodejs = {
|
||||
format = "[$symbol]($style)";
|
||||
symbol = " ";
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
9
modules/home/thunderbird/default.nix
Normal file
@@ -0,0 +1,9 @@
|
||||
{username, ...}: {
|
||||
programs.thunderbird = {
|
||||
enable = true;
|
||||
|
||||
profiles."${username}" = {
|
||||
isDefault = true;
|
||||
};
|
||||
};
|
||||
}
|
||||
136
modules/home/tmux/default.nix
Normal file
@@ -0,0 +1,136 @@
|
||||
{pkgs, ...}: let
|
||||
bg = "default";
|
||||
fg = "default";
|
||||
bg2 = "brightblack";
|
||||
fg2 = "white";
|
||||
color = c: "#{@${c}}";
|
||||
|
||||
indicator = let
|
||||
accent = color "indicator_color";
|
||||
content = " ";
|
||||
in "#[reverse,fg=${accent}]#{?client_prefix,${content},}";
|
||||
|
||||
current_window = let
|
||||
accent = color "main_accent";
|
||||
index = "#[reverse,fg=${accent},bg=${fg}] #I ";
|
||||
name = "#[fg=${bg2},bg=${fg2}] #W ";
|
||||
# flags = "#{?window_flags,#{window_flags}, }";
|
||||
in "${index}${name}";
|
||||
|
||||
window_status = let
|
||||
accent = color "window_color";
|
||||
index = "#[reverse,fg=${accent},bg=${fg}] #I ";
|
||||
name = "#[fg=${bg2},bg=${fg2}] #W ";
|
||||
# flags = "#{?window_flags,#{window_flags}, }";
|
||||
in "${index}${name}";
|
||||
|
||||
battery = let
|
||||
percentage = pkgs.writeShellScript "percentage" (
|
||||
if pkgs.stdenv.isDarwin
|
||||
then ''
|
||||
echo $(pmset -g batt | grep -o "[0-9]\+%" | tr '%' ' ')
|
||||
''
|
||||
else ''
|
||||
path="/org/freedesktop/UPower/devices/DisplayDevice"
|
||||
echo $(${pkgs.upower}/bin/upower -i $path | grep -o "[0-9]\+%" | tr '%' ' ')
|
||||
''
|
||||
);
|
||||
state = pkgs.writeShellScript "state" (
|
||||
if pkgs.stdenv.isDarwin
|
||||
then ''
|
||||
echo $(pmset -g batt | awk '{print $4}')
|
||||
''
|
||||
else ''
|
||||
path="/org/freedesktop/UPower/devices/DisplayDevice"
|
||||
echo $(${pkgs.upower}/bin/upower -i $path | grep state | awk '{print $2}')
|
||||
''
|
||||
);
|
||||
icon = pkgs.writeShellScript "icon" ''
|
||||
percentage=$(${percentage})
|
||||
state=$(${state})
|
||||
if [ "$state" == "charging" ] || [ "$state" == "fully-charged" ]; then echo ""
|
||||
elif [ $percentage -ge 75 ]; then echo ""
|
||||
elif [ $percentage -ge 50 ]; then echo ""
|
||||
elif [ $percentage -ge 25 ]; then echo ""
|
||||
elif [ $percentage -ge 0 ]; then echo ""
|
||||
fi
|
||||
'';
|
||||
color = pkgs.writeShellScript "color" ''
|
||||
percentage=$(${percentage})
|
||||
state=$(${state})
|
||||
if [ "$state" == "charging" ] || [ "$state" == "fully-charged" ]; then echo "green"
|
||||
elif [ $percentage -ge 75 ]; then echo "green"
|
||||
elif [ $percentage -ge 50 ]; then echo "${fg2}"
|
||||
elif [ $percentage -ge 30 ]; then echo "yellow"
|
||||
elif [ $percentage -ge 0 ]; then echo "red"
|
||||
fi
|
||||
'';
|
||||
in "#[fg=#(${color})]#(${icon}) #[fg=${fg}]#(${percentage})%";
|
||||
|
||||
pwd = let
|
||||
accent = color "main_accent";
|
||||
icon = "#[fg=${accent}] ";
|
||||
format = "#[fg=${fg}]#{b:pane_current_path}";
|
||||
in "${icon}${format}";
|
||||
|
||||
git = let
|
||||
icon = pkgs.writeShellScript "branch" ''
|
||||
git -C "$1" branch && echo " "
|
||||
'';
|
||||
branch = pkgs.writeShellScript "branch" ''
|
||||
git -C "$1" rev-parse --abbrev-ref HEAD
|
||||
'';
|
||||
in "#[fg=magenta]#(${icon} #{pane_current_path})#(${branch} #{pane_current_path})";
|
||||
|
||||
separator = "#[fg=${fg}]|";
|
||||
in {
|
||||
programs.tmux = {
|
||||
enable = true;
|
||||
baseIndex = 1;
|
||||
escapeTime = 0;
|
||||
mouse = true;
|
||||
extraConfig = ''
|
||||
set-option -sa terminal-overrides ",xterm*:Tc"
|
||||
set-option -g status-position top
|
||||
unbind r
|
||||
bind r source-file ~/.config/tmux/tmux.conf
|
||||
|
||||
# remap prefix from C-b to C-Space
|
||||
# unbind C-b
|
||||
# set -g prefix C-Space
|
||||
# bind C-Space send-prefix
|
||||
|
||||
# split panes using | and -
|
||||
unbind '"'
|
||||
unbind %
|
||||
bind | split-window -h
|
||||
bind - split-window -v
|
||||
|
||||
# Start windows and panes at 1, not 0
|
||||
set -g base-index 1
|
||||
set -g pane-base-index 1
|
||||
set-window-option -g pane-base-index 1
|
||||
set-option -g renumber-windows on
|
||||
|
||||
# switch panes using Alt-arrow without prefix
|
||||
bind -n M-Left select-pane -L
|
||||
bind -n M-Right select-pane -R
|
||||
bind -n M-Up select-pane -U
|
||||
bind -n M-Down select-pane -D
|
||||
|
||||
set-option -g default-terminal "screen-256color"
|
||||
set-option -g status-right-length 100
|
||||
set-option -g @indicator_color "yellow"
|
||||
set-option -g @window_color "magenta"
|
||||
set-option -g @main_accent "blue"
|
||||
set-option -g pane-active-border fg=black
|
||||
set-option -g pane-border-style fg=black
|
||||
set-option -g status-style "bg=${bg} fg=${fg}"
|
||||
set-option -g status-left "${indicator}"
|
||||
set-option -g status-right "${git} ${pwd} ${separator} ${battery}"
|
||||
set-option -g window-status-current-format "${current_window}"
|
||||
set-option -g window-status-format "${window_status}"
|
||||
set-option -g window-status-separator ""
|
||||
'';
|
||||
};
|
||||
}
|
||||
76
modules/home/vs-code/default.nix
Normal file
@@ -0,0 +1,76 @@
|
||||
{pkgs, ...}: {
|
||||
programs.vscode = {
|
||||
enable = true;
|
||||
package = pkgs.vscodium;
|
||||
|
||||
profiles.default = {
|
||||
keybindings = [
|
||||
{
|
||||
"key" = "f7";
|
||||
"command" = "-editor.action.wordHighlight.next";
|
||||
"when" = "editorTextFocus && hasWordHighlights";
|
||||
}
|
||||
{
|
||||
"key" = "f7";
|
||||
"command" = "-editor.action.accessibleDiffViewer.next";
|
||||
"when" = "isInDiffEditor";
|
||||
}
|
||||
{
|
||||
"key" = "f7";
|
||||
"command" = "workbench.action.terminal.toggleTerminal";
|
||||
"when" = "terminal.active";
|
||||
}
|
||||
{
|
||||
"key" = "ctrl+`";
|
||||
"command" = "-workbench.action.terminal.toggleTerminal";
|
||||
"when" = "terminal.active";
|
||||
}
|
||||
];
|
||||
|
||||
userSettings = {
|
||||
"window.zoomLevel" = 2;
|
||||
"window.menuBarVisibility" = "toggle";
|
||||
|
||||
"workbench.colorTheme" = "Poimandres Alternate";
|
||||
"workbench.startupEditor" = "none";
|
||||
|
||||
"editor.fontFamily" = "FiraCode NF, FiraCode Nerd Font";
|
||||
"editor.fontLigatures" = true;
|
||||
"editor.cursorBlinking" = "smooth";
|
||||
"editor.minimap.enabled" = false;
|
||||
|
||||
"terminal.integrated.fontFamily" = "FiraCode NF, FiraCode Nerd Font , FiraCode";
|
||||
};
|
||||
|
||||
extensions =
|
||||
(with pkgs.vscode-extensions; [
|
||||
wakatime.vscode-wakatime
|
||||
ms-dotnettools.csharp
|
||||
naumovs.color-highlight
|
||||
ms-vscode-remote.remote-containers
|
||||
ms-azuretools.vscode-docker
|
||||
mikestead.dotenv
|
||||
golang.go
|
||||
wix.vscode-import-cost
|
||||
sumneko.lua
|
||||
yzhang.markdown-all-in-one
|
||||
jnoortheen.nix-ide
|
||||
esbenp.prettier-vscode
|
||||
prisma.prisma
|
||||
ms-python.python
|
||||
ms-vscode-remote.remote-ssh
|
||||
humao.rest-client
|
||||
bradlc.vscode-tailwindcss
|
||||
gruntfuggly.todo-tree
|
||||
])
|
||||
++ (with pkgs.vscode-marketplace; [
|
||||
danielpriestley.poimandres-alternate
|
||||
pufferbommy.pretty-poimandres
|
||||
yoavbls.pretty-ts-errors
|
||||
formulahendry.auto-rename-tag
|
||||
chakrounanas.turbo-console-log
|
||||
streetsidesoftware.code-spell-checker
|
||||
]);
|
||||
};
|
||||
};
|
||||
}
|
||||
31
modules/home/wezterm/default.nix
Normal file
@@ -0,0 +1,31 @@
|
||||
{
|
||||
inputs,
|
||||
pkgs,
|
||||
...
|
||||
}: {
|
||||
programs.wezterm = {
|
||||
enable = true;
|
||||
package = inputs.wezterm-flake.packages."${pkgs.system}".default;
|
||||
enableZshIntegration = false;
|
||||
|
||||
extraConfig = ''
|
||||
local wezterm = require 'wezterm'
|
||||
local config = {}
|
||||
|
||||
config.window_close_confirmation = 'NeverPrompt'
|
||||
config.color_scheme = 'Poimandres'
|
||||
config.colors = {
|
||||
background = "#0f0f0f"
|
||||
}
|
||||
config.enable_tab_bar = false
|
||||
config.font = wezterm.font_with_fallback {
|
||||
'JetBrainsMono Nerd Font',
|
||||
}
|
||||
config.font_size = 14.0
|
||||
config.window_background_opacity = 1
|
||||
config.audible_bell = "Disabled"
|
||||
|
||||
return config
|
||||
'';
|
||||
};
|
||||
}
|
||||
65
modules/nixos/desktop/awesome/default.nix
Executable file
@@ -0,0 +1,65 @@
|
||||
{
|
||||
lib,
|
||||
pkgs,
|
||||
...
|
||||
}: {
|
||||
services = {
|
||||
displayManager = {
|
||||
defaultSession = "none+awesome";
|
||||
ly.enable = true;
|
||||
};
|
||||
|
||||
xserver = {
|
||||
enable = true;
|
||||
windowManager.awesome = {
|
||||
enable = true;
|
||||
luaModules = lib.attrValues {
|
||||
inherit
|
||||
(pkgs.luajitPackages)
|
||||
lgi
|
||||
ldbus
|
||||
luadbi-mysql
|
||||
luaposix
|
||||
dkjson
|
||||
;
|
||||
};
|
||||
};
|
||||
};
|
||||
|
||||
acpid.enable = true;
|
||||
picom.enable = true;
|
||||
upower.enable = true;
|
||||
blueman.enable = true;
|
||||
};
|
||||
|
||||
programs.dconf.enable = true;
|
||||
|
||||
environment.systemPackages = with pkgs; [
|
||||
luajit
|
||||
acpi
|
||||
linuxKernel.packages.linux_zen.acpi_call
|
||||
lxappearance
|
||||
inotify-tools
|
||||
polkit_gnome
|
||||
xdotool
|
||||
xclip
|
||||
xorg.xbacklight
|
||||
gpick
|
||||
alsa-utils
|
||||
pavucontrol
|
||||
brightnessctl
|
||||
libnotify
|
||||
feh
|
||||
maim
|
||||
mpdris2
|
||||
python311Packages.mutagen
|
||||
xdg-utils
|
||||
playerctl
|
||||
pulsemixer
|
||||
easyeffects
|
||||
procps
|
||||
sct
|
||||
slop
|
||||
sddm-sugar-dark
|
||||
];
|
||||
}
|
||||
13
modules/nixos/desktop/default.nix
Normal file
@@ -0,0 +1,13 @@
|
||||
{...}: {
|
||||
xdg.mime = {
|
||||
enable = true;
|
||||
defaultApplications = {
|
||||
"application/pdf" = ["brave-browser.desktop"];
|
||||
"text/html" = ["brave-browser.desktop"];
|
||||
"x-scheme-handler/http" = ["brave-browser.desktop"];
|
||||
"x-scheme-handler/https" = ["brave-browser.desktop"];
|
||||
"x-scheme-handler/about" = ["brave-browser.desktop"];
|
||||
"x-scheme-handler/unknown" = ["brave-browser.desktop"];
|
||||
};
|
||||
};
|
||||
}
|
||||
7
modules/nixos/desktop/hyprland/default.nix
Normal file
@@ -0,0 +1,7 @@
|
||||
{pkgs, ...}: {
|
||||
programs.hyprland = {
|
||||
enable = true;
|
||||
package = pkgs.hyprland-git.hyprland;
|
||||
portalPackage = pkgs.hyprland-git.xdg-desktop-portal-hyprland;
|
||||
};
|
||||
}
|
||||
32
modules/nixos/fail2ban.nix
Normal file
@@ -0,0 +1,32 @@
|
||||
{config, ...}: let
|
||||
isFirewallEnabled = config.networking.firewall.enable;
|
||||
in {
|
||||
services.fail2ban = {
|
||||
enable = isFirewallEnabled;
|
||||
maxretry = 5;
|
||||
banaction = "iptables-multiport[blocktype=DROP]";
|
||||
ignoreIP = [
|
||||
"127.0.0.0/8"
|
||||
"10.0.0.0/8"
|
||||
"192.168.0.0/16"
|
||||
];
|
||||
bantime = "24h";
|
||||
|
||||
bantime-increment = {
|
||||
enable = true;
|
||||
rndtime = "12m";
|
||||
overalljails = true;
|
||||
multipliers = "4 8 16 32 64 128 256 512 1024 2048";
|
||||
maxtime = "192h";
|
||||
};
|
||||
|
||||
jails = {
|
||||
sshd.settings = {
|
||||
enabled = true;
|
||||
port = toString config.services.openssh.ports;
|
||||
mode = "aggressive";
|
||||
filter = "sshd";
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
69
modules/nixos/networking/ssh.nix
Normal file
@@ -0,0 +1,69 @@
|
||||
{
|
||||
config,
|
||||
lib,
|
||||
...
|
||||
}:
|
||||
with lib; let
|
||||
cfg = config.tux.services.openssh;
|
||||
|
||||
# Sops needs acess to the keys before the persist dirs are even mounted; so
|
||||
# just persisting the keys won't work, we must point at /persist
|
||||
hasOptinPersistence = config.environment.persistence."/persist".enable;
|
||||
in {
|
||||
options.tux.services.openssh = {
|
||||
enable = mkEnableOption "Enable OpenSSH server";
|
||||
|
||||
ports = mkOption {
|
||||
type = types.listOf types.port;
|
||||
default = [22];
|
||||
description = ''
|
||||
Specifies on which ports the SSH daemon listens.
|
||||
'';
|
||||
};
|
||||
};
|
||||
|
||||
config = mkIf cfg.enable {
|
||||
services.openssh = {
|
||||
enable = true;
|
||||
startWhenNeeded = true;
|
||||
allowSFTP = true;
|
||||
ports = cfg.ports;
|
||||
|
||||
settings = {
|
||||
PermitRootLogin = "no";
|
||||
PasswordAuthentication = false;
|
||||
KbdInteractiveAuthentication = false;
|
||||
AuthenticationMethods = "publickey";
|
||||
PubkeyAuthentication = "yes";
|
||||
ChallengeResponseAuthentication = "no";
|
||||
UsePAM = false;
|
||||
UseDns = false;
|
||||
X11Forwarding = false;
|
||||
KexAlgorithms = [
|
||||
"curve25519-sha256"
|
||||
"curve25519-sha256@libssh.org"
|
||||
"diffie-hellman-group16-sha512"
|
||||
"diffie-hellman-group18-sha512"
|
||||
"sntrup761x25519-sha512@openssh.com"
|
||||
"diffie-hellman-group-exchange-sha256"
|
||||
"mlkem768x25519-sha256"
|
||||
"sntrup761x25519-sha512"
|
||||
];
|
||||
Macs = [
|
||||
"hmac-sha2-512-etm@openssh.com"
|
||||
"hmac-sha2-256-etm@openssh.com"
|
||||
"umac-128-etm@openssh.com"
|
||||
];
|
||||
ClientAliveCountMax = 5;
|
||||
ClientAliveInterval = 60;
|
||||
};
|
||||
|
||||
hostKeys = [
|
||||
{
|
||||
path = "${lib.optionalString hasOptinPersistence "/persist"}/etc/ssh/ssh_host_ed25519_key";
|
||||
type = "ed25519";
|
||||
}
|
||||
];
|
||||
};
|
||||
};
|
||||
}
|
||||
8
modules/nixos/selfhosted/adguard.nix
Normal file
@@ -0,0 +1,8 @@
|
||||
{...}: {
|
||||
services = {
|
||||
adguardhome = {
|
||||
enable = true;
|
||||
openFirewall = true;
|
||||
};
|
||||
};
|
||||
}
|
||||
61
modules/nixos/selfhosted/containers/cs2.nix
Normal file
@@ -0,0 +1,61 @@
|
||||
{config, ...}: {
|
||||
virtualisation.oci-containers.containers.cs2-server = {
|
||||
image = "joedwards32/cs2";
|
||||
environmentFiles = [
|
||||
config.sops.secrets."cs2_secrets/SRCDS_TOKEN".path
|
||||
config.sops.secrets."cs2_secrets/CS2_RCONPW".path
|
||||
config.sops.secrets."cs2_secrets/CS2_PW".path
|
||||
];
|
||||
|
||||
environment = {
|
||||
# Server configuration
|
||||
STEAMAPPVALIDATE = "0";
|
||||
CS2_SERVERNAME = "tux's CS-2 Server";
|
||||
CS2_CHEATS = "0";
|
||||
CS2_PORT = "27015";
|
||||
CS2_SERVER_HIBERNATE = "1";
|
||||
CS2_RCON_PORT = "";
|
||||
CS2_LAN = "0";
|
||||
CS2_MAXPLAYERS = "10";
|
||||
CS2_ADDITIONAL_ARGS = "";
|
||||
CS2_CFG_URL = "";
|
||||
# Game modes
|
||||
CS2_GAMEALIAS = "competitive";
|
||||
CS2_GAMETYPE = "0";
|
||||
CS2_GAMEMODE = "1";
|
||||
CS2_MAPGROUP = "mg_active";
|
||||
CS2_STARTMAP = "de_mirage";
|
||||
# Workshop Maps
|
||||
CS2_HOST_WORKSHOP_COLLECTION = "";
|
||||
CS2_HOST_WORKSHOP_MAP = "";
|
||||
# Bots
|
||||
CS2_BOT_DIFFICULTY = "3";
|
||||
CS2_BOT_QUOTA = "";
|
||||
CS2_BOT_QUOTA_MODE = "";
|
||||
# TV
|
||||
TV_AUTORECORD = "0";
|
||||
TV_ENABLE = "0";
|
||||
TV_PORT = "27020";
|
||||
TV_PW = "changeme";
|
||||
TV_RELAY_PW = "changeme";
|
||||
TV_MAXRATE = "0";
|
||||
TV_DELAY = "0";
|
||||
# Logs
|
||||
CS2_LOG = "on";
|
||||
CS2_LOG_MONEY = "0";
|
||||
CS2_LOG_DETAIL = "0";
|
||||
CS2_LOG_ITEMS = "0";
|
||||
};
|
||||
volumes = [
|
||||
"cs2:/home/steam/cs2-dedicated"
|
||||
];
|
||||
ports = [
|
||||
"27015:27015/tcp"
|
||||
"27015:27015/udp"
|
||||
"27020:27020/udp"
|
||||
];
|
||||
extraOptions = [
|
||||
"--interactive"
|
||||
];
|
||||
};
|
||||
}
|
||||
86
modules/nixos/selfhosted/cyber-tux.nix
Normal file
@@ -0,0 +1,86 @@
|
||||
{
|
||||
config,
|
||||
lib,
|
||||
pkgs,
|
||||
...
|
||||
}:
|
||||
with lib; let
|
||||
cfg = config.tux.services.cyber-tux;
|
||||
in {
|
||||
options.tux.services.cyber-tux = {
|
||||
enable = mkEnableOption "Enable CyberTux Discord bot";
|
||||
|
||||
user = mkOption {
|
||||
type = types.str;
|
||||
default = "cyber-tux";
|
||||
description = "User under which the CyberTux service runs.";
|
||||
};
|
||||
|
||||
group = mkOption {
|
||||
type = types.str;
|
||||
default = "cyber-tux";
|
||||
description = "Group under which the CyberTux service runs.";
|
||||
};
|
||||
|
||||
environmentFile = mkOption {
|
||||
type = types.path;
|
||||
description = "Environment file containing DISCORD_TOKEN";
|
||||
};
|
||||
};
|
||||
|
||||
config = mkIf cfg.enable {
|
||||
systemd.services = {
|
||||
cyber-tux = {
|
||||
description = "A discord bot for my server";
|
||||
after = ["network.target"];
|
||||
wantedBy = ["multi-user.target"];
|
||||
|
||||
serviceConfig = {
|
||||
Type = "simple";
|
||||
User = "cyber-tux";
|
||||
Group = "cyber-tux";
|
||||
EnvironmentFile = cfg.environmentFile;
|
||||
ExecStart = getExe pkgs.cyber-tux;
|
||||
Restart = "always";
|
||||
|
||||
LockPersonality = true;
|
||||
MemoryDenyWriteExecute = true;
|
||||
NoNewPrivileges = true;
|
||||
PrivateDevices = true;
|
||||
PrivateIPC = true;
|
||||
PrivateTmp = true;
|
||||
PrivateUsers = true;
|
||||
ProtectClock = true;
|
||||
ProtectControlGroups = true;
|
||||
ProtectHome = true;
|
||||
ProtectHostname = true;
|
||||
ProtectKernelLogs = true;
|
||||
ProtectKernelModules = true;
|
||||
ProtectKernelTunables = true;
|
||||
ProtectProc = "invisible";
|
||||
ProtectSystem = "strict";
|
||||
RestrictNamespaces = "uts ipc pid user cgroup";
|
||||
RestrictRealtime = true;
|
||||
RestrictSUIDSGID = true;
|
||||
SystemCallArchitectures = "native";
|
||||
SystemCallFilter = ["@system-service"];
|
||||
UMask = "0077";
|
||||
};
|
||||
};
|
||||
};
|
||||
# Ensure the user and group exist
|
||||
users.users = mkIf (cfg.user == "cyber-tux") {
|
||||
${cfg.user} = {
|
||||
isSystemUser = true;
|
||||
group = cfg.group;
|
||||
description = "CyberTux service user";
|
||||
home = "/var/lib/cyber-tux";
|
||||
createHome = true;
|
||||
};
|
||||
};
|
||||
|
||||
users.groups = mkIf (cfg.group == "cyber-tux") {
|
||||
${cfg.group} = {};
|
||||
};
|
||||
};
|
||||
}
|
||||
29
modules/nixos/selfhosted/gitea.nix
Normal file
@@ -0,0 +1,29 @@
|
||||
{lib, ...}: {
|
||||
services = {
|
||||
gitea = {
|
||||
enable = true;
|
||||
settings = {
|
||||
service.DISABLE_REGISTRATION = true;
|
||||
server = {
|
||||
DOMAIN = "git.tux.rs";
|
||||
ROOT_URL = "https://git.tux.rs";
|
||||
};
|
||||
};
|
||||
};
|
||||
|
||||
nginx = {
|
||||
enable = lib.mkForce true;
|
||||
virtualHosts = {
|
||||
"git.tux.rs" = {
|
||||
forceSSL = true;
|
||||
useACMEHost = "tux.rs";
|
||||
locations = {
|
||||
"/" = {
|
||||
proxyPass = "http://localhost:3000";
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
43
modules/nixos/selfhosted/glance/default.nix
Normal file
@@ -0,0 +1,43 @@
|
||||
{
|
||||
username,
|
||||
lib,
|
||||
config,
|
||||
...
|
||||
}: let
|
||||
home = import ./home.nix;
|
||||
in {
|
||||
services = {
|
||||
glance = {
|
||||
enable = true;
|
||||
openFirewall = true;
|
||||
settings = {
|
||||
server = {
|
||||
host = "0.0.0.0";
|
||||
port = 5678;
|
||||
};
|
||||
branding = {
|
||||
custom-footer = "<p><a href='https://tux.rs'>${username}</a></p>";
|
||||
};
|
||||
pages = [
|
||||
home.page
|
||||
];
|
||||
};
|
||||
};
|
||||
|
||||
nginx = {
|
||||
enable = lib.mkForce true;
|
||||
virtualHosts = {
|
||||
"home.tux.rs" = {
|
||||
forceSSL = true;
|
||||
useACMEHost = "tux.rs";
|
||||
locations = {
|
||||
"/" = {
|
||||
proxyPass = "http://${config.services.glance.settings.server.host}:${toString config.services.glance.settings.server.port}";
|
||||
proxyWebsockets = true;
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
};
|
||||
}
|
||||
86
modules/nixos/selfhosted/glance/home.nix
Normal file
@@ -0,0 +1,86 @@
|
||||
{
|
||||
page = {
|
||||
name = "Dashboard - tux";
|
||||
width = "slim";
|
||||
hide-desktop-navigation = true;
|
||||
center-vertically = true;
|
||||
columns = [
|
||||
{
|
||||
size = "full";
|
||||
widgets = [
|
||||
{
|
||||
type = "search";
|
||||
autofocus = true;
|
||||
}
|
||||
{
|
||||
type = "markets";
|
||||
markets = [
|
||||
{
|
||||
symbol = "BTC-USD";
|
||||
name = "Bitcoin";
|
||||
chart-link = "https://www.tradingview.com/chart/?symbol=INDEX:BTCUSD";
|
||||
}
|
||||
{
|
||||
symbol = "ETH-USD";
|
||||
name = "Ethereum";
|
||||
chart-link = "https://www.tradingview.com/chart/?symbol=INDEX:ETHUSD";
|
||||
}
|
||||
{
|
||||
symbol = "SOL-USD";
|
||||
name = "Solana";
|
||||
chart-link = "https://www.tradingview.com/chart/?symbol=INDEX:SOLUSD";
|
||||
}
|
||||
];
|
||||
}
|
||||
{
|
||||
type = "monitor";
|
||||
cache = "1m";
|
||||
title = "Services";
|
||||
sites = [
|
||||
{
|
||||
title = "Gitea";
|
||||
url = "https://git.tux.rs";
|
||||
icon = "si:gitea";
|
||||
}
|
||||
{
|
||||
title = "Vaultwarden";
|
||||
url = "https://bw.tux.rs";
|
||||
icon = "si:vaultwarden";
|
||||
}
|
||||
{
|
||||
title = "Ntfy";
|
||||
url = "https://ntfy.tux.rs";
|
||||
icon = "si:ntfy";
|
||||
}
|
||||
{
|
||||
title = "Grafana";
|
||||
url = "https://grafana.tux.rs";
|
||||
icon = "si:grafana";
|
||||
}
|
||||
{
|
||||
title = "SearXNG";
|
||||
url = "https://sx.tux.rs";
|
||||
icon = "si:searxng";
|
||||
}
|
||||
{
|
||||
title = "Wakapi";
|
||||
url = "https://wakapi.tux.rs";
|
||||
icon = "si:wakatime";
|
||||
}
|
||||
];
|
||||
}
|
||||
{
|
||||
type = "reddit";
|
||||
subreddit = "selfhosted";
|
||||
style = "horizontal-cards";
|
||||
}
|
||||
{
|
||||
type = "reddit";
|
||||
subreddit = "homelab";
|
||||
style = "horizontal-cards";
|
||||
}
|
||||
];
|
||||
}
|
||||
];
|
||||
};
|
||||
}
|
||||